Abstract
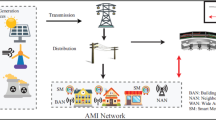
The development of smart grid depends on increased deployment of two-way communication to improve its efficiency and reliability of power delivery. However, this additional dependency also expands the risk from pollution attacks, which consist of injecting malicious packets in the network. The pollution attacks are amplified by the network coding process, resulting in a greater damage to the state estimation and decision making. In this paper, we address this issue by designing an efficient authentication protocol, named EAPA, for the smart grid communication. The proposed scheme allows not only recipient nodes, but also intermediate nodes, to verify the integrity and origin of the packets received without having to decode, and thus detect and discard the malicious packets in transit that fail the verification. By this means, the pollution is canceled out before reaching the destinations. Security analysis demonstrates that the EAPA can be resilient to data/tag pollution attacks and replay attacks. Performance evaluation results show that our EAPA can reduce much more communication overhead than Wu’s scheme.



Similar content being viewed by others
References
Lu R, Liang X, Li X, Lin X, Shen X (2012) EPPA: an efficient and privacy-preserving aggregation scheme for secure smart grid communications. IEEE Trans Parallel Distrib Syst 23(9):1621–1631
Zeng R, Jiang Y, Lin C, Shen X (2012) Dependability analysis of control center networks in smart grid. IIEEE Trans Parallel Distrib Syst 23(9):1721–1730
Abur A, Exposito AG (2004) Power system state estimation: theory and implementation. CRC Press
Li H, Lu R, Zhou L, Yang B, Shen X (2013) An efficient merkle tree based authentication scheme for Smart Grid. IEEE Syst J 99:1–9
Lai C, Li H, Lu R, Shen X (2013) SE-AKA: a secure and efficient group authentication and key agreement protocol for LTE networks. Comput Netw 57:3492–3510
Esmalifalak M, Han Z, Song L (2012) Effect of stealthy bad data injection on network congestion in market based power system. In: WCNC, pp 2468–2472
Huang Y, Esmalifalak M, Nguyen H, Zheng R et al (2013) Bad data injection in smart grid: attack and defense mechanisms. IEEE Commun Mag 51(1):27–33
Liu Y, Ning P, Reiter MK (2011) False data injection attacks against state estimation in electric power grids. ACM Trans Inf Syst Secur 14(1):1–13
Xie L, Mo Y, Sinopoli B (2010) False data injection attacks in electricity markets. In: Smart Grid Comm, pp 226–231
Yu Z, Guan Y, Zhuang W, Shen XS (2005) A key pre-distribution scheme using deployment knowledge for wireless sensor networks. In: IPSN, pp 261–268
Wu X, Xu Y, Yuen C, Xiang L (2014) A tag encoding scheme against pollution attack to linear network coding. IEEE Trans Parallel Distrib Syst 25(1):33–42
Wang Y, Gu D, Wen M, Xu J, Li H (2010) Denial of service detection with hybrid fuzzy set based feed forward neural network. In: ISNN, pp 576–585
Agrawal S, Boneh D (2009) Homomorphic MACs: MAC-based integrity for network coding. Applied cryptography and network security, Springer book, 292–305
Wen M, Zheng Y, Li H, Chen K (2007) A hierarchical composition of LU matrix-based key distribution scheme for sensor networks. In: SSDU, pp 608–620
Blake I, Seroussi G, Smart N, Cassels J (2005) Advances in elliptic curve cryptography London Mathematical Society Lecture Note Series. Cambridge University Press
Jaggi S, Langberg M, Katti S, Ho T, Katabi D, Medard M, Effros M (2008) Resilient network coding in the presence of Byzantine adversaries. IEEE Trans Inf Theory 54(6):2596–2603
Koetter R, Kschischang FR (2008) Coding for errors and erasures in random network coding. IEEE Trans Inf Theory 54(8):3579–3591
Le A, Markopoulou A (2011) TESLA-based defense against pollution attacks in P2P systems with network coding. In: EEE NetCod 1–7
Le A, Markopoulou A (2012) Cooperative defense against pollution attacks in network coding using SpaceMac. IEEE JSAC Coop Netw Chall Appl 30(2):442–449
Li H, Zheng Y, Chen K, Wen M (2006) A locally group key management with revocation capability for sensor networks. ICSNC
Yang Y, Li H, Wen M, Luo H, Lu R Achieving ranked range query in smart grid auction market. ICC 2014, Sydney, Australia, to appear
Liu D, Li H, Yang Y, Yang H Achieving multi-authority access control with efficient attribute revocation in smart grid. ICC 2014, Sydney, Australia, to appear
Boneh D, Freeman D, Katz J, Waters B (2009) Signing a linear subspace: signature schemes for network coding. In: PKC, pp 68–87
Jiang Y, Zhu H, Shi M, Shen X, Lin C (2010) An efficient dynamic identity based signatur scheme for secure network coding. Comput Netw 54(1):28–40
Zhang P, Jiang Y, Lin C, Yao H, Wasef A, Shen XS (2011) Padding for orthogonality: efficient subspace authentication for network coding. In: INFOCOM, pp 261–268
Liang M, Kan H (2013) An efficient hybrid cryptographic scheme for wireless sensor network with network coding. IEICE Trans Fundam E96-A(9):1889–1894
Acknowledgments
This work is supported by the National Natural Science Foundation of China under Grant No. 61373152, No. 61272437 and No. 61202369, Innovation Program of Shanghai Municipal Education Commission No. 13ZZ131, No.14ZZ150 and No.14YZ 129. Foundation Key Project of Shanghai Science and Technology Committee No. 12JC1404500, and Project of Shanghai Science and Technology Committee No. 12510500700.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Wen, M., Lei, J., Bi, Z. et al. EAPA: An efficient authentication protocol against pollution attack for smart grid. Peer-to-Peer Netw. Appl. 8, 1082–1089 (2015). https://doi.org/10.1007/s12083-014-0283-1
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12083-014-0283-1