Abstract
With advances in information technology, more and more processes are automated; consequently, the information generated increases. The centralization of information becomes a necessity, so that companies are forced to send all this information from their branches to a single repository.
The transport of information throughout the network must be done in a safe and fast way, and it is necessary to use mechanisms that support this first factor, one of which is cryptography.
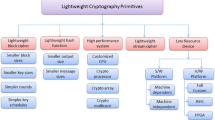
The present work describes particularities of some encryption methods and compares their performance in an environment with reduced hardware characteristics.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
González, D.U.W.G.K.: Revista Electrónica de la Facultad de Ingeniería (2014). [En línea]. http://revistas_electronicas.unicundi.edu.co/index.php/Revistas_electronicas/article/view/164. Último acceso: 2018
Granados, G.: Introducción a la criptografía, Revista Digital Universitaria, pp. 1–17 (2006)
ISO: «www.iso27000.es, [En línea]. http://www.iso27000.es/iso27000.html. Último acceso: 20 septiembre 2018
Arenas, X.: Sistemas distribuidos y seguridad web, 16 Octubre 2016. [En línea]. http://sistemasdistribuidosyseguridadweb.blogspot.com/2016/10/cifrado-simetrico-firmas-sells-y.html
Pousa, A.: Plataforma Virtual Educativa ITCA-FEPADE (2011). [En línea]. https://virtual.itca.edu.sv/Mediadores/cms/u63_esquema_general_de_un_sistema_de_cifrado_simetrico.html
R. A., Rojas, J.: Implementación de Protocolo de Cifrado TLS para mejorar la Seguridad de la capa de Transporte, Universidad Señor de Sipan (2017)
Lucena, M.: Criptografía y Seguridad en Computadores, Openlibra (2014)
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2020 Springer Nature Switzerland AG
About this paper
Cite this paper
Vivanco Herrera, H.R., Camacho Reina, A.G. (2020). Analysis of Cryptographic Technologies Based on ISO27001 Standards. In: Botto-Tobar, M., León-Acurio, J., Díaz Cadena, A., Montiel Díaz, P. (eds) Advances in Emerging Trends and Technologies. ICAETT 2019. Advances in Intelligent Systems and Computing, vol 1067. Springer, Cham. https://doi.org/10.1007/978-3-030-32033-1_37
Download citation
DOI: https://doi.org/10.1007/978-3-030-32033-1_37
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-32032-4
Online ISBN: 978-3-030-32033-1
eBook Packages: Intelligent Technologies and RoboticsIntelligent Technologies and Robotics (R0)