Abstract
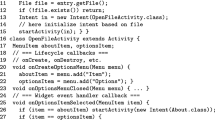
One of the famous software packages for running smart devices is Android. It is an operating system with middlewares and applications. Android runs most functioning mobile phone and tablet devices, today. On the top of the stack describing the organization of different parts of Android is the “applications” component. A main part of an Android application is activity useful for interaction with users where each activity can be realized as a single-frame user interface. An important tool for utilizing activities is that of fragment representing slices of the interface of the activity. Activities and fragments have life cycles.
This paper presents an operational semantics for precisely and efficiently modeling the state transitions within life cycles of activities and fragments. The semantics considers the effects of the transitions in both life cycles on each other. Such semantics is necessary for precisely designing important static analyses for Android applications including fragment components.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Android developers. http://developer.android.com
Arzt, S., Rasthofer, S., Fritz, C., Bodden, E., Bartel, A., Klein, J., Le Traon, Y., Octeau, D., McDaniel, P.: Flowdroid: precise context, flow, field, object-sensitive and lifecycle-aware taint analysis for android apps. ACM SIGPLAN Not. 49(6), 259–269 (2014)
Burguera, I., Zurutuza, U., Nadjm-Tehrani, S.: Crowdroid: behavior-based malware detection system for android. In: Proceedings of the 1st ACM Workshop on Security and Privacy in Smartphones and Mobile Devices, pp. 15–26. ACM (2011)
Chaudhuri, A.: Language-based security on android. In: Proceedings of the ACM SIGPLAN Fourth Workshop on Programming Languages and Analysis for Security, pp. 1–7. ACM (2009)
Android Developers. What is android (2011)
El-Zawawy, M.A.: An operational semantics for android applications. In: Gervasi, O., et al. (eds.) ICCSA 2016, Part V. LNCS, vol. 9790, pp. 100–114. Springer, Cham (2016). doi:10.1007/978-3-319-42092-9_9
El-Zawawy, M.A.: A type system for android applications. In: Gervasi, O., et al. (eds.) ICCSA 2016, Part V. LNCS, vol. 9790, pp. 115–128. Springer, Cham (2016). doi:10.1007/978-3-319-42092-9_10
Enck, W., Gilbert, P., Han, S., Tendulkar, V., Chun, B.-G., Cox, L.P., Jung, J., McDaniel, P., Sheth, A.N.: Taintdroid: an information-flow tracking system for realtime privacy monitoring on smartphones. ACM Trans. Comput. Syst. (TOCS) 32(2), 5 (2014)
Enck, W., Ongtang, M., McDaniel, P.: Understanding android security. IEEE Secur. Priv. 7(1), 50–57 (2009)
Farzan, A., Chen, F., Meseguer, J., Roşu, G.: Formal analysis of java programs in JavaFAN. In: Alur, R., Peled, D.A. (eds.) CAV 2004. LNCS, vol. 3114, pp. 501–505. Springer, Heidelberg (2004). doi:10.1007/978-3-540-27813-9_46
Felt, A.P., Chin, E., Hanna, S., Song, D., Wagner, D.: Android permissions demystified. In: Proceedings of the 18th ACM Conference on Computer and Communications Security, pp. 627–638. ACM (2011)
Gibler, C., Crussell, J., Erickson, J., Chen, H.: AndroidLeaks: automatically detecting potential privacy leaks in android applications on a large scale. In: Katzenbeisser, S., Weippl, E., Camp, L.J., Volkamer, M., Reiter, M., Zhang, X. (eds.) Trust 2012. LNCS, vol. 7344, pp. 291–307. Springer, Heidelberg (2012). doi:10.1007/978-3-642-30921-2_17
Jeon, J., Micinski, K.K., Foster, J.S.: Symdroid: Symbolic execution for dalvik bytecode. Technical report (2012)
Payet, E., Spoto, F.: An operational semantics for android activities. In: Proceedings of the ACM SIGPLAN 2014 Workshop on Partial Evaluation and Program Manipulation, pp. 121–132. ACM (2014)
Spreitzenbarth, M., Freiling, F., Echtler, F., Schreck, T., Hoffmann, J.: Mobile-sandbox: having a deeper look into android applications. In: Proceedings of the 28th Annual ACM Symposium on Applied Computing, pp. 1808–1815. ACM (2013)
Wu, D.-J., Mao, C.-H., Wei, T.-E., Lee, H.-M., Wu, K.-P.: Droidmat: android malware detection through manifest and API calls tracing. In: 2012 Seventh Asia Joint Conference on Information Security (Asia JCIS), pp. 62–69. IEEE (2012)
Yan, L.-K., Yin, H.: Droidscope: seamlessly reconstructing the os and dalvik semantic views for dynamic android malware analysis. In: USENIX Security Symposium, pp. 569–584 (2012)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2017 Springer International Publishing AG
About this paper
Cite this paper
El-Zawawy, M.A. (2017). Modeling Android Fragments and Activities Life Cycles Coordination. In: Gervasi, O., et al. Computational Science and Its Applications – ICCSA 2017. ICCSA 2017. Lecture Notes in Computer Science(), vol 10408. Springer, Cham. https://doi.org/10.1007/978-3-319-62404-4_46
Download citation
DOI: https://doi.org/10.1007/978-3-319-62404-4_46
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-62403-7
Online ISBN: 978-3-319-62404-4
eBook Packages: Computer ScienceComputer Science (R0)