Abstract
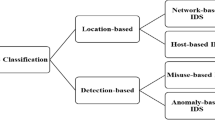
Intrusion detection system (IDS) protects the network from suspicious and harmful activities. It scans the network for harmful activity and any potential breaching. Even in the presence of the so many network intrusion APIs there are still problems in detecting the intrusion. These problems can be handled through the normalization of whole dataset, and ranking of feature on benchmark dataset before training the classification models. In this paper, used NSL-KDD dataset for the analysation of various features and test the efficiency of the various algorithms. For each value of k, then, trained each model separately and evaluated the feature selection approach with the algorithms. This work, make use of feature selection techniques like Information gain, SelectKBest, Pearson coefficient and Random forest. And also iterate over the number of features to pick the best values in order to train the dataset.The selected features then tested on different machine and deep learning approach. This work make use of stacked ensemble learning technique for classification. This stacked ensemble learner contains model which makes un-correlated error there by making the model more robust.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Rashid, A., Siddique, M.J., Ahmed, S.M.: Machine and deep learning based comparative analysis using hybrid approaches for intrusion detection system. In: 2020 3rd International Conference on Advancements in Computational Sciences (ICACS), pp. 1–9 (2020). IEEE
Ali, A., Shaukat, S., Tayyab, M., Khan, M.A., Khan, J.S., Ahmad, J., et al.: Network intrusion detection leveraging machine learning and feature selection. In: 2020 IEEE 17th International Conference on Smart Communities: Improving Quality of Life Using ICT, IoT and AI (HONET), pp. 49–53. IEEE (2020)
Gao, N., Gao, L., Gao, Q., Wang, H.: An intrusion detection model based on deep belief networks. In: 2014 Second International Conference on Advanced Cloud and Big Data, pp. 247–252. IEEE (2014)
Sangkatsanee, P., Wattanapongsakorn, N., Charnsripinyo, C.: Practical real-time intrusion detection using machine learning approaches. Comput. Commun. 34(18), 2227–2235 (2011)
Sinclair, C., Pierce, L., Matzner, S.: An application of machine learning to network intrusion detection. In: Proceedings 15th Annual Computer Security Applications Conference (ACSAC’99), pp. 371–377. IEEE (1999)
Alazzam, H., Sharieh, A., Sabri, K.E.: A feature selection algorithm for intrusion detection system based on pigeon inspired optimizer. Expert Syst. Appl. 148, 113249 (2020)
Ieracitano, C., Adeel, A., Morabito, F.C., Hussain, A.: A novel statistical analysis and autoencoder driven intelligent intrusion detection approach. Neurocomputing 387, 51–62 (2020)
Aggarwal, P., Sharma, S.K.: Analysis of kdd dataset attributes-class wise for intrusion detection. Procedia Comput. Sci. 57, 842–851 (2015)
Kirch, W. (ed.): Pearson’s Correlation Coefficient, pp. 1090–1091. Springer, Berlin (2008)
Shaltout, N., Elhefnawi, M., Rafea, A., Moustafa, A.: Information gain as a feature selection method for the efficient classification of influenza based on viral hosts. Lect. Notes Eng. Comput. Sci. 1, 625–631 (2014)
Kursa, M., Rudnicki, W.: The all relevant feature selection using random forest (2011)
Leo, B.: Random Forests, vol. 45. Springer, Berlin (2001)
Chen, T., Guestrin, C.: Xgboost: A scalable tree boosting system. In: Proceedings of the 22nd Acm Sigkdd International Conference on Knowledge Discovery and Data Mining, pp. 785–794 (2016)
Rokach, L., Maimon, O.: Decision Trees 6, 165–192 (2005)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Sunil, C.K., Reddy, S., Kanber, S.G., Sandeep, V.R., Patil, N. (2023). Comparative Analysis of Intrusion Detection System using ML and DL Techniques. In: Abraham, A., Hong, TP., Kotecha, K., Ma, K., Manghirmalani Mishra, P., Gandhi, N. (eds) Hybrid Intelligent Systems. HIS 2022. Lecture Notes in Networks and Systems, vol 647. Springer, Cham. https://doi.org/10.1007/978-3-031-27409-1_67
Download citation
DOI: https://doi.org/10.1007/978-3-031-27409-1_67
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-27408-4
Online ISBN: 978-3-031-27409-1
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)