Abstract
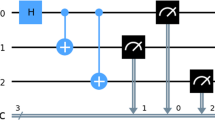
This paper divides into two main parts. The first one discusses authentication of quantum messages. The protocol proposed in [1] for one qubit message-length case is especially considered. The protocol uses a shared EPR pair as a secret key. In the second part, it is shown how such a protocol can be simulated using the Quantum-Octave package. Quantum-Octave is a set of functions for a Matlab-like numerical environment allowing calculations with general density matrices.
Similar content being viewed by others
References
M. Curty et al., “Qubit Authentication,” Phys. Rev. A 66, 022301 (2002).
D. W. Leung, “Quantum Vernam Cipher,” Quant. Inform. & Computation 2(1), 14–34 (2002).
H. Barnum et al., “Authentication of Quantum Messages,” Proc. 43rd Annual IEEE Symposium on the Foundations of Computer Science (FOCS’02), pp. 449–458, IEEE Press, 2002; quant-ph/0205128.
C. H. Bennett et al., “Purification of Noisy Entanglement and Faithful Teleportation Via Noisy Channels,” Phys. Rev. Lett. 76, 722–725 (1996).
B. Ömer, “Structured Quantum Programming,” PhD Thesis (TU Vienna, Vienna, 2003).
Author information
Authors and Affiliations
Additional information
The text was submitted by the author in English.