Abstract
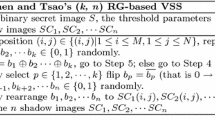
In (k, n) visual secret sharing (VSS), a secret image is generated into n shadow images printed onto transparencies and distributed to n associated participants. The secret image can be recovered by stacking any k or more shadow images and human visual system without cryptographic computation. The previous VSS schemes neglected participants increasing. However, in some applications, some new shadow images need to be generated because some new participants join the secret sharing. In this paper, we consider the new participants increasing issue as well as propose a participants increasing method only from the n original shadow images generated by previous existed (k, n) threshold random grids-based visual secret sharing (RGVSS). Without knowing the original generation algorithm and the original secret image, q new shadow images can be obtained from the original n shadow images without reprinting the original ones, as a result \((k, n+q)\) threshold RGVSS will be gained. Theoretical analysis and experiments are conducted to evaluate the security and efficiency of the proposed scheme.








Similar content being viewed by others
References
Naor, M., Shamir, A.: Visual cryptography. In: Advances in Cryptology EUROCRYPT’94 Lecture Notes in Computer Science, Workshop on the Theory and Application of Cryptographic Techniques, May 9C12, Perugia, Italy, pp. 1–12. Springer (1995)
Yang, C.N., Sun, L.Z., Yan, X., Kim, C.: Design a new visual cryptography for human-verifiable authentication in accessing a database. J. Real-Time Image Process. 12(2), 483–494 (2015)
Wang, D., Zhang, L., Ma, N., Li, X.: Two secret sharing schemes based on boolean operations. Pattern Recognit. 40(10), 2776–2785 (2007)
Wang, Z., Arce, G.R., Di Crescenzo, G.: Halftone visual cryptography via error diffusion. IEEE Trans. Inf. Forensics Secur. 4(3), 383–396 (2009)
Weir, J., Yan, W.: A comprehensive study of visual cryptography. In: Transactions on DHMS V, LNCS 6010, pp. 70–105. Springer, Berlin (2010)
Wu, X., Sun, W.: Improving the visual quality of random grid-based visual secret sharing. Signal Process. 93(5), 977–995 (2013)
Yan, X., Wang, S., Niu, X.: Threshold construction from specific cases in visual cryptography without the pixel expansion. Signal Process. 105, 389–398 (2014)
Luo, H., Yu, F., Pan, J.S., Lu, Z.M.: Robust and progressive color image visual secret sharing cooperated with data hiding. In: Eighth International Conference on Intelligent Systems Design and Applications, 2008, vol. 3, pp. 431–436. ISDA’08, Kaohsiung, Taiwan. IEEE (2008)
Li, P., Ma, P.J., Su, X.H., Yang, C.N.: Improvements of a two-in-one image secret sharing scheme based on gray mixing model. J. Vis. Commun. Image Represent. 23(3), 441–453 (2012)
Yan, X., Wang, S., Niu, X., Yang, C.N.: Generalized random grids-based threshold visual cryptography with meaningful shares. Signal Process. 109, 317–333 (2015)
Zhou, Z., Arce, G.R., Di Crescenzo, G.: Halftone visual cryptography. IEEE Trans. Image Process. 15(8), 2441–2453 (2006)
Liu, F., Wu, C.: Embedded extended visual cryptography schemes. Inf. Forensics Secur. IEEE Trans. 6(2), 307–322 (2011)
Yan, X., Wang, S., Niu, X., Yang, C.N.: Halftone visual cryptography with minimum auxiliary black pixels and uniform image quality. Digit. Signal Process. 38, 53–65 (2015)
Yang, C.N.: New visual secret sharing schemes using probabilistic method. Pattern Recognit. Lett. 25(4), 481–494 (2004)
Cimato, S., De Prisco, R., De Santis, A.: Probabilistic visual cryptography schemes. Comput. J. 49(1), 97–107 (2006)
Guo, T., Liu, F., Wu, C.: Threshold visual secret sharing by random grids with improved contrast. J. Syst. Softw. 86(8), 2094–2109 (2013)
Fu, Z.x., Yu, B.: Visual cryptography and random grids schemes. In: Digital-Forensics and Watermarking, pp. 109–122. Springer, Auckland (2014)
Li, P., Yang, C.N., Wu, C.C., Kong, Q., Ma, Y.: Essential secret image sharing scheme with different importance of shadows. J. Vis. Commun. Image Represent. 24(7), 1106–1114 (2013)
Yan, X., Liu, X., Yang, C.N.: An enhanced threshold visual secret sharing based on random grids. J. Real-Time Image Process. (2015). doi: 10.1007/s11554-015-0540-4
Yan, X., Lu, Y., Huang, H., Liu, L., Wan, S.: Clarity Corresponding to Contrast in Visual Cryptography, pp. 249–257. Springer, Singapore (2016)
Shyu, S.J.: Visual cryptograms of random grids for general access structures. Circuits Syst. Video Technol. IEEE Trans. 23(3), 414–424 (2013)
Lin, S.J., Lin, J.C.: VCPSS: a two-in-one two-decoding-options image sharing method combining visual cryptography (VC) and polynomial-style sharing (PSS) approaches. Pattern Recognit. 40(12), 3652–3666 (2007)
Yang, C.N., Ciou, C.B.: Image secret sharing method with two-decoding-options: lossless recovery and previewing capability. Image Vis. Comput. 28(12), 1600–1610 (2010)
Acknowledgements
The authors would like to thank the anonymous reviewers for their valuable comments. This work is supported by the National Natural Science Foundation of China (Grant Number: 61602491).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Yan, X., Lu, Y. Participants increasing for threshold random grids-based visual secret sharing. J Real-Time Image Proc 14, 13–24 (2018). https://doi.org/10.1007/s11554-016-0639-2
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11554-016-0639-2