Abstract
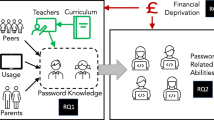
Development and integration of technology give organisations the opportunity to be globally competitive. However, the potential misuse of Information Technology (IT) is a reality that has to be dealt with by management, individuals and information security professionals. Numerous threats have emerged over time in the networked world, but so have the ways of alleviating these risks. However, security problems are still imminent – as highlighted by the plethora of media articles and research efforts. The insider risk is stated as being around 80% of security threats [1] in a company. With this statistic in mind, management has to plan how to allocate resources to counteract the risks. Very often, simple measures such as good password behaviour are overlooked or not rated high enough to include in all security awareness programmes. This paper will focus on a study that assesses password management of future IT professionals. It will be demonstrated how management and educators can use these results to focus their efforts in order to improve users’ password practices and thereby enhancing overall IT security.
Chapter PDF
Similar content being viewed by others
Keywords
References
Walton, R.: Balancing the insider and outsider threat. Computer Fraud & Security, November 8-11 (2006)
Dark, M.J.: Security education, Training and Awareness from a Human Performance Technology point of view. In: Whitman, M.E., Mattford, H.J. (eds.) Readings and Cases in the Management of Information Security, pp. 86–104. Thomson Course Technology, Boston (2006)
Burnett, M., Kleiman, D.: Perfect Passwords. Selection, Protection, Authentication. Syngress (2006)
Pfleeger, C.P., Pfleeger, S.L.: Security in Computing, 4th edn. Prentice Hall, Upper Saddle River (2007)
Wiedenbeck, S., Waters, J., Birget, J., Brodskiy, A., Memon, N.: PassPoints: Design and longitudinal evaluation of a graphical password system. International Journal of Human-Computer Studies 63, 102–127 (2005)
Singh, S., Cabraal, A., Demosthenous, C., Astbrink, G., Furlong, M.: Password sharing: implications for security design based on social practice. In: CHI Proceedings, April 27-May 3 (2007)
Forget, A., Chiasson, S., Van Oorschot, P., Biddle, R.: Improving text passwords through persuasion. In: Symposium on Usable Privacy and Security, July 23-25 (2008)
Kruger, H.A., Drevin, L., Steyn, T.: A framework for evaluating ICT security awareness. In: Proceedings of the 2006 ISSA Conference, Johannesburg, South Africa, July 5-7 (2006)
Gollmann, D.: Computer Security. Wiley (1999)
Vu, K.L., Proctor, R.W., Bhargav-Spantzel, A., Tai, B.L., Cook, J., Schultz, E.: Improving password security and memorability to protect personal and organizational information. International Journal of Human-Computer Studies 65, 744–757 (2007)
Berenson, M.L., Levine, D.M.: Basic Business Statistics. Concepts and Applications, 6th edn. Prentice Hall, Upper Saddle River (1996)
Furnell, S.: An assessment of website password practices. Computers & Security 26, 445–451 (2007)
Kruger, H.A., Drevin, L., Steyn, T.: Password management assessment. Technical Report. North-West University, South Africa, FABWI-N-RKW:2008-222 (2008)
Pareto Diagram, http://mot.vuse.vanderbilt.edu/mt322/Pareto.htm (accessed July 9, 2007)
Author information
Authors and Affiliations
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2013 IFIP International Federation for Information Processing
About this paper
Cite this paper
Drevin, L., Kruger, H., Steyn, T. (2013). Determinants of Password Security: Some Educational Aspects. In: Dodge, R.C., Futcher, L. (eds) Information Assurance and Security Education and Training. WISE WISE WISE 2013 2011 2009. IFIP Advances in Information and Communication Technology, vol 406. Springer, Berlin, Heidelberg. https://doi.org/10.1007/978-3-642-39377-8_28
Download citation
DOI: https://doi.org/10.1007/978-3-642-39377-8_28
Publisher Name: Springer, Berlin, Heidelberg
Print ISBN: 978-3-642-39376-1
Online ISBN: 978-3-642-39377-8
eBook Packages: Computer ScienceComputer Science (R0)