Abstract
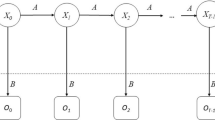
The malware uses morphological and polymorphic methods to evade detection, traditional malware recognition methods have gradually failed to cope with large and variable malware. To overcome drawbacks of static or dynamic analysis techniques, we merge the static and dynamic features as a new feature vector and form a feature matrix. In order to handle the effects of feature interactions we build a model for the interaction between tow feature vector in an efficient and effective manner, and apply Factorization Machine (FM) as the final classifier for malware classification because it can handle the feature sparsity effectively. The experimental results show that the method has a high accuracy for malware classification and a low false negative rate for malicious and benign dataset.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Addressing big data security challenges: the right tools for smart protection (2012). http://www.trendmicro.com/cloud-content/us/pdfs/business/white-papers/wp_addressing-big-data-security-challenges.pdf
AV-TEST: The independent IT-security institute (2019). https://www.av-test.org/en/statistics/malware/
Tian, R., Batten, L., Islam, R., Versteeg, S.: An automated classification system based on the strings of trojan and virus families. In: 4th International Conference on Malicious and Unwanted Software (MALWARE), pp. 23–30. IEEE (2009)
Islam, R., Tian, R., Batten, L., Versteeg, S.: Classification of malware based on string and function feature selection. In: Second Cybercrime and Trustworthy Computing Workshop, pp. 9–17. IEEE (2010)
Galal, H.S., Mahdy, Y.B., Atiea, M.A.: Behavior-based features model for malware detection. J. Comput. Virol. Hacking Tech. 12(2), 59–67 (2015). https://doi.org/10.1007/s11416-015-0244-0
Liu, J., Zeng, Y., Shi, J., Yang, Y., Wang, R., He, L.: MalDetect: a structure of encrypted malware traffic detection. Comput. Mater. Continua. 60(2), 721–739 (2019)
Wang, Y., et al.: YATA: yet another proposal for traffic analysis and anomaly detection. Comput. Mater. Continua. 60(3), 1171–1187 (2019)
Tan, L., Li, C., Xia, J., Cao, J.: Application of self-organizing feature map neural network based on K-means clustering in network intrusion detection. Comput. Mater. Continua 61(1), 275–288 (2019)
Islam, R., Tian, R., Batten, L.M., Versteeg, S.: Classification of malware based on integrated static and dynamic features. J. Netw. Comput. Appl. 36(2), 646–656 (2013)
Shijo, P.V., Salim, A.: Integrated static and dynamic analysis for malware detection. Procedia Comput. Sci. 46, 804–811 (2015)
Juan, Y., Zhuang, Y., Chin, W.-S., Lin, C.-J.: Field-aware factorization machines for CTR prediction. In: Proceedings of the 10th ACM Conference on Recommender Systems, pp. 43–50. ACM (2016)
Jang, J.W., Woo, J., Mohaisen, A., Yun, J., Kim, H.K.: Mal-netminer: malware classification approach based on social network analysis of system call graph. Math. Prob. Eng. (2015)
Rendle, S.: Factorization machines. In: IEEE International Conference on Data Mining, pp. 995–1000, IEEE (2010)
Rendle, S.: Factorization machines with libfm. ACM Trans. Intell. Syst. Technol. (TIST). 3(3), 1–22 (2012)
VirusShare. https://virusshare.com/
MalwareBlackList. http://malwareblacklist.com/
Hacking and Countermeasure Research Lab. http://ocslab.hksecurity.net/mal_netminer/download-malnet-miner/
Acknowledgments
This work is supported by Natural Science Foundation of China (NSFC), under grant number 61300220 and 61370227, and by Natural Science Foundation of Hunan Province of China, under grant number 2017JJ2100.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Long, H., Li, Z., Jiang, F. (2020). Malware Classifications Based on Static-Dynamic Features and Factorization Machines. In: Sun, X., Wang, J., Bertino, E. (eds) Artificial Intelligence and Security. ICAIS 2020. Communications in Computer and Information Science, vol 1254. Springer, Singapore. https://doi.org/10.1007/978-981-15-8101-4_23
Download citation
DOI: https://doi.org/10.1007/978-981-15-8101-4_23
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-8100-7
Online ISBN: 978-981-15-8101-4
eBook Packages: Computer ScienceComputer Science (R0)