Abstract
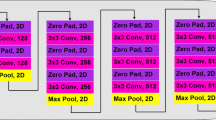
In the last decades, deep learning neural networks have taken several steps toward higher pattern recognition accuracies. Face recognition is one of the popular topics that have drawn much attention and it is now frequently used in everyday lives. However, the recognition performance suffers easily by irregularities and disturbances. The focus of this work is to explore the security performance of deep learning neural networks by using an adversarial attack approach. The ResNets is the framework of the proposed system and its recognition behaviors under the adversarial attacks are investigated. The experiments are performed by using MNIST and CIFAR-10 datasets and the detection and recognition errors are evaluated. The results show that the proposed systems can be an alternative that can resist perturbations better than the conventional models.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
LeCun, Y., Bottou, L., Bengio, Y., Haffner, P.: Gradient-based learning applied to document recognition. Proc. IEEE 86(11), 2278–2324 (1998)
Andor, D., et al.: Globally normalized transition-based neural networks. arXiv:1603.06042 (2016)
Mnih, V., et al.: Playing atari with deep reinforcement learning. arXiv:1312.5602 (2013)
Szegedy, C., et al.: Intriguing properties of neural networks. arXiv:1312.6199 (2013)
He, K., Zhang, H., Ren, S., Sun, J.: Deep residual learning for image recognition. arXiv:1512.03385 (2016)
Madry, A., Makelov, A., Schmidt, L., Tsipras, D., Vladu, A.: Towards deep learning models resistant to adversarial attacks. arXiv:1706.06083 (2017)
Xu, J., Liu, H., Wu, D., Zhou, F., Gao, C., Jiang, L.: Generating universal adversarial perturbation with ResNet. Inform. Sci. 537, 302–312 (2020)
Hochreiter, S., Bengio, Y., Frasconi, P., Schmidhuber, J.: Gradient flow in recurrent nets: the difficulty of learning long-term dependencies (2001)
Schmidhuber, J.: Learning complex, extended sequences using the principle of history compression. Neural Comput. 4(2), 234–242 (1992)
Deng, L.: The MNIST database of handwritten digit images for machine learning research. IEEE Signal Process. Mag. 29(6), 141–142 (2012)
Krizhevsky, A., Hinton, G.: Learning multiple layers of features from tiny images (2009)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2022 The Author(s), under exclusive license to Springer Nature Switzerland AG
About this paper
Cite this paper
Chen, F., Choi, J. (2022). Deep Learning Network Model Studies for Adversarial Attack Resistance. In: Kahraman, C., Cebi, S., Cevik Onar, S., Oztaysi, B., Tolga, A.C., Sari, I.U. (eds) Intelligent and Fuzzy Techniques for Emerging Conditions and Digital Transformation. INFUS 2021. Lecture Notes in Networks and Systems, vol 308. Springer, Cham. https://doi.org/10.1007/978-3-030-85577-2_19
Download citation
DOI: https://doi.org/10.1007/978-3-030-85577-2_19
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-85576-5
Online ISBN: 978-3-030-85577-2
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)