Abstract
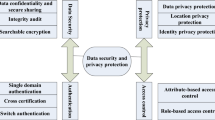
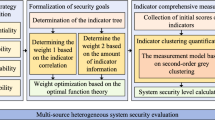
With the rapid development and wide application of 5G networks, artificial intelligence, and big data, traditional cloud computing cannot handle the massive data generated by edge terminals. Edge computing has gradually been widely used as a computing method close to objects. However, due to the open features of edge computing, such as content perception, real-time computing, and parallel processing, the data security issues that already exist in the cloud computing environment have become more prominent. Data security protection capability evaluation is an important part of the improvement of data security capabilities. However, current protection capability evaluations are mostly qualitative evaluations and lack quantitative evaluation models. Aiming at the edge computing network architecture, this paper proposes a data security protection capability evaluation model based on weight presets. By studying the edge architecture data security protection capability score and cost curve, the data security protection model is adaptively selected. Experiments show that the method can quantitatively calculate the data security protection capability in the edge computing environment, and can guide the construction of the protection model through the score-cost curve.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Shi, W., Cao, J., Zhang, Q., et al.: Edge computing: vision and challenges. Internet Things J. 3(5), 637–646 (2016)
Zhang, J., Chen, B., Zhao, Y., et al.: Data security and privacy-preserving in edge computing paradigm: survey and open issues. IEEE Access 18209–18237 (2018)
Chadwick, D.W., Fan, W., Constantino, G., et al.: A cloud-edge based data security architecture for sharing and analysing cyber threat information. Future Generat. Comput. Syst. 102, 710–722 (2020)
Liu, D., Shen, J., Vijayakumar, P., Wang, A., Zhou, T.: Efficient data integrity auditing with corrupted data recovery for edge computing in enterprise multimedia security. Multimedia Tools Applicat. 79(15–16), 10851–10870 (2020). https://doi.org/10.1007/s11042-019-08558-1
Guan, Y., Shao, J., Wei, G., et al.: Data security and privacy in fog computing. IEEE Netw. 32(5), 106–111 (2018)
Han, W., Xiao, Y.: Big data security analytic for smart grid with fog nodes. In: International Conference on Security. Springer, Cham (2016). https://doi.org/10.1007/978-3-319-49148-6_6
Guan, Y., Shao, J., Wei, G., et al.: Data security and privacy in fog computing. IEEE Netw. 106–111 (2018)
Puthal, D., Ranjan, R., Nanda, A., et al.: Secure authentication and load balancing of distributed edge datacenters. J. Parallel Distribut. Comput. 124, 60–69 (2019)
Mahmoud, S., Salman, A.: Cost estimate and input energy of floor systems in low seismic regions. Comput. Mater. Continua 71(2), 2159–2173 (2022)
Attaallah, A., Khan, R.A.: Estimating usable-security through hesitant fuzzy linguistic term sets based technique. Comput. Mater. Continua 70(3), 5683–5705 (2022)
Aydi, W., Alduais, F.S.: Estimating weibull parameters using least squares and multilayer perceptron vs. Bayes estimation. Comput. Mater. Continua 71(2), 4033–4050 (2022)
Funding
The authors declare that they have no conflicts of interest to report regarding the present study.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Liu, C., Sun, Y., Li, J., Wang, M., Wang, T. (2022). A Novel Evaluation Model of Data Security Protection Capability in Edge Computing Environment. In: Sun, X., Zhang, X., Xia, Z., Bertino, E. (eds) Advances in Artificial Intelligence and Security. ICAIS 2022. Communications in Computer and Information Science, vol 1587. Springer, Cham. https://doi.org/10.1007/978-3-031-06761-7_44
Download citation
DOI: https://doi.org/10.1007/978-3-031-06761-7_44
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-031-06760-0
Online ISBN: 978-3-031-06761-7
eBook Packages: Computer ScienceComputer Science (R0)