Abstract
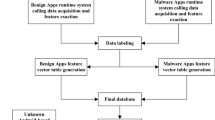
Android malware is a growing threat to the Android operating system. Various anti-virus tools are developed to detect Android malware. Most of these tools use Machine Learning (ML) algorithms. ML-based methods are robust and can detect future threats. However, we cannot directly deploy these resource-intensive tools on smartphones as smartphones have a limited amount of resources. In this paper, we propose two multi-stage classification models for the classification of Android malware. The first model is a combination of logistic regression and linear Support Vector Machine (SVM). We use a combination of logistic regression, K-means clustering, and linear SVM for the second model. We divide each model into two stages. The first stage involves the training of the classification model. The second stage consists of a decision function that classifies a given app as benign or malware. The proposed classification models can detect both Android malware and colluding app-pairs. Android application-collusion is a special kind of threat. The proposed classification models are low compute-intensive and straightforward to implement.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Statista. https://www.statista.com/statistics/272307/market-share-forecast-for-smartphone-operating-systems/
Bartel, A., Bissyande, T., Klein, J., Traon, Y.L., Azert, S., Li, L.: IccTA: detecting inter-component privacy leaks in android apps In: Proceedings of 37th International Conference on Software Engineering, Florence, pp. 280–291. IEEE (2015)
Chin, E., Porter, A.F., Greenwood, K., Wagner, D.: Analyzing inter-application communication in Android. In: Proceedings of the 9th International Conference on Mobile systems, Applications, and Services. ACM, pp. 239–252 (2011)
Felt, A.P., Wang, H.J., Moshchuk, A., Hanna, S., Chin, E.: Permission re-delegation: attacks and defences. In: Proceedings of the 20th USENIX Security Symposium, USENIX Association (2011)
Octeau, D., Jha, S., Derring, M., McDaniel, P., Bartel, A., Li, L., Klein, J., Traon, Y.L.: Combining static analysis with probabilistic models to enable market-scale android inter-component analysis In: Proceedings of 43rd Annual ACM SIGPLAN-SIGACT Symposium on Principles of Programming Languages, pp. 469–484. ACM (2016)
Porter, A.F., Ha, E., Egelman, S., Haney, A., Chin, E., Wagner, D.: Android permissions: user attention, comprehension, and behaviour In: Proceedings of the 8th Symposium on Usable Privacy and Security, Article 3, pp. 1–14. ACM (2012)
Wang, W., Wang, X., Feng, D., Liu, J., Han, Z., Zhang, X.: Exploring permission-induced risk in android applications for malicious application detection. IEEE Trans. Inf. Forensics Secur. 9(11), 1869–1882 (2014). https://doi.org/10.1109/TIFS.2014.2353996
Xie, Z., Zhu, S.: Group tie: toward hidden collusion group discovery in app stores. In: Proceedings of Conference on Security and Privacy in Wireless & Mobile Networks, pp. 153–164. ACM (2014)
Intel newsroom. https://newsroom.intel.com/news-releases/mcafee-labs-report-reveals-new-mobile-app-collusion-threats/
Yerima, S.Y., Sezer, S., Muttik, I.: High accuracy android malware detection using ensemble learning. IET Inf. Secur. 9(6), 313–320 (2015). https://doi.org/10.1049/iet-ifs.2014.0099, IET Digital Library. https://digital-library.theiet.org/content/journals/10.1049/iet-ifs.2014.0099
Li, J., Sun, L., Yan, Q., Li, Z., Srisa-an, W., Ye, H.: Significant permission identification for machine-learning-based android malware detection. IEEE Trans. Industr. Inf. 14(7), 3216–3225 (2018)
Arp, D., Spreitzenbarth, M., Hübner, M., Gascon, H., Rieck, K.: DREBIN: effective and explainable detection of android malware in your pocket. In: Symposium on Network and Distributed System Security (NDSS) (2014). https://doi.org/10.14722/ndss.2014.23247
Lu, Y., Kuo, C., Chen, H., Chen, C., Chou, S.: A SVM-based malware detection mechanism for android devices. In: 2018 International Conference on System Science and Engineering (ICSSE), New Taipei, pp. 1–6 (2018)
Faiz, M.F.I., Hussain, A.M., Marchang, N.: Detection of collusive app-pairs using machine learning. In: Proceedings of 3rd International Conference on Consumer Electronics ASIA, pp. 206–212. IEEE (2018)
Marforio, C., Ritzdorf, H., Francillon, A., Capkun, S.: Analysis of the communication between colluding applications on modern smartphones In: Proceedings of the 28th Annual Computer Security Applications Conference, pp. 51–60. ACM (2012)
Kalutarage, H.K., Nguyen, H.N., Shaikh, S.A.: Towards a threat assessment framework for apps collusion. In: Telecommunication Systems, pp. 417–430. Springer (2017)
Faiz, M.F.I., Hussain, M.A., Marchang, N.: App-collusion detection using a two-stage classifier. In: Barolli, L., Takizawa, M., Xhafa, F., Enokido, T. (eds.) Web, Artificial Intelligence and Network Applications. WAINA 2019. Advances in Intelligent Systems and Computing, vol. 927. Springer, Cham (2019)
Faiz, M.F.I., Hussain, A., Marchang, N.: Machine learning based app-collusion detection in smartphones. In: 2019 IEEE 23rd International Symposium on Consumer Technologies (ISCT), Ancona, Italy (2019)
Guyon, I., Weston, J., Barnhill, S., Vapnik, V.: Gene selection for cancer classification using support vector machines. Mach. Learn. 46, 389–422 (2002). https://doi.org/10.1023/A:1012487302797
Abu-Mostafa, Y.S.: Learning From Data, pp. 1–213. AMLBook (2012)
Bishop, C.: Pattern Recognition and Machine Learning, pp. 1–711. Springer-Verlag, New York (2006)
Yerima, S.Y., Sezer, S.: DroidFusion: a novel multilevel classifier fusion approach for android malware detection. IEEE Trans. Cybern. 49(2), 453–466 (2019)
Blasco, J., Chen, T.M.: J. Comput. Virol. Hack. Tech. 14, 127 (2018). https://doi.org/10.1007/s11416-017-0296-4
Sculley, D.: Web-scale k-means clustering. In: Proceedings of the 19th International Conference on World Wide Web (WWW 2010), pp. 1177–1178. Association for Computing Machinery, New York (2010). https://doi.org/10.1145/1772690.1772862
Gu, Q., Han, J.: Clustered support vector machines. In: Proceedings of the Sixteenth International Conference on Artificial Intelligence and Statistics, vol. 31. PMLR (2013)
Suykens, J.A.K., Vandewalle, J.: Least squares support vector machine classifiers. Neural Process. Lett. 9, 293–300 (1999). https://doi.org/10.1023/A:1018628609742
Ma, Y., Zhang, Q., Li, D., Tian, Y.: LINEX support vector machine for large-scale classification. IEEE Access 7, 70319–70331 (2019)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2021 Springer Nature Switzerland AG
About this paper
Cite this paper
Faiz, M.F.I., Hussain, M.A., Marchang, N. (2021). Android Malware Detection Using Multi-stage Classification Models. In: Barolli, L., Poniszewska-Maranda, A., Enokido, T. (eds) Complex, Intelligent and Software Intensive Systems. CISIS 2020. Advances in Intelligent Systems and Computing, vol 1194. Springer, Cham. https://doi.org/10.1007/978-3-030-50454-0_23
Download citation
DOI: https://doi.org/10.1007/978-3-030-50454-0_23
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-50453-3
Online ISBN: 978-3-030-50454-0
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)