Abstract
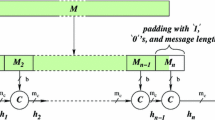
In this paper, we introduce a solution for ensuring data integrity using cryptographic one-way hash functions. The cryptographic security of such hash functions was estimated by us in detail for different kinds of attacks. We propose several new schemes for increasing the security of one-way hash functions without reformation of its internal algorithms. Also we outline schemes with the best speed and security level. We show that the Schneier method of suffix superposition has a serious drawback. In this article, we also suggest the method of constructing collision resistant one-way hash functions from standard well-known hash functions. Therefore, the proposed schemas can be used to upgrade the majority of cryptographic one-way functions, such as MD4, MD5, RIPEMD, SHA, GOST 34 11-94.
Similar content being viewed by others
References
A. Menezes, P. Oorschot, and S. Vanstone, Handbook of Applied Cryptography, CRC Press (1996).
B. Schneier, Applied Cryptography. Protocols, Algorithms, and Source Code in C, Wiley (2002).
X. Wang, D. Feng, X. Lai, and H. Yu, “Collisions for hash functions MD4, MD5, HAVAL-128, and RIPEMD,” in: CRYPTO 2004.
Author information
Authors and Affiliations
Corresponding author
Additional information
Translated from Fundamentalnaya i Prikladnaya Matematika, Vol. 15, No. 5, pp. 171–179, 2009.
Rights and permissions
About this article
Cite this article
Levin, V.Y. Increasing the security of hash functions. J Math Sci 172, 734–739 (2011). https://doi.org/10.1007/s10958-011-0215-z
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10958-011-0215-z