Abstract
Finding optimal adversarial dynamics between defenders and attackers in large network systems is a complex problem one can approach from several perspectives. The results obtained are often not satisfactory since they either concentrate on only one party or run very simplified scenarios that are hard to correlate with realistic settings. To truly find which are the most robust defensive strategies, the adaptive attacker ecosystem must be given as many degrees of freedom as possible, to model real attacking scenarios accurately. We propose a coevolutionary-based simulator called MOVE that can evolve both attack and defense strategies. To test it, we investigate several different but realistic scenarios, taking into account features such as network topology and possible applications in the network. The results show that the evolved strategies far surpass randomly generated strategies. Finally, the evolved strategies can help us to reach some more general conclusions for both attacker and defender sides.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Move simulator (2019). https://github.com/MOVESimulator/
Achleitner, S., La Porta, T., McDaniel, P., Sugrim, S., Krishnamurthy, S.V., Chadha, R.: Cyber deception: virtual networks to defend insider reconnaissance. In: Proceedings of the 8th ACM CCS International Workshop on Managing Insider Security Threats, MIST 2016, pp. 57–68. ACM, New York (2016)
Achleitner, S., La Porta, T., McDaniel, P., Sugrim, S., Krishnamurthy, S.V., Chadha, R.: Reconnaissance deception system prototype implementation (2016). https://github.com/deceptionsystem/master
Duan, Q., Al-Shaer, E., Haadi Jafarian, J.: Efficient random route mutation considering flow and network constraints. In: IEEE Conference on Communications and Network Security, CNS 2013, National Harbor, MD, USA, 14–16 October 2013, pp. 260–268. IEEE (2013)
Eiben, A.E., Smith, J.E.: Introduction to Evolutionary Computing. Springer, Berlin (2003)
Garcia, D., Lugo, A.E., Hemberg, E., O’Reilly, U.-M.: Investigating coevolutionary archive based genetic algorithms on cyber defense networks. In: Proceedings of the Genetic and Evolutionary Computation Conference Companion, GECCO 2017, pp. 1455–1462. ACM, New York (2017)
Hemberg, E., Zipkin, J.R., Skowyra, R.W., Wagner, N., O’Reilly, U.-M.: Adversarial co-evolution of attack and defense in a segmented computer network environment. In: Proceedings of the Genetic and Evolutionary Computation Conference Companion, GECCO 2018, pp. 1648–1655. ACM, New York (2018)
Kelly, J., DeLaus, M., Hemberg, E., O’Reilly, U.: Adversarially adapting deceptive views and reconnaissance scans on a software defined network. In: 2019 IFIP/IEEE Symposium on Integrated Network and Service Management (IM), pp. 49–54, April 2019
Lyon, G.F.: Nmap Network Scanning: The Official Nmap Project Guide to Network Discovery and Security Scanning. Insecure, Los Angeles (2009)
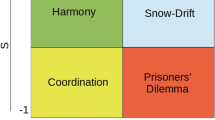
Miller, J.H.: The coevolution of automata in the repeated prisoner’s dilemma. J. Econ. Behav. Organ. 29(1), 87–112 (1996)
Panjwani, S., Tan, S., Jarrin, K.M., Cukier, M.: An experimental evaluation to determine if port scans are precursors to an attack. In: 2005 International Conference on Dependable Systems and Networks (DSN 2005), pp. 602–611, June 2005
Rush, G., Tauritz, D.R., Kent, A.D.: Coevolutionary agent-based network defense lightweight event system (CANDLES). In: Proceedings of the Companion Publication of the 2015 Annual Conference on Genetic and Evolutionary Computation, GECCO Companion 2015, pp. 859–866. ACM, New York (2015)
Prado Sánchez, D.: Visualizing adversaries: transparent pooling approaches for decision support in cybersecurity. M. Eng, thesis, Massachusetts Institute of Technology (2018)
Symantec: Preparing for a cyber attack, January 2017
Tankard, C.: Advanced persistent threats and how to monitor and deter them. Netw. Secur. 2011(8), 16–19 (2011)
Winterrose, M.L., Carter, K.M.: Strategic evolution of adversaries against temporal platform diversity active cyber defenses. In: Proceedings of the 2014 Symposium on Agent Directed Simulation, ADS 2014, pp. 9:1–9:9. Society for Computer Simulation International, San Diego (2014)
Winterrose, M.L., Carter, K.M., Wagner, N., Streilein, W.W.: Adaptive attacker strategy development against moving target cyber defenses. CoRR, abs/1407.8540 (2014)
Zaffarano, K., Taylor, J., Hamilton, S.: A quantitative framework for moving target defense effectiveness evaluation. In: Proceedings of the Second ACM Workshop on Moving Target Defense, MTD 2015, pp. 3–10. ACM, New York (2015)
Author information
Authors and Affiliations
Corresponding authors
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Knezevic, K., Picek, S., Jakobovic, D., Hernandez-Castro, J. (2020). What Is Your MOVE: Modeling Adversarial Network Environments. In: Castillo, P.A., Jiménez Laredo, J.L., Fernández de Vega, F. (eds) Applications of Evolutionary Computation. EvoApplications 2020. Lecture Notes in Computer Science(), vol 12104. Springer, Cham. https://doi.org/10.1007/978-3-030-43722-0_17
Download citation
DOI: https://doi.org/10.1007/978-3-030-43722-0_17
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-43721-3
Online ISBN: 978-3-030-43722-0
eBook Packages: Computer ScienceComputer Science (R0)