Abstract
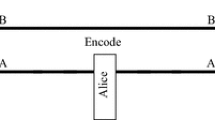
A security layer for the asymptotically secure ping-pong protocol is proposed and analyzed in the paper. The operation of the improvement exploits inevitable errors introduced by the eavesdropping in the control and message modes. Its role is similar to the privacy amplification algorithms known from the quantum key distribution schemes. Messages are processed in blocks which guarantees that an eavesdropper is faced with a computationally infeasible problem as long as the system parameters are within reasonable limits. The introduced additional information preprocessing does not require quantum memory registers and confidential communication is possible without prior key agreement or some shared secret.
Article PDF
Similar content being viewed by others
References
Beige A., Englert B.G., Kurtsiefer C., Weinfurter H.: Secure communication with a publicly known key. Act. Phys. Pol. 101(3), 357–368 (2002)
Boström K., Felbinger T.: Deterministic secure direct communication using entanglement. Phys. Rev. Lett. 89(18), 187902 (2002)
Boström K., Felbinger T.: On the security of the ping-pong protocol. Phys. Lett. A 372(22), 3953–3956 (2008)
Cai Q.Y., Li B.W.: Improving the capacity of the Boström-Felbinger protocol. Phys. Rev. A 69(5), 054301 (2004)
Deng F.G., Long G.L., Liu X.S.: Two-step quantum direct communication protocol using the Einstein-Podolsky-Rosen pair block. Phys. Rev. A 68(4), 042317 (2003)
Deng F.G., Long G.L., Wang Y., Xiao L.: Increasing the efficiencies of random-choice-based quantum communication protocols with delayed measurement. Chin. Phys. Lett. 21(11), 2097–2100 (2004)
Fu-Guo D., Gui-Lu L.: Quantum privacy amplification for a sequence of single qubits. Commun. Theor. Phys. 46(3), 443 (2006)
ISO/IEC 9797-1: Information technology—Security techniques—Message Authentication Codes (MACs)-Part 1: Mechanisms using a block cipher (1999)
Long G.L., Liu X.S.: Theoretically efficient high-capacity quantum-key-distribution scheme. Phys. Rev. A 65(3), 032302 (2002)
Ostermeyer M., Walenta N.: On the implementation of a deterministic secure coding protocol using polarization entangled photons. Opt. Commun. 281(17), 4540–4544 (2008)
Vasiliu E.V.: Non-coherent attack on the ping-pong protocol with completely entangled pairs of qutrits. Quantum Inf. Process. 10, 189–202 (2011)
Wang C., Deng F.G., Li Y.S., Liu X.S., Long G.L.: Quantum secure direct communication with high-dimension quantum superdense coding. Phys. Rev. A 71(4), 044305 (2005)
Wang C., Deng F.G., Long G.L.: Multi-step quantum secure direct communication using multi-particle Green-Horne-Zeilinger state. Opt. Commun. 253(1), 15–20 (2005)
Wójcik A.: Eavesdropping on the ping-pong quantum communication protocol. Phys. Rev. Lett. 90(15), 157901 (2003)
Zawadzki, P.: Security of ping-pong protocol based on pairs of completely entangled qudits. Quantum Inf. Process. pp. 1–12 (2011). doi:10.1007/s11128-011-0307-1. http://dx.doi.org/10.1007/s11128-011-0307-1
Zhang Z., Man Z., Li Y.: Improving Wójciks eavesdropping attack on the ping-pong protocol. Phys. Lett. A 333, 46–50 (2004)
Open Access
This article is distributed under the terms of the Creative Commons Attribution License which permits any use, distribution, and reproduction in any medium, provided the original author(s) and the source are credited.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
Open Access This article is distributed under the terms of the Creative Commons Attribution 2.0 International License (https://creativecommons.org/licenses/by/2.0), which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.
About this article
Cite this article
Zawadzki, P. Improving security of the ping-pong protocol. Quantum Inf Process 12, 149–155 (2013). https://doi.org/10.1007/s11128-012-0363-1
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11128-012-0363-1