Abstract
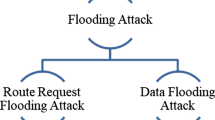
RREQ Flood Attack is one of the prominent attack in Wireless Adhoc Network. In the flood attack, a malicious node fills up all the routing tables with its own packets and hence communication between source and destination becomes paralyzed. To secure against flooding attack, a mitigation scheme is proposed which uses Time to Live value to mark and remove the malicious node that floods the network. In the proposed scheme, RREQ limit is set which is dynamically checked after certain period so that the flood attack does not occur. The Simulation of the proposed scheme is done by Qualnet and the result shows that the scheme prevents the flooding attack, reduces the end-to-end delay and increases the throughput.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Balakrishnan, V., Varadhrajan, V., Tupakula, U.: Mitigating flooding attacks in mobile ad-hoc networks supporting anonymous communications. In: Wireless Broadband and Ultra Wideband Communications, vol. 2, p. 29 (2007)
Bandyopadhyay, A., Vuppala, S., Choudhury, P.: A simulation analysis of flooding attack in MANET using NS-3. In: Wireless Communication, Vehicular Technology, Information Theory and Aerospace & Electronic Systems Technology (Wireless VITAE), pp. 1–5 (2011)
Chauhan, N., Yadav, S.: Flooding attacks prevention in MANET. Int. J. Comput. Technol. Electron. Eng. 1(3), 68–72 (2011)
Choudhury, P., Nandi, S., Paul, A., Debnath, N.: Mitigating route request flooding attack in MANET using node reputation. In: IEEE 10th International Conference on Industrial Informatics, vol. 10, pp. 1010–1015 (2012)
Guo, Y., Perreau, S.: Trace flooding attack in mobile ad hoc networks. In: International Conference on Intelligent Sensors, Sensors Networks and Information, vol. 3, pp. 329–334 (2007)
Kum, D., Le, A., Cho, Y., Toh, C., Lee, I.: An efficient on-demand routing approach with directional flooding for wireless mesh networks. J. Commun. Netw. 2(1), 67–73 (2010)
Li, M., Li, J.: Simulation study of flood attacking of DDOS. In: International Conference on Internet Computing in Science and Engineering, pp. 286–293 (2008)
Pires, W., Figueiredo, T., Wong, H., Loureiro, A.: Malicious node detection in wireless sensor networks. In: Proceedings of the 18th International Parallel and Distributed Processing Symposium, vol. 18, p. 24 (2004)
Song, J., Hong, F., Zhang, Y.: Effective filtering scheme against RREQ flooding attack in mobile ad hoc networks. In: Proceedings of the 7th International Conference on Parallel and Distributed Computing, Applications and Technologies, vol. 7, pp. 497–502 (2006)
Venkatraman, R., Pushpalatha, M., RamaRao, T.: Performance analysis of flooding attack, prevention algorithm in MANETs. Int. J. Comput. Electr. Autom. Control Inf. Eng. 3(8), 2056–2059 (2009)
Yi, P., Dai, Z., Zhong, Y., Zhang, Z.: Resisting flooding attacks in ad hoc networks. In: Proceedings of the International Conference on Information Technology: Coding and Computing (ITCC 2005), vol. 2, pp. 657–662 (2005)
RFC 3561 of AODV protocol
Grover, N., Mohapatra, A.K.: Digital image authentication model based on edge adaptive steganography. In: Proceedings of the 2013 2nd International Conference on Advanced Computing, Networking and Security, pp. 238–242. IEEE Computer Society, December 2013
Khandelwal, A., Mohapatra, A.K.: An insight into the security issues and their solutions for android phones. In: 2015 2nd International Conference on Computing for Sustainable Global Development (INDIACom) (2015)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2018 Springer Nature Singapore Pte Ltd.
About this paper
Cite this paper
Rani, S., Narwal, B., Mohapatra, A.K. (2018). RREQ Flood Attack and Its Mitigation in Ad Hoc Network. In: Panda, B., Sharma, S., Roy, N. (eds) Data Science and Analytics. REDSET 2017. Communications in Computer and Information Science, vol 799. Springer, Singapore. https://doi.org/10.1007/978-981-10-8527-7_50
Download citation
DOI: https://doi.org/10.1007/978-981-10-8527-7_50
Published:
Publisher Name: Springer, Singapore
Print ISBN: 978-981-10-8526-0
Online ISBN: 978-981-10-8527-7
eBook Packages: Computer ScienceComputer Science (R0)