Abstract
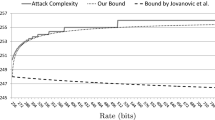
The Sponge function is known to achieve 2c/2 security, where c is its capacity. This bound was carried over to keyed variants of the function, such as SpongeWrap, to achieve a min {2c/2,2κ} security bound, with κ the key length. Similarly, many CAESAR competition submissions are designed to comply with the classical 2c/2 security bound. We show that Sponge-based constructions for authenticated encryption can achieve the significantly higher bound of min {2b/2,2c,2κ} asymptotically, with b > c the permutation size, by proving that the CAESAR submission NORX achieves this bound. Furthermore, we show how to apply the proof to five other Sponge-based CAESAR submissions: Ascon, CBEAM/STRIBOB, ICEPOLE, Keyak, and two out of the three PRIMATEs. A direct application of the result shows that the parameter choices of these submissions are overly conservative. Simple tweaks render the schemes considerably more efficient without sacrificing security. For instance, NORX64 can increase its rate and decrease its capacity by 128 bits and Ascon-128 can encrypt three times as fast, both without affecting the security level of their underlying modes in the ideal permutation model.
Chapter PDF
Similar content being viewed by others
References
CAESAR: Competition for Authenticated Encryption: Security, Applicability, and Robustness (2014), http://competitions.cr.yp.to/caesar.html
Whiting, D., Housley, R., Ferguson, N.: AES Encryption and Authentication Using CTR Mode and CBC-MAC. IEEE 802.11-02/001r2 (2002)
Rogaway, P., Bellare, M., Black, J., Krovetz, T.: OCB: a block-cipher mode of operation for efficient authenticated encryption. In: Reiter, M.K., Samarati, P. (eds.) ACM Conference on Computer and Communications Security, pp. 196–205. ACM (2001)
Rogaway, P.: Efficient instantiations of tweakable blockciphers and refinements to modes OCB and PMAC. In: Lee, P.J. (ed.) ASIACRYPT 2004. LNCS, vol. 3329, pp. 16–31. Springer, Heidelberg (2004)
Krovetz, T., Rogaway, P.: The software performance of authenticated-encryption modes. In: Joux, A. (ed.) FSE 2011. LNCS, vol. 6733, pp. 306–327. Springer, Heidelberg (2011)
Bellare, M., Rogaway, P., Wagner, D.: The EAX mode of operation. In: Roy, B., Meier, W. (eds.) FSE 2004. LNCS, vol. 3017, pp. 389–407. Springer, Heidelberg (2004)
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G.: Sponge functions. In: ECRYPT Hash Function Workshop (2007)
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G.: On the security of the keyed sponge construction. In: Symmetric Key Encryption Workshop (SKEW 2011) (2011)
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G.: Duplexing the sponge: Single-pass authenticated encryption and other applications. In: Miri, A., Vaudenay, S. (eds.) SAC 2011. LNCS, vol. 7118, pp. 320–337. Springer, Heidelberg (2012)
Aumasson, J., Jovanovic, P., Neves, S.: NORX v1 (2014), Submission to CAESAR competition
Dobraunig, C., Eichlseder, M., Mendel, F., Schläffer, M.: Ascon v1 (2014), Submission to CAESAR competition
Minaud, B.: Re: CBEAM Withdrawn as of today! (2014), CAESAR mailing list
Saarinen, M.: CBEAM r1 (2014), Submission to CAESAR competition
Saarinen, M.: CBEAM: Efficient authenticated encryption from feebly one-way φ functions. In: Benaloh (ed.) [9], pp. 251–269
Morawiecki, P., Gaj, K., Homsirikamol, E., Matusiewicz, K., Pieprzyk, J., Rogawski, M., Srebrny, M., Wójcik, M.: ICEPOLE v1 (2014), Submission to CAESAR competition
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G., Van Keer, R.: Keyak v1 (2014), Submission to CAESAR competition
Andreeva, E., Bilgin, B., Bogdanov, A., Luykx, A., Mendel, F., Mennink, B., Mouha, N., Wang, Q., Yasuda, K.: PRIMATEs v1 (2014), Submission to CAESAR competition
Saarinen, M.: Beyond modes: Building a secure record protocol from a cryptographic sponge permutation. In: Benaloh (ed.) [9], pp. 270–285
Saarinen, M.: STRIBOB r1 (2014), Submission to CAESAR competition
Saarinen, M.: Authenticated encryption from GOST R 34.11-2012 LPS permutation. In: CTCrypt 2014 (2014)
Alizadeh, J., Aref, M., Bagheri, N.: Artemia v1 (2014), Submission to CAESAR competition
Gligoroski, D., Mihajloska, H., Samardjiska, S., Jacobsen, H., El-Hadedy, M., Jensen, R.: π-Cipher v1 (2014), Submission to CAESAR competition
Bellare, M., Namprempre, C.: Authenticated encryption: Relations among notions and analysis of the generic composition paradigm. J. Cryptology 21(4), 469–491 (2008)
Iwata, T., Ohashi, K., Minematsu, K.: Breaking and repairing GCM security proofs. In: Safavi-Naini, R., Canetti, R. (eds.) CRYPTO 2012. LNCS, vol. 7417, pp. 31–49. Springer, Heidelberg (2012)
Bertoni, G., Daemen, J., Peeters, M., Van Assche, G.: Sponge-based pseudo-random number generators. In: Mangard, S., Standaert, F.-X. (eds.) CHES 2010. LNCS, vol. 6225, pp. 33–47. Springer, Heidelberg (2010)
Bellare, M., Rogaway, P.: The security of triple encryption and a framework for code-based game-playing proofs. In: Vaudenay, S. (ed.) EUROCRYPT 2006. LNCS, vol. 4004, pp. 409–426. Springer, Heidelberg (2006)
Andreeva, E., Bilgin, B., Bogdanov, A., Luykx, A., Mennink, B., Mouha, N., Yasuda, K.: APE: Authenticated permutation-based encryption for lightweight cryptography. In: Cid, C., Rechberger, C. (eds.) FSE. LNCS. Springer (2014)
Jovanovic, P., Luykx, A., Mennink, B.: Beyond 2c/2 security in sponge-based authenticated encryption modes. Cryptology ePrint Archive, Report 2014/373 (2014), Full version of this paper
Wu, H.: The Hash Function JH (2011) Submission to NIST’s SHA-3 competition
Bagheri, N.: Padding of Artemia (2014), CAESAR mailing list
Benaloh, J. (ed.): CT-RSA 2014. LNCS, vol. 8366. Springer, Heidelberg (2014)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 International Association for Cryptologic Research
About this paper
Cite this paper
Jovanovic, P., Luykx, A., Mennink, B. (2014). Beyond 2c/2 Security in Sponge-Based Authenticated Encryption Modes. In: Sarkar, P., Iwata, T. (eds) Advances in Cryptology – ASIACRYPT 2014. ASIACRYPT 2014. Lecture Notes in Computer Science, vol 8873. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-662-45611-8_5
Download citation
DOI: https://doi.org/10.1007/978-3-662-45611-8_5
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-662-45610-1
Online ISBN: 978-3-662-45611-8
eBook Packages: Computer ScienceComputer Science (R0)