Abstract
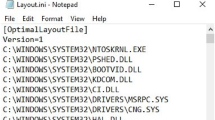
Timestamp patterns assist forensic analysts in detecting user activities, especially operations performed on files and folders. However, the Windows Subsystem for Linux feature in Windows 10 versions 1607 and later enables users to access and manipulate NTFS files using Linux command-line tools within the Bash shell. Therefore, forensic analysts should consider the timestamp patterns generated by file operations performed using Windows command-line utilities and Linux tools within the Bash shell.
This chapter describes the identification of timestamp patterns of various file operations in stand-alone NTFS and Ext4 filesystems as well as file interactions between the filesystems. Experiments are performed to analyze the anti-forensic capabilities of file timestamp changing utilities – called timestomping tools – on NTFS and Ext4 filesystems. The forensic implications of timestamp patterns and timestomping are also discussed.
Chapter PDF
Similar content being viewed by others
References
P. Albano, A. Castiglione, G. Cattaneo and A. De Santis, A novel anti-forensic technique for the Android OS, Proceedings of the International Conference on Broadband and Wireless Computing, Communications and Applications, pp. 380–385, 2011.
I. Baggili, A. BaAbdallah, D. Al-Safi and A. Marrington, Research trends in digital forensic science: An empirical analysis of published research, Proceedings of the Fourth International Conference on Digital Forensics and Cyber Crime, pp. 144–157, 2012.
F. Buchholz and E. Spafford, On the role of filesystem metadata in digital forensics, Digital Investigation, vol. 1(4), pp. 298–309, 2004.
B. Carrier, File System Forensic Analysis, Pearson Education, Upper Saddle River, New Jersey, 2005.
E. Casey, Digital stratigraphy: Contextual analysis of filesystem traces in forensic science, Journal of Forensic Sciences, vol. 63(5), pp. 1383–1391, 2018.
K. Conlan, I. Baggili and F. Breitinger, Anti-forensics: Furthering digital forensic science through a new, extended, granular taxonomy, Digital Investigation, vol. 18(S), pp. S66–S75, 2016.
A. Dewald and S. Seufert, AFEIC: Advanced forensic Ext4 inode carving, Digital Investigation, vol. 20(S), pp. S83–S91, 2017.
K. Fairbanks, An analysis of Ext4 for digital forensics, Digital Investigation, vol. 9(S), pp. S118–S130, 2012.
K. Fairbanks, C. Lee and H. Owen III, Forensic implications of Ext4, Proceedings of the Sixth Annual Workshop on Cyber Security and Information Intelligence Research, article no. 22, 2010.
J. Foster and V. Liu, Catch me, if you can, presented at Black Hat Japan, 2005.
S. Garfinkel, Anti-forensics: Techniques, detection and countermeasures, Proceedings of the Second International Conference on i-Warfare and Security, pp. 77–84, 2007.
R. Harris, Arriving at an anti-forensics consensus: Examining how to define and control the anti-forensics problem, Digital Investigation, vol. 3(S), pp. 44–49, 2006.
A. Harrison, Further Forensicating of Windows Subsystem for Linux, 1234n6 Blog (www.blog.1234n6.com/2017/10/further-forensicating-of-windows.html), October 17, 2017.
S. Ho, D. Kao and W. Wu, Following the breadcrumbs: Timestamp pattern identification for cloud forensics, Digital Investigation, vol. 24, pp. 79–94, 2018.
A. Mathur, M. Cao, S. Bhattacharya, A. Dilger, A. Tomas and L. Vivier, The new Ext4 filesystem: Current status and future plans, Proceedings of the Linux Symposium, vol. 2, pp. 21–34, 2007.
L. Nathan, A. Case, A. Ali-Gombe and G. Richard III, Memory forensics and the Windows Subsystem for Linux, Digital Investigation, vol. 26(S), pp. S3–S11, 2018.
M. Rogers, Anti-forensics: The coming wave in digital forensics, poster presentation at the Seventh Annual CERIAS Information Security Symposium, 2006.
J. Schicht, Mft2Csv, GitHub (www.github.com/jschicht/Mft2Csv/wiki/Mft2Csv), May 20, 2017.
B. Singh and U. Singh, Program execution analysis in Windows: A study of data sources, their formats and comparison of forensic capability, Computers and Security, vol. 74, pp. 94–114, 2018.
D. Wong, Ext4 Disk Layout (www.ext4.wiki.kernel.org/index.php/Ext4_Disk_Layout), February 18, 2019.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2019 IFIP International Federation for Information Processing
About this paper
Cite this paper
Singh, B., Gupta, G. (2019). Analyzing Windows Subsystem for Linux Metadata to Detect Timestamp Forgery. In: Peterson, G., Shenoi, S. (eds) Advances in Digital Forensics XV. DigitalForensics 2019. IFIP Advances in Information and Communication Technology, vol 569. Springer, Cham. https://doi.org/10.1007/978-3-030-28752-8_9
Download citation
DOI: https://doi.org/10.1007/978-3-030-28752-8_9
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-030-28751-1
Online ISBN: 978-3-030-28752-8
eBook Packages: Computer ScienceComputer Science (R0)