Abstract
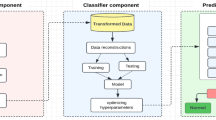
Since of huge progress of Internet of things (IoT) and networking technologies, and the expanding number of devices linked to the Internet, security and privacy problems must be addressed in order to secure hardware and information networks. Real-time monitoring of network resources and information is required to guarantee security. Intrusion detection systems have been utilized to continuously monitor, detect, and notify on an intrusion incident. Indeed, intrusion detection systems (IDSs) are a powerful cybersecurity tool that can be improved with machine learning (ML) and deep learning (DP) algorithms. These are intended to improve standard quality criteria like as accuracy (ACC), recall, and precision, but they hardly take time processor performance into effect. A novel IDS for IoT-based smart environments that utilizes DL and Supervised ML, is presented in this paper. The framework typically offered an optimum anomaly detection model that combines deep extraction based on the stacked autoencoder and combining feature selection using Information gain (IG) and Genetic algorithms (GA) (DEIGASe) which employs Multi-layer Perceptron (MLP) and support vector machine (SVM), K-nearest neighbors (K-NN) for classification. The BoT-IoT dataset was used to validate the proposed model metrics when compared to previous IDS, the results show that the proposed approach produces excellent Accuracy (ACC), Recall, Roc-auc and F1-score performance metrics.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Saba, T., Rehman, A., Sadad, T., Kolivand, H., Bahaj, S.A.: Anomaly-based intrusion detection system for IoT networks through deep learning model. Comput. Electric. Eng. 107810 (2022)
Von Solms, R., Van Niekerk, J.: From information security to cyber security. Comput. Secur. 38, 97–102 (2013)
Azrour, M., Mabrouki, J., Farhaoui, Y., Guezzaz, A.: Security analysis of Nikooghadam et al.’s authentication protocol for cloud-IoT. In: Gherabi, N., Kacprzyk, J. (eds.) Intelligent Systems in Big Data, Semantic Web and Machine Learning. AISC, vol. 1344, pp. 261–269. Springer, Cham (2021). https://doi.org/10.1007/978-3-030-72588-4_18
Kafle, V.P., Fukushima, Y., Harai, H.: Internet of things standardization in ITU and prospective networking technologies. IEEE Commun. Mag. 54(9), 43–49 (2016)
Guezzaz, A., Asimi, A., Mourade, A., Tbatou, Z., Asimi, Y.: A multilayer perceptron classifier for monitoring network traffic. In: Farhaoui, Y. (ed.) BDNT 2019. LNNS, vol. 81, pp. 262–270. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-23672-4_19
Guezzaz, A., Asimi, A., Asimi, Y., Azrour, M., Benkirane, S.: A distributed intrusion detection approach based on machine leaning techniques for a cloud security. In: Gherabi, N., Kacprzyk, J. (eds.) Intelligent Systems in Big Data, Semantic Web and Machine Learning. AISC, vol. 1344, pp. 85–94. Springer, Cham (2021). https://doi.org/10.1007/978-3-030-72588-4_6
Azrour, M., Mabrouki, J., Guezzaz, A., Farhaoui, Y.: A survey of high school students’ usage of smartphone in moroccan rural areas. Int. J. Cloud Comput. 10(3), 265-274 (2021)
Guezzaz, A., Benkirane, S., Azrour, M., Khurram, S.: A reliable network intrusion detection approach using decision tree with enhanced data quality. Secur. Commun. Netw. (2021)
Buczak, A.L., Guven, E.: A survey of data mining and machine learning methods for cyber security intrusion detection. IEEE Commun. Surv. Tutorials 18(2), 1153–1176 (2016)
Guezzaz, A., Asimi, A., Asimi, Y., Tbatou, Z., Sadqi, Y.: A lightweight neural classifier for intrusion detection. Gen. Lett. Math. 2, 57–66 (2017)
Azrour, M., Mabrouki, J., Guezzaz, A., Kanwal, A.: Internet of Things security: challenges and key issues. Secur. Commun. Netw. 5533843, 11 (2021)
Guezzaz, A., Asimi, A., Batou, Z., Asimi, Y., Sadqi, Y.: A global intrusion detection system using PcapSockS sniffer and multilayer perceptron classifier. Int. J. Netw. Secur. 21(3), 438–450 (2019)
Koroniotis, N., Moustafa, N., Sitnikova, E.: A new network forensic framework based on deep learning for Internet of Things networks: A particle deep framework. Future Gen. Comput. Syst. 110, 91–106 (2020)
Guezzaz, M. Azrour, S., Benkirane, M., Mohyeddine, H., Attou, M., Douiba. A.: Lightweight hybrid intrusion detection framework using machine learning for edge-based IIoT security. Int. Arab J. Inf. Technol. 19(5) (2022)
Diro, A., Chilamkurti, N.: Distributed attack detection scheme using deep learning approach for Internet of Things. Future Gen. Comput. Syst. 82, 761–768 (2017)
Sarker, I.H., Abushark, Y.B., Alsolami, F., Khan, A.I.: Intrudtree: a machine learning based cyber security intrusion detection model. Symmetry 12(5), 754 (2020)
Jabbar, M.A., Aluvalu, R., Seelam, S.S.R.: RFAODE: a novel ensemble intrusion detection system. Procedia Comput. Sci. 115, 226–234 (2017)
Chaabouni, N., Mosbah, M., Zemmari, A., Sauvignac, C.: A OneM2M intrusion detection and prevention system based on edge machine learning. In: IEEE/IFIP Network Operations and Management Symposium, pp. 1–7 (2020)
Ullah, I., Mahmoud, Q.H.: Design and development of a deep learning-based model for anomaly detection in IoT Networks. IEEE Access, 9, 103906–103926 (2021)
Shafiq, M., Tian, Z., Sun, Y., Du, X., Guizani, M.: Selection of effective machine learning algorithm and Bot-IoT attacks traffic identification for internet of things in smart city. Futur. Gener. Comput. Syst. 107, 433–442 (2020)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2023 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Hazman, C., Benkirane, S., Guezzaz, A., Azrour, M., Abdedaime, M. (2023). Intrusion Detection Framework for IoT-Based Smart Environments Security. In: Farhaoui, Y., Rocha, A., Brahmia, Z., Bhushab, B. (eds) Artificial Intelligence and Smart Environment. ICAISE 2022. Lecture Notes in Networks and Systems, vol 635. Springer, Cham. https://doi.org/10.1007/978-3-031-26254-8_79
Download citation
DOI: https://doi.org/10.1007/978-3-031-26254-8_79
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-26253-1
Online ISBN: 978-3-031-26254-8
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)