Abstract
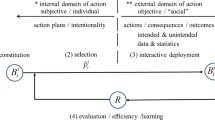
Here we introduce methodological guidelines for designing policies against organized crime. We employ the evolutionary ontology proposed by Kurt Dopfer for conceiving organized crime as the outcome of social, intelligent agents whose strategies evolve through time. To illustrate the use of this ontology we explore the case of corruption in public procurement processes in Colombia in which criminal organizations—groups of corrupt agents—converge spontaneously. The ontology leads to conceive corruption as a knowledge process that adapts according to the evolution of problem-solving rules that are created, used and discarded by agents that seek to attain personal gains by means of public resources. We also use an engineering perspective that favors model-aided design. We built a simulation model that illustrates how the dynamics of such evolving-rules systems can be conceptualized for exploring potential policies. The application of the evolutionary ontology shows why corruption exhibits self-organization: system-level patterns develop from spontaneous interactions that use only local information. Rule dynamics form a changing structure of rule-populations that adapt to novel environmental conditions and generate meta-stable adaptions that explain why corruption persists despite continuous challenges from the environment. This engineering approach forms the ground for proposing policies that instead of addressing the operant level of a social system (according to observed operations and data), should meet the dynamics of rules that govern those operations. Hence, the role of regulators shifts from “controllers” to inventors of selectionist environments that facilitate suitable change through the introduction or promotion of counter-crime rules, the design of selective pressures that favor the evolution of desirable rules and the attention to coordination gaps at the macro-structure. The recognition of organized crime as the outcome of an evolving-rules system changes the questions that orient policy-making and focuses on the redesign of evolving knowledge. Accordingly, our methodological guidelines address such evolutionary dynamics and can be applied to several forms of organized crime.




Similar content being viewed by others
References
Ackoff RL (2001) OR: after the post mortem. Syst Dyn Rev 17(4):341–346
Ackoff RL, Gharajedaghi J (1996) Reflections on systems and their models. Syst Res Behav Sci 13(1):13–23
Andreasen MM (1994) Modelling—the language of the designer. J Eng Des 5(2):103–115
Bauer JM, Herder PM (2009) Designing socio-technical systems. In: Meijers A (ed) Philosophy of technology and engineering sciences. Amsterdam, North Holland, pp 602–630
Bissell C, Dillon C (2012) Preface. In: Bissell C, Dillon C (eds) Ways of thinking, ways of seeing. Mathematical and other modelling in engineering and technology, vol 1. Springer, Berlin, Heidelberg, pp v–vii
Campbell DT (1960) Blind variation and selective retention in creative thought as in other knowledge processes. Psychol Rev 380–400
Campbell DT (1965) Variation and selective retention in socio-cultural evolution. In: Barringer HR, Blanksten GI, Mack RW (eds) Social change in developing areas: a reinterpretation of evolutionary theory. Schenkman, Cambridge, pp 19–49
Campbell DT (1987) Blind variation and selective retention in creative thought as in other knowledge processes. In: Radnitzky G, Bartley I (eds) Evolutionary epistemology, rationality, and the sociology of knowledge. Open Court, La Salle, pp 91–114
Cook SDN (2008) Design and responsibility. The interdependence of natural, artifactual, and human systems. In: Vermaas PE, Kroes P, Light A, Moore SA (eds) Philosophy and design. Springer, Netherlands, pp 259–269
Departamento Nacional de Planeación (2005) Información y corrupción en Colombia; victimización experiencia y percepción (Information and corruption in Colombia; victimization experience and perception). Editora Guadalupe, Bogota
Dodgson M, Gann DM, Salter A (2007) The impact of modelling and simulation technology on engineering problem solving. Tech Anal Strat Manag 19(4):471–489
Dopfer K (2001) Evolutionary economics: framework for analysis. In: Dopfer K (ed) Evolutionary economics: program and scope. Kluwer Academic Publishers, Boston/Dordrecht/London, pp 1–44
Dopfer K (2004) The economic agent as rule maker and rule user: Homo Sapiens Oeconomicus. J Evol Econ 14:177–195
Dopfer K (2005) Evolutionary economics: a theoretical framework. In: Dopfer K (ed) The evolutionary foundations of economics. Cambridge University Press, Cambridge, UK, pp 3–55
Dopfer K (2011) Mesoeconomics. Integrated analysis of systemic complexity and evolutionary change. In: Antonelli C (ed) Handbook on the economic complexity of technological change (Vol. Forthcoming). Edward Elgar Publisher
Dopfer K, Foster J, Potts J (2004) Micro–meso–macro. J Evol Econ 14:263–279
Dopfer K, Potts J (2004) Evolutionary realism: a new ontology for economics. J Econ Methodol 11(2):195–212
Dopfer K, Potts J (2008) The general theory of economic evolution. Routledge, London
Epstein JM (2008) Why model? J Artif Soc Soc Simul 11(4)
Fein E, Weibler J (2014) Review and shortcomings of literature on corruption in organizations in offering a multi-faceted and integrative understanding of the phenomenon. Behav Dev Bull 19(3):67–77
Garud R, Jain S, Tuertscher P (2008) Incomplete by design and designing for incompleteness. Organ Stud 29(3):351–371
Garud R, Kumaraswamy A, Sambamurthy V (2006) Emergent by design: performance and transformation at Infosys technologies. Organ Sci 17(2):277–286
Goldman SL (1984) The technē of philosophy and the philosophy of technology. Res in Philos Technol 115–144
Goldman SL (1990) Philosophy, engineering, and western culture. In: Durbin PT (ed) Broad and narrow interpretations of philosophy of technology. Amsterdam, Kluwer, pp 125–152
Isaza O, Restrepo JD, Hincapié SM (2005) Estrategias de corrupción en Colombia (Corruption Strategies in Colombia). Instituto Popular de Capacitación, Medellin
Koepsell DR (1999) Introduction to applied ontology: the philosophical analyses of everyday objects. Am J Econ Soc 58(2):217–220
Kroes P (2012) Engineering design. In: Kroes P (ed) Technical artefacts: creations of mind and matter. Springer, Dordrecht, pp 127–161
Krohs U (2008) Co-designing social systems by designing technical artifacts. In: Vermaas PE, Kroes P, Light A, Moore SA (eds) Philosophy and design. Springer, Netherlands, pp 233–245
Kühn S, Sherman LB (2014) Curbing corruption in public procurement: a practical guide. Transparency International, Berlin
Mayr E (1969) Footnotes on the philosophy of biology. Philos Sci 36(2):197–202
Morales A (2010) Cifras del fraude y la corrupción (Fraud and Corruption Figures). El Colombiano, March 27
Norström P (2013) Engineers’ non-scientific models in technology education. Int J Technol Des Educ 23(2):377–390
Olaya C (2015) Cows, agency, and the significance of operational thinking. Syst Dyn Rev 31(4):183–219
Olaya C, Gómez-Quintero J, Salas D (2012) Ontology in action: urban mobility as evolving knowledge. Proceedings of the 24th annual European association for evolutionary political economy conference. Cracow University of Economics, Cracow, Poland
Ostrom V (1980) Artishanship and artifact. Public Adm Rev 40(4):309–317
Remington R, Boehm-Davis DA, Folk CL (2012) Natural and engineered systems. In: Introduction to humans in engineered systems. John Wiley & Sons, Hoboken, pp 7–13
Republic of Colombia (2013) Decree 1510 of 2013
Republic of Colombia & World Bank (2002) Corrupción, desempeño institucional y gobernabilidad en Colombia (Corruption, Institutional Performance and Governability in Colombia). Bogota
Salas D, Olaya C (2009) No more “Learning”: selectionist education for the classroom. In Proceedings of the 21st Annual Meeting of the Human Behavior and Evolution Society. HBES: Fullerton, California State University, CA, USA
Salcedo-Albarán E, Zuleta MM, Beltrán I, Rubio M (2007) Corrupción, cerebro y sentimientos. Grupo Método, Bogotá
Simon HA (1996) The sciences of the artificial, 3rd edn. MIT Press, Cambridge
Sober E (1980) Evolution, population thinking, and essentialism. Philos Sci 47(3):350–383
Sterman J (2000) Business dynamics. Systems thinking and modeling for a complex. World.McGraw-Hill, Boston, MA
Transparencia por Colombia (2015) Cuarta encuesta nacional sobre prácticas contra el soborno en empresas colombianas (Fourth National Survey on Practices Against Bribery in Colombian Firms). Cuadernos de transparencia 23
Transparency International (2013) Corruption perception index – Colombia. Transparency International, Berlin
United Nations (2013) Guidebook on anti-corruption in public procurement and the management of public finances. United Nations, New York
Windrum P, Fagiolo G, Moneta A (2007) Empirical validation of agent-based models: alternatives and prospects. J Artif Soc Soc Simul 10(2)
Author information
Authors and Affiliations
Corresponding author
Ethics declarations
Ethical approval
This article does not contain any studies with human participants performed by any of the authors.
Annex 1 – model parameters and tests
Annex 1 – model parameters and tests
Sensitivity analysis
Sensitivity analysis asks whether results change in ways important to the purpose as assumptions and parameters change; this type of analysis should focus on examining those relationships and parameters that are uncertain and likely to be influential (Sterman 2000). Windrum et al. (2007) also suggest that sensitivity analysis should explore how results depend on i) micro and macro parameters, ii) initial conditions, and iii) across run variability induced by stochastic elements. The results from these tests can be categorized in: a) numerical sensitivity, b) behavior mode sensitivity, and c) policy sensitivity (Sterman, 2000). Based on this categorization, we performed sensitivity tests with parameters upon which we are uncertain of their estimation; these are: corruption threshold, denounce rate of contractors and minimum accumulated allegations by citizens required for the local government to present allegations to controllers. We varied these parameters and focused on the behavior rule #4 use since it is the corrupt rule that entails higher complexity (association among groups of corrupt contractor and groups of corrupt public officers). In the following table we brief the specifications and conclusions of these tests; we also present the simulation results of the tests in the subsequent graphs. Because there were no observed changes in behavioral patterns, the uncertainty of the estimation for these parameters is not of concern in terms of the conclusions that can derive from this model, particularly considering that the outcomes of this model are merely illustrative and aim to shed light towards public policy broad guidelines.
Figure 5 shows that use of rule #4 has numeric sensitivity to variations in propensity for corruption parameters. However, the behavior mode through the simulation does not change. For lower values of propensity for corruption, the use of rule #4 decreases with regard to those simulations with higher levels of propensity for corruption.
Figure 6 shows that the use of rule #4 decreases when the denounce rate increases and vice versa. However there is no change in the behavior mode throughout the simulations.
In the model, allegations from local governments are a response to an accumulation of citizen allegations. Figure 7 shows that the use of rule #4 does not seem to change when this parameter changes. Significant increases in the use of rule #4 are observed at the last part of the simulation when this parameter has values of 700 and 750, however there is no significant change in the behavior mode.
Extreme conditions
With the Extreme Conditions test, we examined if the model behaves in a realistic fashion when extreme inputs are explored (Sterman, 2000) such as no propensity for corruption, total propensity for corruption, no public officers involved in procurement processes, or large numbers of public officers involved in procurement processes. The description and results of this test are summarized in Table 10; we also show the simulation results of the tests in the subsequent graphs. From the results we can conclude that the rule dynamics of the model is consistent with what is expected when we assume extreme values for critical parameters.
Figure 8 shows three simulations: 1. No corruption (Corruption Threshold = 100), 2. Normal Corruption Threshold (Corruption Threshold = 36) and 3. Absolut corruption (Corruption Threshold = 0). The simulations show that in the case of No corruption, rule #4 is never used while in the case of Absolut corruption the utilization of rule#4 is largely increased with respect to the Normal Corruption Threshold used in the model. These results show that the model responds accordingly to extreme conditions.
Figure 9 shows three simulations: 1. No public officers in process (Public officers = 0), 2. Normal number of Public Officers in process (Public officers = 3, value used in the model), and 3. Large number of public officers in process (Public officers = 9). For the first case, No public officers in process, rule#4 is not used because there are no public officers with whom to make corrupt alliances with. Conversely, in the case of Large numbers of public officers in the process, the chance of making a corrupt alliance with several public officers is higher since there are more public officers; consequently, the use of rule#4 increases significantly. These results are coherent with the expected behavior.
Further analysis could be extended in terms of how the model responds to extreme conditions. Analysis could focus not only in the dynamics of the use of rule#4 but as well in the use of the other three rules. This test, as well as the sensitivity analysis serve as illustrative examples of how this type of models could be tested with respect to its purpose from an engineering perspective.
Rights and permissions
About this article
Cite this article
Olaya, C., Guzmán, L. & Gomez-Quintero, J. An engineering perspective for policy design: self-organizing crime as an evolutionary social system. Trends Organ Crim 20, 55–84 (2017). https://doi.org/10.1007/s12117-016-9282-3
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12117-016-9282-3