Abstract
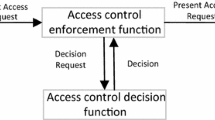
Physical security has received increased attention after 9/11. However, access control to physical units has not been explored much. On the other hand, there is a rich literature on access control to information. These two areas appear converging as seen by recent products and studies. However, use of different notations and implementation details make this convergence harder. We need to try to take this convergence at a more abstract level first. Although introduced about 10 years ago, security patterns have recently become accepted by industry and two books on this topic have appeared recently. Security patterns for information access control have appeared but now we extend this concept to access for physical units. The unification of information and physical access control is just beginning but the strong requirements of infrastructure protection will make this convergence to happen rapidly. Examining existing systems, industry standards and government regulations, we describe, in the form of patterns, the core set of features a physical access control system should have. The paper illustrates the structure and use of these patterns.
Chapter PDF
Similar content being viewed by others
References
SSPC135/LSS-WG: Physical access control with BACnet (October 2006), http://www.bacnet.org/bibliography/bac-10-06.pdf
Majdalawieh, M., Parisi-Presicce, F., Wijesekera, D.: Dnpsec: A security framework for dnp3 in SCADA systems. In: Internat. Joint Conf. on Computer Information and Systems Sciences and Engineering, Bridgeport, CT (December 10-20, 2005)
Buschmann, F., Meunier, R., Rohnert, H., Sommerlad, P., Stal, M.: Pattern-Oriented Software Architecture: A System of Patterns, vol. 1. Wiley, Chichester (1996)
Gamma, E., Helm, R., Johnson, R., Vlissides, J.: Design Patterns: Elements of Reusable Object-Oriented Software. Addison-Wesley, Boston, Mass (1994)
Schumacher, M., Fernandez, E.B., Hybertson, D., Buschmann, F., Sommerlad, P.: Security Patterns: Integrating security and systems engineering. J. Wiley & Sons, Chichester (2006)
Steel, C., Nagappan, R., Lai, R.: Core Security Patterns: Best Strategies for J2EE, Web Services, and Identity Management. Prentice Hall, Upper Saddle River, New Jersey (2005)
Fernandez, E.B., Pan, R.: A pattern language for security models. In: Procs, of PLoP (2001), http://hillside.net/plop/plop2001/accepted_submissions/accepted-papers.html
Priebe, T., Fernandez, E.B., Mehlau, J.I., Pernul, G.: A pattern system for access control. In: Procs. of the 18th Annual IFIP WG 11.3 Working Conference on Data and Applications Security, Sitges, Spain, pp. 235–249 (July 2004)
Desouza-Doucet, A.: Controlling access to physical locations, M.S. Thesis, dept. of computer science and eng., Florida Atlantic University (April 2006)
Fernandez, E.B., Sinibaldi, J.C.: More patterns for operating system access control. In: Proc. of the 8th European conference on Pattern Languages of Programs, pp. 381–398 (2003), http://hillside.net/europlop
Fernandez, E.B.: Security patterns (keynote talk and paper). In: Procs. of the Eigth International Symposium on System and Information Security - SSI2006, Sao Jose dos Campos, Brazil (November 08-10, 2006)
Ritter, D., Isler, B., Mundt, H., Treado, S.: Access control in bacnet. BACnet today (supplement to ASHRAE Journal), B26–B32 (November 2006)
Chandia, R., Gonzalez, J., Kilpatrick, T., Papa, M., Shenoi, S.: Security strategies for SCADA networks. In: Procs. First Annual IFIP WG 11.10 International Conference on Critical Infrastructure Protection
Bridging the great divide: The convergence of physical and logical security (August 2006), Imprivata( http://www.imprivata.com )
Martin, R.: In Designing Object-Oriented C++ Applications Using the Booch Method, Ch. 6. Prentice-Hall, Englewood Cliffs (1995)
Hengartner, U., Steenkiste, P.: Implementing access control to people location information. In: Procs. of the ACM Symposium on Access Control Models and Technologies (SACMAT 2004), ACM Press, New York (2004)
Boyer, J., Tan, K., Gunter, C.: Privacy-sensitive location information systems in smart buildings. In: Procs. of the 3rd Int. Conf. on Security for Pervasive Computing, York, England (April 2006)
Atluri, V., Shin, H.: Efficient enforcement of security policies based on tracking of mobile users. In: 20th Annual IFIP WG 11.3 Working Conference on Data and Applications Security (July 2006)
Corradi, A., Montanari, R., Tibaldi, D.: Context-based access control management in ubiquitous environments. In: Proceedings of the Third IEEE International Symposium on Network Computing and Applications (NCA 2004), IEEE Computer Society Press, Boston, MA (2004)
Huldenbosch, R., Salden, A., Bargh, M.S., Ebben, P.W.G., Reitsma, J.: Context-sensitive access control. In: Procs. of SACMAT 2005, pp. 111–119 (2005)
Warmer, J., Kleppe, A.: The Object Constraint Language, 2nd edn. Addison-Wesley, Reading (2003)
Ray, I., Li, N., Kim, D., France, R.: Using parameterized UML to specify and compose access control models. In: Proceedings of the Sixth IFIP WG 11.5 Conference on Integrity and Control in Information Systems. Lausanne, Switzerland (November 2003)
Delessy, N., Fernandez, E.B., Larrondo-Petrie, M.: A pattern language for identity management. In: Delessy, N. (ed.) Accepted for the 2nd IARIA Int. Multiconference on Computing in the Global Information Technology (ICCGI 2007), Guadeloupe, French Caribbean (March 4-9, 2007)
Author information
Authors and Affiliations
Editor information
Rights and permissions
Copyright information
© 2007 IFIP International Federation for Information Processing
About this paper
Cite this paper
Fernandez, E.B., Ballesteros, J., Desouza-Doucet, A.C., Larrondo-Petrie, M.M. (2007). Security Patterns for Physical Access Control Systems. In: Barker, S., Ahn, GJ. (eds) Data and Applications Security XXI. DBSec 2007. Lecture Notes in Computer Science, vol 4602. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-540-73538-0_19
Download citation
DOI: https://doi.org/10.1007/978-3-540-73538-0_19
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-540-73533-5
Online ISBN: 978-3-540-73538-0
eBook Packages: Computer ScienceComputer Science (R0)