Abstract
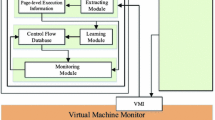
Ensuring the integrity of logs is essential to reliably detect and counteract attacks, because adversaries tamper with logs to hide their activities on a computer. Even though some research studies proposed different ways to protect log files, adversaries can tamper with logs in kernel space with kernel-level malicious software (malware). In an environment where Virtual Machines (VM) are utilized, VM Introspection (VMI) is capable of collecting logs from VMs. However, VMI is not optimized for log protection and unnecessary overhead is incurred, because VMI does not specialize in log collection. To transfer logs out of a VM securely, we propose a secure log transfer method of replacing a library. In our proposed method, a process on a VM requests a log transfer by using the modified library, which contains a trigger for a log transfer. When a VM Monitor (VMM) detects the trigger, it collects logs from the VM and sends them to another VM. The proposed method provides VM-level log isolation and security for the mechanism itself. This paper describes design, implementation, and evaluation of the proposed method.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Preview
Unable to display preview. Download preview PDF.
Similar content being viewed by others
References
Kent, K., Souppaya, M.: Guide to computer security log management, special publication 800-92 (September 2006)
spoonfork: Analysis of a rootkit: Tuxkit, http://www.ossec.net/doc/rootcheck/analysis-tuxkit.html
stealth: Announcing full functional adore-ng rootkit for 2.6 kernel, http://lwn.net/Articles/75991/
Symantec: Backdoor.lastdoor, http://www.symantec.com/security_response/writeup.jsp?docid=2002-090517-3251-99
Subashini, S., Kavitha, V.: A survey on security issues in service delivery models of cloud computing. Journal of Network and Computer Applications 34(1), 1–11 (2011)
Grobauer, B., Walloschek, T., Stocker, E.: Understanding cloud computing vulnerabilities. IEEE Security & Privacy 9(2), 50–57 (2011)
Marty, R.: Cloud application logging for forensics. In: Proceedings of the 2011 ACM Symposium on Applied Computing, SAC 2011, pp. 178–184 (2011)
Chen, P.M., Noble, B.D.: When virtual is better than real. In: Proceedings of the Eighth Workshop on Hot Topics in Operating Systems, HOTOS 2001, pp. 133–138. IEEE Computer Society (2001)
Boeck, B., Huemer, D., Tjoa, A.M.: Towards more trustable log files for digital forensics by means of “trusted computing”. In: International Conference on Advanced Information Networking and Applications, pp. 1020–1027 (2010)
Seshadri, A., Luk, M., Qu, N., Perrig, A.: Secvisor: a tiny hypervisor to provide lifetime kernel code integrity for commodity oses. SIGOPS Oper. Syst. Rev. 41(6), 335–350 (2007)
Garfinkel, T., Rosenblum, M.: A virtual machine introspection based architecture for intrusion detection. In: Proceedings of the Network and Distributed Systems Security Symposium, pp. 191–206 (2003)
Dewan, P., Durham, D., Khosravi, H., Long, M., Nagabhushan, G.: A hypervisor-based system for protecting software runtime memory and persistent storage. In: Proceedings of the 2008 Spring Simulation Multiconference, SpringSim 2008, pp. 828–835 (2008)
Sharif, M.I., Lee, W., Cui, W., Lanzi, A.: Secure in-vm monitoring using hardware virtualization. In: Proceedings of the 16th ACM Conference on Computer and Communications Security, CCS 2009, pp. 477–487 (2009)
Adiscon: rsyslogm, http://www.rsyslog.com/
Security, B.I.: Syslog server | syslog-ng logging system, http://www.balabit.com/network-security/syslog-ng
Kelsey, J., Callas, J., Clemm, A.: Signed syslog messages (May 2010), http://tools.ietf.org/html/rfc5848
New, D., Rose, M.: Reliable delivery for syslog (November 2001), http://www.ietf.org/rfc/rfc3195.txt
Dunlap, G.W., King, S.T., Cinar, S., Basrai, M.A., Chen, P.M.: Revirt: enabling intrusion analysis through virtual-machine logging and replay. SIGOPS Oper. Syst. Rev. 36(SI), 211–224 (2002)
Ibrahim, A., Hamlyn-Harris, J., Grundy, J., Almorsy, M.: Cloudsec: A security monitoring appliance for virtual machines in the iaas cloud model. In: 5th International Conference on Network and System Security, pp. 113–120 (September 2011)
Sato, M., Yamauchi, T.: Vmm-based log-tampering and loss detection scheme. Journal of Internet Technology 13(4), 655–666 (2012)
Barham, P., Dragovic, B., Fraser, K., Hand, S., Harris, T., Ho, A., Neugebauer, R., Pratt, I., Warfield, A.: Xen and the art of virtualization. SIGOPS Oper. Syst. Rev. 37(5), 164–177 (2003)
Accorsi, R.: Log data as digital evidence: What secure logging protocols have to offer? In: Proceedings of the 33rd Annual IEEE International Computer Software and Applications Conference, vol. 02, pp. 398–403 (2009)
Zhao, S., Chen, K., Zheng, W.: Secure logging for auditable file system using separate virtual machines. In: 2009 IEEE International Symposium on Parallel and Distributed Processing with Applications, pp. 153–160 (2009)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 Springer-Verlag Berlin Heidelberg
About this paper
Cite this paper
Sato, M., Yamauchi, T. (2013). Secure Log Transfer by Replacing a Library in a Virtual Machine. In: Sakiyama, K., Terada, M. (eds) Advances in Information and Computer Security. IWSEC 2013. Lecture Notes in Computer Science, vol 8231. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-41383-4_1
Download citation
DOI: https://doi.org/10.1007/978-3-642-41383-4_1
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-41382-7
Online ISBN: 978-3-642-41383-4
eBook Packages: Computer ScienceComputer Science (R0)