Abstract
To simplify shared-memory concurrent programming, in addition to low-level synchronisation primitives, several modern programming languages have started to offer core support for higher-level communication primitives as well, in the guise of message passing through channels. Yet, a growing body of evidence suggests that channel-based programming abstractions for shared memory also have their issues.
The Discourje project aims to help programmers cope with message-passing concurrency bugs in Clojure programs, based on run-time verification and dynamic monitoring. The idea is that programmers write not only implementations, but also specifications (of sessions of channel actions). Discourje then offers a library to ensure that implementations run safely relative to specifications (= “bad” channel actions never happen).
This paper gives a tour of the current state of Discourje, by example; it is intended to serve both as a general overview for readers who are unfamiliar with previous work on Discourje, and as an introduction to new features for readers who are familiar.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Notes
- 1.
- 2.
- 3.
With unbuffered channels, in the absence of a buffer, both sends and receives are blocking until a reciprocal channel action is performed on the other end of the channel. With buffered channels, in the presence of a bounded, n-capacity, order-preserving buffer, sends are blocking until the buffer is not full (then, a message is added to the back of the buffer), while receives are blocking until the buffer is not empty (then, a message is removed from the front of the buffer).
- 4.
Tic–Tac–Toe is a two-player game played on a \(3 \times 3\) grid. Players take turns to fill the initially blank spaces of the grid with crosses (“X”) and noughts (“O”). The first player to fill three consecutive spaces, in any direction, with the same symbol wins.
- 5.
A version of this example with buffered communication appears elsewhere [22].
- 6.
Many data structures in Clojure—including the vector that implements the grid—are persistent and, thus, effectively immutable: every operation on an old data structure leaves it unmodified and, instead, returns a new data structure. In concurrent programs, including Tic–Tac–Toe, persistent data structures can be used as thread-local copies of data, but modifications need to be explicitly communicated. Persistence also means that classical data races cannot happen: if threads communicate only persistent data structures through channels, freedom of data races is guaranteed.
- 7.
Rock–Paper–Scissors is a multiplayer game played in rounds. In every round, every remaining player chooses an item—rock, paper, or scissors—and reveals it. A player goes to the next round, unless some other player defeats them, while they defeat no other player, based on the chosen items in the current round (“scissors cuts paper, paper covers rock, rock crushes scissors”). The last player to remain wins.
- 8.
Go Fish is a multiplayer game played with a standard 52-card deck. A dealer shuffles the deck and deals an initial hand to every player. Then, players take turns to collect groups of cards of the same rank. Every turn, the active player asks a passive player for a card. If the asked player has it, the asking player gets it and takes another turn; if not, the asked player tells the asking player (“go”), the asking player gets a card from the dealer (“fish”), and the turn is passed to the asked player. The first player to hold only complete groups wins. (This version of Go Fish is due to Parlett [38].).
References
Ancona, D., et al.: Behavioral types in programming languages. Found. Trends Program. Lang. 3(2–3), 95–230 (2016)
Barnett, M., Chang, B.-Y.E., DeLine, R., Jacobs, B., Leino, K.R.M.: Boogie: a modular reusable verifier for object-oriented programs. In: de Boer, F.S., Bonsangue, M.M., Graf, S., de Roever, W.-P. (eds.) FMCO 2005. LNCS, vol. 4111, pp. 364–387. Springer, Heidelberg (2006). https://doi.org/10.1007/11804192_17
Bartocci, E., Falcone, Y., Francalanza, A., Reger, G.: Introduction to runtime verification. In: Bartocci, E., Falcone, Y. (eds.) Lectures on Runtime Verification. LNCS, vol. 10457, pp. 1–33. Springer, Cham (2018). https://doi.org/10.1007/978-3-319-75632-5_1
Bocchi, L., Chen, T., Demangeon, R., Honda, K., Yoshida, N.: Monitoring networks through multiparty session types. Theor. Comput. Sci. 669, 33–58 (2017)
Bocchi, L., Honda, K., Tuosto, E., Yoshida, N.: A theory of design-by-contract for distributed multiparty interactions. In: Gastin, P., Laroussinie, F. (eds.) CONCUR 2010. LNCS, vol. 6269, pp. 162–176. Springer, Heidelberg (2010). https://doi.org/10.1007/978-3-642-15375-4_12
Bonnaire-Sergeant, A., Davies, R., Tobin-Hochstadt, S.: Practical optional types for Clojure. In: Thiemann, P. (ed.) ESOP 2016. LNCS, vol. 9632, pp. 68–94. Springer, Heidelberg (2016). https://doi.org/10.1007/978-3-662-49498-1_4
Castro, D., Hu, R., Jongmans, S., Ng, N., Yoshida, N.: Distributed programming using role-parametric session types in go: statically-typed endpoint APIs for dynamically-instantiated communication structures. PACMPL 3(POPL), 29:1–29:30 (2019)
Clojure Team: Clojure - Clojure core.async Channels, 28 June 2013. https://clojure.org/news/2013/06/28/clojure-clore-async-channels. Accessed 1 Sept 2019
Clojure Team: Clojure - State of Clojure 2019 Results, 04 February 2019. https://clojure.org/news/2019/02/04/state-of-clojure-2019. Accessed 1 Sept 2019
Clojure Team: Clojure - State of Clojure 2020 Results, 20 February 2019. https://clojure.org/news/2020/02/20/state-of-clojure-2020. Accessed 28 May 2020
Clojure Team: Clojure (nd). https://clojure.org. Accessed 1 Sept 2019
Cohen, E., et al.: VCC: a practical system for verifying concurrent C. In: Berghofer, S., Nipkow, T., Urban, C., Wenzel, M. (eds.) TPHOLs 2009. LNCS, vol. 5674, pp. 23–42. Springer, Heidelberg (2009). https://doi.org/10.1007/978-3-642-03359-9_2
Demangeon, R., Honda, K., Hu, R., Neykova, R., Yoshida, N.: Practical interruptible conversations: distributed dynamic verification with multiparty session types and python. Formal Methods Syst. Des. 46(3), 197–225 (2015)
Filliâtre, J.-C., Paskevich, A.: Why3—where programs meet provers. In: Felleisen, M., Gardner, P. (eds.) ESOP 2013. LNCS, vol. 7792, pp. 125–128. Springer, Heidelberg (2013). https://doi.org/10.1007/978-3-642-37036-6_8
Fokkink, W.: Introduction to Process Algebra. Texts in Theoretical Computer Science. An EATCS Series. Springer, Heidelberg (2000). https://doi.org/10.1007/978-3-662-04293-9
Go Team: Go 2016 Survey Results - The Go Blog, 03 June 2017. https://blog.golang.org/survey2016-results. Accessed 1 Sept 2019
Go Team: Go 2017 Survey Results - The Go Blog, 26 February 2018. https://blog.golang.org/survey2017-results. Accessed 1 Sept 2019
Go Team: Go 2018 Survey Results - The Go Blog, 28 March 2019. https://blog.golang.org/survey2018-results. Accessed 1 Sept 2019
Go Team: Go Developer Survey 2019 Results - The Go Blog, 20 April 2020. https://blog.golang.org/survey2019-results. Accessed 8 May 2020
Go Team: Effective Go - The Go Programming Language (nd). https://golang.org/doc/effective_go.html. Accessed 8 May 2020
Go Team: The Go Programming Language (nd). https://golang.org. Accessed 1 Sept 2019
Hamers, R., Jongmans, S.-S.: Discourje: runtime verification of communication protocols in Clojure. In: Biere, A., Parker, D. (eds.) TACAS 2020. LNCS, vol. 12078, pp. 266–284. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-45190-5_15
Hickey, R.: The Clojure programming language. In: DLS, p. 1. ACM (2008)
Honda, K., Yoshida, N., Carbone, M.: Multiparty asynchronous session types. In: POPL, pp. 273–284. ACM (2008)
Hu, R., Neykova, R., Yoshida, N., Demangeon, R., Honda, K.: Practical interruptible conversations. In: Legay, A., Bensalem, S. (eds.) RV 2013. LNCS, vol. 8174, pp. 130–148. Springer, Heidelberg (2013). https://doi.org/10.1007/978-3-642-40787-1_8
Hu, R., Yoshida, N.: Hybrid session verification through endpoint API generation. In: Stevens, P., Wąsowski, A. (eds.) FASE 2016. LNCS, vol. 9633, pp. 401–418. Springer, Heidelberg (2016). https://doi.org/10.1007/978-3-662-49665-7_24
Hu, R., Yoshida, N.: Explicit connection actions in multiparty session types. In: Huisman, M., Rubin, J. (eds.) FASE 2017. LNCS, vol. 10202, pp. 116–133. Springer, Heidelberg (2017). https://doi.org/10.1007/978-3-662-54494-5_7
Hüttel, H., et al.: Foundations of session types and behavioural contracts. ACM Comput. Surv. 49(1), 3:1–3:36 (2016)
Kiczales, G., et al.: Aspect-oriented programming. In: Akşit, M., Matsuoka, S. (eds.) ECOOP 1997. LNCS, vol. 1241, pp. 220–242. Springer, Heidelberg (1997). https://doi.org/10.1007/BFb0053381
Lange, J., Ng, N., Toninho, B., Yoshida, N.: Fencing off go: liveness and safety for channel-based programming. In: POPL, pp. 748–761. ACM (2017)
Lange, J., Ng, N., Toninho, B., Yoshida, N.: A static verification framework for message passing in go using behavioural types. In: ICSE, pp. 1137–1148. ACM (2018)
López, H.A., et al.: Protocol-based verification of message-passing parallel programs. In: OOPSLA, pp. 280–298. ACM (2015)
Neykova, R., Bocchi, L., Yoshida, N.: Timed runtime monitoring for multiparty conversations. Formal Aspects Comput. 29(5), 877–910 (2017). https://doi.org/10.1007/s00165-017-0420-8
Neykova, R., Hu, R., Yoshida, N., Abdeljallal, F.: A session type provider: compile-time API generation of distributed protocols with refinements in f#. In: CC, pp. 128–138. ACM (2018)
Neykova, R., Yoshida, N.: Let it recover: multiparty protocol-induced recovery. In: CC, pp. 98–108. ACM (2017)
Ng, N., Yoshida, N.: Static deadlock detection for concurrent go by global session graph synthesis. In: CC, pp. 174–184. ACM (2016)
Ng, N., Yoshida, N., Honda, K.: Multiparty session C: safe parallel programming with message optimisation. In: Furia, C.A., Nanz, S. (eds.) TOOLS 2012. LNCS, vol. 7304, pp. 202–218. Springer, Heidelberg (2012). https://doi.org/10.1007/978-3-642-30561-0_15
Parlett, D.: The Penguin Book of Card Games. Penguin (2008)
Pinzaru, G., Rivera, V.: Towards static verification of Clojure contract-based programs. In: Mazzara, M., Bruel, J.-M., Meyer, B., Petrenko, A. (eds.) TOOLS 2019. LNCS, vol. 11771, pp. 73–80. Springer, Cham (2019). https://doi.org/10.1007/978-3-030-29852-4_5
Rust Team: Rust Programming Language (nd). https://rust-lang.org. Accessed 1 Sept 2019
Santos, C., Martins, F., Vasconcelos, V.T.: Deductive verification of parallel programs using why3. In: ICE. EPTCS, vol. 189, pp. 128–142 (2015)
Scalas, A., Dardha, O., Hu, R., Yoshida, N.: A linear decomposition of multiparty sessions for safe distributed programming. In: ECOOP. LIPIcs, vol. 74, pp. 24:1–24:31. Schloss Dagstuhl - Leibniz-Zentrum fuer Informatik (2017)
Stadtmüller, K., Sulzmann, M., Thiemann, P.: Static trace-based deadlock analysis for synchronous mini-go. In: Igarashi, A. (ed.) APLAS 2016. LNCS, vol. 10017, pp. 116–136. Springer, Cham (2016). https://doi.org/10.1007/978-3-319-47958-3_7
Tasharofi, S., Dinges, P., Johnson, R.E.: Why do Scala developers mix the actor model with other concurrency models? In: Castagna, G. (ed.) ECOOP 2013. LNCS, vol. 7920, pp. 302–326. Springer, Heidelberg (2013). https://doi.org/10.1007/978-3-642-39038-8_13
Tu, T., Liu, X., Song, L., Zhang, Y.: Understanding real-world concurrency bugs in go. In: ASPLOS, pp. 865–878. ACM (2019)
Yoshida, N., Gheri, L.: A very gentle introduction to multiparty session types. In: Hung, D.V., D’Souza, M. (eds.) ICDCIT 2020. LNCS, vol. 11969, pp. 73–93. Springer, Cham (2020). https://doi.org/10.1007/978-3-030-36987-3_5
Acknowledgements
We thank Luc Edixhoven and anonymous reviewers for comments on an earlier version of this paper. Funded by the Netherlands Organisation of Scientific Research (NWO): 016.Veni.192.103.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
A Clojure
A Clojure
Standard library
 :
:
-
 : first evaluates e to v; then binds x to v in the global environment.
: first evaluates e to v; then binds x to v in the global environment. -
 : first evaluates \(e_1\); if
: first evaluates \(e_1\); if
 , evaluates \(e_2\); else, evaluates \(e_3\).
, evaluates \(e_2\); else, evaluates \(e_3\). -
 : first evaluates \(e_1\) to \(v_1\); then evaluates \(e_2\) to \(v_2\) with \(x_1\) bound to \(v_1\); ...; then evaluates \(e_n\) to \(v_n\) with \(x_1\), ..., \(x_{n-1}\) bound to \(v_1\), ..., \(v_{n-1}\); then evaluates e with \(x_1\), ..., \(x_n\) bound to \(v_1\), ..., \(v_n\).
: first evaluates \(e_1\) to \(v_1\); then evaluates \(e_2\) to \(v_2\) with \(x_1\) bound to \(v_1\); ...; then evaluates \(e_n\) to \(v_n\) with \(x_1\), ..., \(x_{n-1}\) bound to \(v_1\), ..., \(v_{n-1}\); then evaluates e with \(x_1\), ..., \(x_n\) bound to \(v_1\), ..., \(v_n\). -
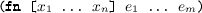 : evaluates to a function with parameters \(x_1\), ..., \(x_n\) and creates a recursion point; then, when applied to arguments \(v_1\), ..., \(v_n\), sequentially evaluates \(e_1\), ..., \(e_m\) with \(x_1\), ..., \(x_n\) bound to \(v_1\), ..., \(v_n\).
: evaluates to a function with parameters \(x_1\), ..., \(x_n\) and creates a recursion point; then, when applied to arguments \(v_1\), ..., \(v_n\), sequentially evaluates \(e_1\), ..., \(e_m\) with \(x_1\), ..., \(x_n\) bound to \(v_1\), ..., \(v_n\). -
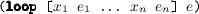 : same as
: same as
 , but also creates a recursion point.
, but also creates a recursion point. -
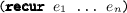 : first evaluates \(e_1\), ..., \(e_n\) to \(v_1\), ..., \(v_n\); then evaluates the nearest recursion point with \(x_1\), ..., \(x_n\) bound to \(v_1\), ..., \(v_n\).
: first evaluates \(e_1\), ..., \(e_n\) to \(v_1\), ..., \(v_n\); then evaluates the nearest recursion point with \(x_1\), ..., \(x_n\) bound to \(v_1\), ..., \(v_n\).
Standard library
 :
:
-
 : starts a new thread that evaluates e.
: starts a new thread that evaluates e. -
 : evaluates to a new unbuffered channel.
: evaluates to a new unbuffered channel. -
 : first evaluates e to channel c; then closes c.
: first evaluates e to channel c; then closes c. -
 : first evaluates \(e_1\) to channel c; then evaluates \(e_2\) to v; then sends v through c.
: first evaluates \(e_1\) to channel c; then evaluates \(e_2\) to v; then sends v through c. -
 : first evaluates e to channel c; then receives a value through c.
: first evaluates e to channel c; then receives a value through c. -
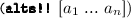 : for every \(a_i\) of the form
: for every \(a_i\) of the form
 (send) or
(send) or
 (receive), evaluates \(e_{i,1}\) and \(e_i\) to channel \(c_i\), and then, evaluates \(e_{i,2}\) to v; then, waits until one of these channel actions can be performed; then, performs a channel action that can be performed (non-deterministically selected).
(receive), evaluates \(e_{i,1}\) and \(e_i\) to channel \(c_i\), and then, evaluates \(e_{i,2}\) to v; then, waits until one of these channel actions can be performed; then, performs a channel action that can be performed (non-deterministically selected).
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Hamers, R., Jongmans, SS. (2020). Safe Sessions of Channel Actions in Clojure: A Tour of the Discourje Project. In: Margaria, T., Steffen, B. (eds) Leveraging Applications of Formal Methods, Verification and Validation: Verification Principles. ISoLA 2020. Lecture Notes in Computer Science(), vol 12476. Springer, Cham. https://doi.org/10.1007/978-3-030-61362-4_28
Download citation
DOI: https://doi.org/10.1007/978-3-030-61362-4_28
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-61361-7
Online ISBN: 978-3-030-61362-4
eBook Packages: Computer ScienceComputer Science (R0)


 : first evaluates e to v; then binds x to v in the global environment.
: first evaluates e to v; then binds x to v in the global environment. : first evaluates
: first evaluates  , evaluates
, evaluates  : first evaluates
: first evaluates 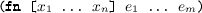 : evaluates to a function with parameters
: evaluates to a function with parameters 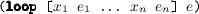 : same as
: same as
 , but also creates a recursion point.
, but also creates a recursion point.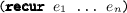 : first evaluates
: first evaluates  : starts a new thread that evaluates e.
: starts a new thread that evaluates e. : evaluates to a new unbuffered channel.
: evaluates to a new unbuffered channel. : first evaluates e to channel c; then closes c.
: first evaluates e to channel c; then closes c. : first evaluates
: first evaluates  : first evaluates e to channel c; then receives a value through c.
: first evaluates e to channel c; then receives a value through c.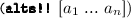 : for every
: for every  (send) or
(send) or
 (receive), evaluates
(receive), evaluates