Abstract
Verification of memory safety such as absence of null pointer dereferences and memory leaks in system software is important in practice. O’Hearn’s group proposed a new method of memory safety analysis/verification by modular abstract interpretation with separation logic and biabduction. To realize this method, one has to construct a call graph before the modular abstract interpretation. This paper aims to analyze/verify memory safety of system software written in C programming language by this method, and as the first step this paper provides a function pointer eliminator tool to eliminate function pointer calls in order to construct a call graph. The tool uses SVF for pointer analysis. First C programs are translated into LLVM programs by Clang and then SVF analyses the LLVM programs. The tool given in this paper finds correspondence between function pointer calls in C programs and those in LLVM programs, and transforms the C programs into C programs with the same functionality and without any function pointer calls. The experimental results for gzip, git, and OpenSSL using this function pointer eliminator are presented and they show that this tool is sufficiently efficient and precise for the purpose.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Calcagno, C., Distefano, D., O’Hearn, P.W., Yang, H.: Footprint analysis: a shape analysis that discovers preconditions. In: Nielson, H.R., Filé, G. (eds.) SAS 2007. LNCS, vol. 4634, pp. 402–418. Springer, Heidelberg (2007). https://doi.org/10.1007/978-3-540-74061-2_25
Calcagno, C., Distefano, D., O’Hearn, P.W., Yang, H.: Compositional shape analysis by means of bi-abduction. J. ACM 58(6), 26:1–26:66 (2011)
Distefano, D., O’Hearn, P.W., Yang, H.: A local shape analysis based on separation logic. In: Hermanns, H., Palsberg, J. (eds.) TACAS 2006. LNCS, vol. 3920, pp. 287–302. Springer, Heidelberg (2006). https://doi.org/10.1007/11691372_19
Distefano, D., Fähndrich, M., Logozzo, F., O’Hearn, P.W.: Scaling static analyses at Facebook. Commun. ACM 62(8), 62–70 (2019)
Faruki, P., Laxmi, V., Gaur, M.S., Vinod, P.: Mining control flow graph as API call-grams to detect portable executable malware. In: Proceedings of the Fifth International Conference on Security of Information and Networks (SIN 2012), pp. 130–137 (2012)
Gascon, H., Yamaguchi, F., Arp, D., Rieck, K.: Structural detection of android malware using embedded call graphs. In: Proceedings of the 2013 ACM Workshop on Artificial Intelligence and Security (AISec 2013), pp. 45–54 (2013)
Hu, X., Chiueh, T.-C., Shin, K.G.: Large-scale malware indexing using function-call graphs. In: Proceedings of the 16th ACM Conference on Computer and Communications Security (CCS 2009), pp. 611–620 (2009)
Jang, J.-W., Woo, J., Yun, J., Kim, H.K.: Mal-Netminer: malware classification based on social network analysis of call graph, In: Proceedings of the 23rd International Conference on World Wide Web Companion (WWW 2014 Companion), pp. 731–734 (2014)
O’Hearn, P.W.: Separation logic. Commun. ACM 62(2), 86–95 (2019)
Sui, Y., Xue, J.: SVF: interprocedural static value-flow analysis in LLVM. In: Proceedings of the 25th International Conference on Compiler Construction (CC 2016), pp. 265–266 (2016)
Zhang, W., Zhang, Yu.: Lightweight function pointer analysis. In: Lopez, J., Wu, Y. (eds.) ISPEC 2015. LNCS, vol. 9065, pp. 439–453. Springer, Cham (2015). https://doi.org/10.1007/978-3-319-17533-1_30
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Appendices
Appendix
A Screenshot
We give a screenshot of the command FPE.

B Examples
We give some examples of how the command FPE transforms an input C file into an output C file.
1.1 B.1 Example
The input file:

The output file:

1.2 B.2 Example
The input file:

The output file:

1.3 B.3 Example
The input file:

The output file:

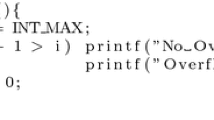
1.4 B.4 Example
The input file:

The output file:

1.5 B.5 Example
The input file:

The output file:

1.6 B.6 Example
The input file:

The output file:

1.7 B.7 Example
The input file:

The output file:

Rights and permissions
Copyright information
© 2021 Springer Nature Switzerland AG
About this paper
Cite this paper
Kimura, D., Ameen, M.F.A., Tatsuta, M., Nakazawa, K. (2021). Function Pointer Eliminator for C Programs. In: Oh, H. (eds) Programming Languages and Systems. APLAS 2021. Lecture Notes in Computer Science(), vol 13008. Springer, Cham. https://doi.org/10.1007/978-3-030-89051-3_2
Download citation
DOI: https://doi.org/10.1007/978-3-030-89051-3_2
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-89050-6
Online ISBN: 978-3-030-89051-3
eBook Packages: Computer ScienceComputer Science (R0)