Abstract
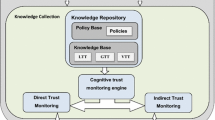
Free-rider problem greatly influences the performance of unstructured networks (like ad hoc or peer-to-peer networks). To solve such problem, we focus on trust management framework, which is intended to stimulate nodes to cooperate with each other and prevent free-riders. Currently, the existing trust management framework can be classified into trust establishment framework and reputation-based framework. None of them, however, was explicitly designed with the considerations on neutrality, which is indispensable issue when devising a network system. Therefore, we attempt to march towards the design of neutral trust management framework in this paper. We firstly investigate the relation between neutrality and trust definition, and identify the requirements for design of neutral trust management framework. Then, we focus on trust management of one kind of typical unstructured networks, mobile ad hoc network (MANET). We design a neutral trust management framework of MANET to meet the clarified design requirements. Further, we perform analysis on our proposed framework, which shows our proposal can achieve neutrality under the location-dependent attack of free-rider in MANET.
Similar content being viewed by others
References
Bloom B (1970) Space/time trade-offs in hash coding with allowable errors. Commun ACM 13:422–426
Buchegger S, Le Boudec J-Y (2002) Performance analysis of the CONFIDANT protocol (cooperation of nodes—fairness in dynamic ad-hoc networks). In: Proceedings of ACM MobiHoc 2002, Atlanta, USA, Sept
Buchegger S, Le Boudec J-Y (2004) A robust reputation system for P2P and mobile ad-hoc networks. In: Proceedings of P2PEcon 2004, Harvard University, Cambridge, MA, USA, June
Crowcroft J (2007) Net neutrality—the technical side of the debate: a white paper. ACM Comput Commun Rev 37(1):49–55
Davison A (2003) Statistical models. Cambridge series in statistical and probabilistic mathematics. Cambridge University Press, Cambridge
Ferdous R, Muthukkumarasamy V, Sattar A (2010) Trust formalization in mobile ad-hoc networks. In: IEEE 24th international conference on advanced information networking and applications workshops, pp 351–356
Ganeriwal S, Srivastava M (2004) Reputation-based framework for high integrity sensor networks. In: Proceedings of the ACM workshop on security of ad hoc and sensor networks (SASN 2004), Washington, DC, USA, Oct 25
Grandison T, Sloman M (2000) A survey of trust in internet applications. IEEE Commun Surv Tutor Fourth Quarter 3(4):2–16
Jøsang A, Ismail R (2002) The beta reputation system. In: Proceedings of the 15th bled conference on electronic commerce, Bled, Slovenia, 17–19 June
Kamvar SD, Schlosser MT, Garcia-Molina H (2003) The eigentrust algorithm for reputation management in P2P networks. In: Proceedings of 12th international World Wide Web conferences, May
Li R, Li J, Liu P, Chen H-H (2007) An objective trust management framework for mobile ad hoc networks. In: IEEE 65th vehicular technology conference VTC 2007 spring (IEEE VTC 2007 spring), 23–25 April, pp 56–60
Marti S, Giuli T, Lai K, Baker M (2000) Mitigating routing misbehavior in mobile ad hoc networks. In: Proceedings of MobiCom 2000, Aug, pp 255–265
Shankaran R, Varadharajan V, Orgun MA, Hitchens M (2009) Critical issues in trust management for mobile ad-hoc networks. In: Proceedings of the 10th IEEE international conference on information reuse & integration, pp 97–100
Sun Y, Han Z, Yu W, Liu KJR (2006) A trust evaluation framework in distributed networks vulnerability analysis and defense against attacks. In: Proceedings of the IEEE Infocom 2006, Apr, Barcelona, Spain
Theodorakopoulos G, Baras S (2006) On trust models and trust evaluation metrics for ad hoc networks. IEEE J Sel Areas Commun, Special Issue on Security in Wireless Ad-Hoc Networks, Feb 2006
Zouridaki C, Mark BL, Hejmo M, Thomas RK (2005) A quantitative trust establishment framework for reliable data packet delivery in MANETs. In: Proceedings of the 3rd ACM workshop on security of ad hoc and sensor networks (SASN 2005), Alexandria, VA, USA, November 7
Theodorakopoulos G, Baras JS (1995) Malicious users in unstructured networks. MIT Press, Cambridge
Yang X, Tsudik G, Liu X (2006) A technical approach to net neutrality. In: Fifth workshop on hot topics in networks (ACM HotNets-V), Irvine
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Li, R., Li, J. Requirements and design for neutral trust management framework in unstructured networks. J Supercomput 64, 702–716 (2013). https://doi.org/10.1007/s11227-010-0502-3
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11227-010-0502-3