Abstract
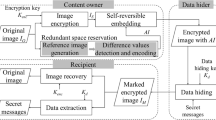
We present an end-to-end learned image data hiding framework that embeds and extracts secrets in the latent representations of a neural compressor. The message encoder/decoder design is flexible to support multiples of 64-bit message lengths. We jointly optimize with the rate-distortion function of the neural codec, which reduces the embedded size overhead significantly. By leveraging a perceptual loss function, our approach simultaneously achieves high image quality and low bit-error rate. Our approach offers superior image secrecy in steganography and watermarking scenarios than existing techniques. Processing messages in the compressed domain has much lower complexity, and our method can achieve about 30 times acceleration. Furthermore, with the prevalence of IoT smart devices, machines can extract hidden data directly from the compressed domain without decoding. Our framework can benefit both secure communication and the coding-for-machines concept.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Agustsson, E., Timofte, R.: Ntire 2017 challenge on single image super-resolution: Dataset and study. In: The IEEE Conference on Computer Vision and Pattern Recognition (CVPR) Workshops, June 2017
Ballé, J., Minnen, D., Singh, S., Hwang, S.J., Johnston, N.: Variational image compression with a scale hyperprior. arXiv preprint arXiv:1802.01436 (2018)
Baluja, S.: Hiding images in plain sight: deep steganography. Adv. Neural. Inf. Process. Syst. 30, 2069–2079 (2017)
Bégaint, J., Racapé, F., Feltman, S., Pushparaja, A.: Compressai: a pytorch library and evaluation platform for end-to-end compression research. arXiv preprint arXiv:2011.03029 (2020)
Bi, N., Sun, Q., Huang, D., Yang, Z., Huang, J.: Robust image watermarking based on multiband wavelets and empirical mode decomposition. IEEE Trans. Image Process. 16(8), 1956–1966 (2007)
Boehm, B.: Stegexpose-a tool for detecting lsb steganography. arXiv preprint arXiv:1410.6656 (2014)
Boroumand, M., Chen, M., Fridrich, J.: Deep residual network for steganalysis of digital images. IEEE Trans. Inf. Forensics Secur. 14(5), 1181–1193 (2018)
Bose, R.C., Ray-Chaudhuri, D.K.: On a class of error correcting binary group codes. Inf. Control 3(1), 68–79 (1960)
Chen, T., Liu, H., Ma, Z., Shen, Q., Cao, X., Wang, Y.: End-to-end learnt image compression via non-local attention optimization and improved context modeling. IEEE Trans. Image Process. 30, 3179–3191 (2021)
Cheng, Z., Sun, H., Takeuchi, M., Katto, J.: Learned image compression with discretized gaussian mixture likelihoods and attention modules. In: CVPR, pp. 7939–7948 (2020)
Choi, K., Tatwawadi, K., Grover, A., Weissman, T., Ermon, S.: Neural joint source-channel coding. In: International Conference on Machine Learning, pp. 1182–1192. PMLR (2019)
Duan, Z., Ma, Z., Zhu, F.: Unified architecture adaptation for compressed domain semantic inference. IEEE Trans. Circuits Syst. Video Technol. (2023)
Fridrich, J., Pevny, T., Kodovsky, J.: Statistically undetectable jpeg steganography: dead ends challenges, and opportunities. In: Proceedings of the 9th Workshop on Multimedia & Security, pp. 3–14 (2007)
Holub, V., Fridrich, J., Denemark, T.: Universal distortion function for steganography in an arbitrary domain. EURASIP J. Inf. Secur. 2014(1), 1–13 (2014)
Jing, J., Deng, X., Xu, M., Wang, J., Guan, Z.: Hinet: deep image hiding by invertible network. In: Proceedings of the IEEE/CVF International Conference on Computer Vision, pp. 4733–4742 (2021)
Kodak photocd dataset. https://r0k.us/graphics/kodak/
Lainema, J., Hannuksela, M.M., Vadakital, V.K.M., Aksu, E.B.: Hevc still image coding and high efficiency image file format. In: 2016 IEEE International Conference on Image Processing (ICIP), pp. 71–75. IEEE (2016)
Lerch-Hostalot, D., Megias, D.: Unsupervised steganalysis based on artificial training sets. Eng. Appl. Artif. Intell. 50, 45–59 (2016)
Liu, Z., Luo, P., Wang, X., Tang, X.: Deep learning face attributes in the wild. In: Proceedings of the IEEE International Conference on Computer Vision, pp. 3730–3738 (2015)
Lu, S.P., Wang, R., Zhong, T., Rosin, P.L.: Large-capacity image steganography based on invertible neural networks. In: Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, pp. 10816–10825 (2021)
Luo, X., Li, Y., Chang, H., Liu, C., Milanfar, P., Yang, F.: Dvmark: A deep multiscale framework for video watermarking. arXiv preprint arXiv:2104.12734 (2021)
Luo, X., Zhan, R., Chang, H., Yang, F., Milanfar, P.: Distortion agnostic deep watermarking. In: Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, pp. 13548–13557 (2020)
Ma, S., Zhang, X., Jia, C., Zhao, Z., Wang, S., Wanga, S.: Image and video compression with neural networks: a review. IEEE Trans. Circuits Syst. Video Technol. (2019)
Minnen, D., Ballé, J., Toderici, G.D.: Joint autoregressive and hierarchical priors for learned image compression. Adv. Neural. Inf. Process. Syst. 31, 10771–10780 (2018)
Mishra, D., Singh, S.K., Singh, R.K.: Deep architectures for image compression: a critical review. Signal Process. 191, 108346 (2022)
Ohm, J.R., Sullivan, G.J.: Versatile video coding-towards the next generation of video compression. In: Picture Coding Symposium, vol. 2018 (2018)
Pevny, T., Filler, T., Bas, P.: Using high-dimensional image models to perform highly undetectable steganography. In: International Workshop on Information Hiding, pp. 161–177. Springer (2010)
Russakovsky, O., et al.: Imagenet large scale visual recognition challenge. Int. J. Comput. Vision 115(3), 211–252 (2015)
Shin, R., Song, D.: Jpeg-resistant adversarial images. In: NIPS 2017 Workshop on Machine Learning and Computer Security, vol. 1 (2017)
Tancik, M., Mildenhall, B., Ng, R.: Stegastamp: invisible hyperlinks in physical photographs. In: Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, pp. 2117–2126 (2020)
Testolina, M., Upenik, E., Ebrahimi, T.: Towards image denoising in the latent space of learning-based compression. In: Applications of Digital Image Processing XLIV, vol. 11842, pp. 412–422. SPIE (2021)
Wang, Z., Bovik, A.C., Sheikh, H.R., Simoncelli, E.P.: Image quality assessment: from error visibility to structural similarity. IEEE Trans. Image Process. 13(4), 600–612 (2004)
Wengrowski, E., Dana, K.: Light field messaging with deep photographic steganography. In: Proceedings of the IEEE/CVF Conference on Computer Vision and Pattern Recognition, pp. 1515–1524 (2019)
Yang, Y., Mandt, S., Theis, L.: An introduction to neural data compression. arXiv preprint arXiv:2202.06533 (2022)
Zhang, C., Benz, P., Karjauv, A., Sun, G., Kweon, I.S.: UDH: universal deep hiding for steganography, watermarking, and light field messaging. Adv. Neural. Inf. Process. Syst. 33, 10223–10234 (2020)
Zhang, R., Isola, P., Efros, A.A., Shechtman, E., Wang, O.: The unreasonable effectiveness of deep features as a perceptual metric. In: CVPR (2018)
Zhu, J., Kaplan, R., Johnson, J., Fei-Fei, L.: Hidden: Hiding data with deep networks. In: Proceedings of the European Conference on Computer Vision (ECCV), pp. 657–672 (2018)
Acknowledgements
The authors would like to thank the NSTC of Taiwan and CITI SINICA for supporting this research under the grant numbers 111-2221-E-002-134-MY3 and Sinica 3012-C3447.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Huang, CH., Wu, JL. (2024). Joint Image Data Hiding and Rate-Distortion Optimization in Neural Compressed Latent Representations. In: Rudinac, S., et al. MultiMedia Modeling. MMM 2024. Lecture Notes in Computer Science, vol 14554. Springer, Cham. https://doi.org/10.1007/978-3-031-53305-1_8
Download citation
DOI: https://doi.org/10.1007/978-3-031-53305-1_8
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-53304-4
Online ISBN: 978-3-031-53305-1
eBook Packages: Computer ScienceComputer Science (R0)