Abstract
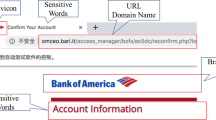
With the rapid growth of online space and the rising number of interconnected devices, security threats related to both personal and corporate data have increased considerably. Phishing attacks are commonly used to target corporate networks and gain initial access into security perimeters. The campaigns associated to these attacks span different propagation media and, in the case of web pages, attackers mimic real pages to trick users into downloading malicious software or sharing their credentials. In this paper we propose PhishVision, a framework for visually detecting phishing websites by identifying the main logo that characterizes them and comparing it with a set of logos which PhishVision protects. In case of presence of multiple logos, the framework is able to reconstruct which logo identifies the page while ignoring the others. The framework has been designed to have a lower false positive rate, fast detection times, and works in near-real-time fashion to provide a phishing detection service to Security Operation Centers. Its operators can use it make informed decisions about potential phishing activities by offering a comprehensible grey box explanation about how the framework has reached its conclusions. PhishVision achieves 0.997 ROC AUC on a test set of 404 screenshots, including both benign and malicious samples.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
Notes
References
Abdelnabi, S., Krombholz, K., Fritz, M.: Visualphishnet: zero-day phishing website detection by visual similarity. In: ACM SIGSAC Conference on Computer and Communications Security (2020)
Afroz, S., Greenstadt, R.: Phishzoo: detecting phishing websites by looking at them. In: IEEE International Conference on Semantic Computing (2011)
Ahmed, A.A., Abdullah, N.A.: Real time detection of phishing websites. In: IEEE Annual Information Technology, Electronics and Mobile Communication Conference (2016)
AlEroud, A., Karabatis, G.: Bypassing detection of URL-based phishing attacks using generative adversarial deep neural networks. In: International Workshop on Security and Privacy Analytics (2020)
Bell, S., Komisarczuk, P.: An analysis of phishing blacklists: google safe browsing, openphish, and phishtank. In: Australasian Computer Science Week Multiconference (2020)
Bozkir, A.S., Aydos, M.: Logosense: a companion hog based logo detection scheme for phishing web page and e-mail brand recognition. Comput. Secur. 95, 101855 (2020)
Diederik, P.K., Ba, J.: Adam: a method for stochastic optimization. Tech. rep. (2017)
ENISA. Enisa threat landscape 2022. Tech. rep. (2022)
Feroz, M.N., Mengel, S.: Phishing url detection using url ranking. In: IEEE International Congress on Big Data (2015)
Fu, A.Y., Wenyin, L., Deng, X.: Detecting phishing web pages with visual similarity assessment based on earth mover’s distance (emd). IEEE Trans. Depend. Secure Comput. 3(4), 301–311 (2006)
Ge, Z., Liu, S., Li, Z., Yoshie, O., Sun, J.: Ota: optimal transport assignment for object detection. In: IEEE/CVF Conference on Computer Vision and Pattern Recognition (2021)
Ge, Z., Liu, S., Wang, F., Li, Z., Sun, J.: Yolox: exceeding yolo series in 2021. arXiv preprint arXiv:2107.08430 (2021)
IBM. Cost of a data breach report 2022. Tech. rep. (2022)
Lin, T.Y., Goyal, P., Girshick, R., He, K., Dollár, P.: Focal loss for dense object detection. In: IEEE International Conference on Computer Vision (2017)
Lin, T.Y., et al.: Microsoft coco: common objects in context. In: European Conference on Computer Vision (2014)
Lin, Y., Liu, R., Divakaran, D.M., Ng, J.Y., Chan, Q.Z., Lu, Y., Si, Y., Zhang, F., Dong, J.S.: Phishpedia: A hybrid deep learning based approach to visually identify phishing webpages. In: USENIX Security Symposium (2021)
Liu, R., Lin, Y., Yang, X., Ng, S.H., Divakaran, D.M., Dong, J.S.: Inferring phishing intention via webpage appearance and dynamics: a deep vision based approach. In: USENIX Security Symposium (2022)
Marforio, C., Jayaram Masti, R., Soriente, C., Kostiainen, K., Čapkun, S.: Evaluation of personalized security indicators as an anti-phishing mechanism for smartphone applications. In: CHI Conference on Human Factors in Computing Systems (2016)
Moghimi, M., Varjani, A.Y.: New rule-based phishing detection method. Expert Syst. Appl. 53, 231–242 (2016)
Moore, S.: 7 top trends in cybersecurity for 2022 - gartner inc. Tech. rep. (2023)
Nguyen, L.A.T., To, B.L., Nguyen, H.K., Nguyen, M.H.: A novel approach for phishing detection using url-based heuristic. In: International Conference on Computing, Management and Telecommunications (2014)
PhishLabs, F.: Ransomware Attacks: Why Email is Still the Most Common Delivery Method. Tech. rep, Fortra (2023)
Rao, R.S., Ali, S.T.: Phishshield: a desktop application to detect phishing webpages through heuristic approach. Procedia Comput. Sci. 54, 147–156 (2015)
Redmon, J., Divvala, S., Girshick, R., Farhadi, A.: You only look once: unified, real-time object detection. In: IEEE Conference on Computer Vision and Pattern Recognition (2016)
Redmon, J., Farhadi, A.: Yolo9000: better, faster, stronger. In: IEEE Conference on Computer Vision and Pattern Recognition (2017)
Sheng, S., Wardman, B., Warner, G., Cranor, L., Hong, J., Zhang, C.: An empirical analysis of phishing blacklists. In: International Conference on Email and Anti-Spam (2009)
Song, F., Lei, Y., Chen, S., Fan, L., Liu, Y.: Advanced evasion attacks and mitigations on practical ml-based phishing website classifiers. Int. J. Intell. Syst. 36(9), 5210–5240 (2021)
Vade. Phishers’ favorites. 2022 year-in-review. Tech. rep. (2023)
Vidas, T., Owusu, E., Wang, S., Zeng, C., Cranor, L.F., Christin, N.: Qrishing: the susceptibility of smartphone users to QR code phishing attacks. In: Financial Cryptography and Data Security (2013)
Wang, C.Y., Bochkovskiy, A., Liao, H.Y.M.: Yolov7: trainable bag-of-freebies sets new state-of-the-art for real-time object detectors. arXiv preprint arXiv:2207.02696 (2022)
Xiang, G., Hong, J., Rose, C.P., Cranor, L.: Cantina+ a feature-rich machine learning framework for detecting phishing web sites. ACM Trans. Inf. Syst. Secur. 14(2), 1–28 (2011)
Acknowledgments
This work is partially supported by project SERICS (PE00000014) under the MUR National Recovery and Resilience Plan funded by the European Union - NextGenerationEU.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2024 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Graziano, G., Ucci, D., Bisio, F., Oneto, L. (2024). PhishVision: A Deep Learning Based Visual Brand Impersonation Detector for Identifying Phishing Attacks. In: Pereira, A.I., Mendes, A., Fernandes, F.P., Pacheco, M.F., Coelho, J.P., Lima, J. (eds) Optimization, Learning Algorithms and Applications. OL2A 2023. Communications in Computer and Information Science, vol 1981. Springer, Cham. https://doi.org/10.1007/978-3-031-53025-8_9
Download citation
DOI: https://doi.org/10.1007/978-3-031-53025-8_9
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-53024-1
Online ISBN: 978-3-031-53025-8
eBook Packages: Computer ScienceComputer Science (R0)