Abstract
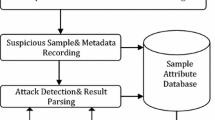
A lot of HTTP traffics are unnoticed to users because they are automatically generated from software. This caused by HTTP protocol characteristics. For the purpose of communication with servers, HTTP-based applications always automatically and actively send requests to their hosts because HTTPs are designed as connectionless protocols. In addition, all kinds of HTTP communications from software such as a bot, adware, and normal web accesses are mixed clearly. This raises the requirement for clarification of HTTP traffics. Most previous studies concentrated on HTTP-based malicious bot traffics, however, graywares such as adware or unauthorized applications are also becoming serious internal threats since they can stealth sensitive information or web usage experiences from infected systems. In this study, a new method for clustering and identifying HTTP communications is proposed. It focuses on analyzing of HTTP-based software Internet access behaviors. The method is tested with real outbound HTTP communication of a private network. Examination showed improved results with an accuracy rate of 91.18% in clustering and identifying HTTP automated communications.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Dietrich CJ, Rossow C, Pohlmann N (2013) CoCoSpot: clustering and recognizing botnet command and control channels using traffic analysis. Comput Netw 57(2):475–486
AsSadhan B, Moura JMF (2014) An efficient method to detect periodic behavior in botnet traffic by analyzing control plane traffic. J Adv Res 5(4):435–448
Tran MC, Nakamura Y (2016) Classification of HTTP automated software communication behavior using a NoSQL database. IEIE Trans Smart Process Comput 5(2):94–99
Oberheide J, Cooke E, Jahanian F (2008) Cloudav: N-version antivirus in the network cloud. In: Proceedings of the 17th USENIX conference on security symposium, pp 91–106
Rajab MA, Ballard L, Lutz N, Mavrommatis P, Provos N (2013) CAMP: content-agnostic malware protection. In: Proceedings of 20th annual network and distributed system security symposium (NDSS)
Dubuisson M-P, Jain AK (1994) A modified Hausdorff distance for object matching. In: Proceedings of the 12th IAPR international conference, vol 1, pp 566–568
Ester M, Kriegel H-P, Sander J, Xu X (1996) A density-based algorithm for discovering clusters in large spatial databases with noise. In: Proceedings of the second international conference on knowledge discovery and data mining (KDD-96), pp 226–231
VirusTotal. http://virustotal.com/. Last Accessed Feb 2019
McAfee Web Gateway. http://www.mcafee.com/us/products/web-gateway.aspx. Last Accessed Feb 2019
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Tran, M.C., Thi, N.Q., Tien, N.T., Phuc, N.X., Minh, N.H. (2020). A Research on Clustering and Identifying Automated Communication in the HTTP Environment. In: Solanki, V., Hoang, M., Lu, Z., Pattnaik, P. (eds) Intelligent Computing in Engineering. Advances in Intelligent Systems and Computing, vol 1125. Springer, Singapore. https://doi.org/10.1007/978-981-15-2780-7_111
Download citation
DOI: https://doi.org/10.1007/978-981-15-2780-7_111
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-15-2779-1
Online ISBN: 978-981-15-2780-7
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)