Abstract
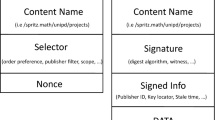
Named data networking (NDN) is an emerging networking paradigm that is considered as one of the promising candidates for next-generation Internet architecture. To be a viable Internet architecture, NDN must be resilient against current and emerging threats. This paper focuses on how to detect and mitigate the Interest flooding attack (IFA) in NDN, which can excessively consume the resource of each involved router by flooding too many malicious Interest packets with fake names. In this paper, to counter IFA, an architecture called Cooperative-Filter is proposed. It detects IFA using fuzzy logic, and mitigates it based on the cooperation between routers at the granularity of per-prefix-per-interface, by taking advantages of the state statistics of each router. Moreover, the performance of Cooperative-Filter is evaluated, based on both effect of it on reducing memory resource consumption of each involved router and the effect on increasing Interest satisfaction rate for legitimate users when suffering IFA as well as on decreasing the Interest-retrieving delay. Simulation results demonstrate that Cooperative-Filter can detect IFA and effectively mitigate its damage effect on NDN. To the best of our knowledge, this is the first attempt to design an IFA countermeasure embedding with fuzzy logic as well as countering IFA at the granularity of per-prefix-per-interface.











Similar content being viewed by others
References
Afanasyev A, Moiseenko I, Zhang L (2012) ndnSIM: NDN simulator for NS-3. NDN. Technical, Report NDN-0005
Afanasyev A, Mahadevan P, Uzun E, Zhang L (2013) Interest flooding attack and countermeasures in named data networking. In: Proceedings of IFIP networking
Carofiglio G, Muscariello L, Gallo M (2011a) Bandwidth and storage sharing performance in information centric networking. In: Proceedings of the ACM SIGCOMM workshop on information-centric networking (ICN)
Carofiglio G, Gallo M, Muscariello L, Perino D (2011b) Modeling data transfer in content centric networking. In: Proceedings of the 23rd international teletraffic congress
Carofiglio G, Gallo M, Muscariello L, Perino D (2011c) Modeling data transfer in content centric networking(extended version). In Technical Report. http://perso.rd.francetelecom.fr/muscariello/report-itc-transport
Dai H, Wang Y, Fan J, Liu B (2013) Mitigate DDoS attacks in NDN by interest traceback. In: Proceedings of IEEE INFOCOM NOMEN workshop, Turin, Italy
Dannewitz (2009) NetInf: an information-centric design for the future internet. In: Proceedings of the 3rd GI/ITG KuVS workshop on the future internet, Munich, Germany, May
Fotiou N, Nikander P, Trossen D, Polyzos GC (2010) Developing information networking further: from PSIRP to PURSUIT. In: Proceedings of the international ICST conference broadband communications, networks, and systems (BROADNETS), 2010 (invited paper), Oct 2010
Gasti P, Tsudik G, Uzun E, Zhang L (2012) DoS & DDoS in named-data networking. ArXive-prints. Tech Rep 1208.0952v2, Aug 2012
Jacobson V, Semtters DK, Thornton JD, Plass MF, Briggs NH, Braynard RL (2012) Networking named content. Commun ACM 55(1):117–124
Jacobson V, Smetters DK, Thornton JD, Plass MF, Briggs NH, Braynard RL (Dec 2009) Networking named content. In: Proceedings of the ACM CoNEXT, Rome, Italy
Koponen T, Ermolinskiy A, Chawla M, Kim KH, Stoica I, gon Chun B, Shenker S (2007) A data oriented (and beyond) network architecture. In: Proceedings of the SIGCOMM, Kyoto, Japan
Lagutin D, Visala K, Tarkoma S (2010) Publish/subscribe for internet: PSIRP perspective. Towards Future Internet Emerg Trends Eur Res 4:75–84
Lauinger T (2010) Security & scalability of content-centric networking. Master’s thesis of Technische Universitat Darmstadt and Eurcom
Sekar V, Duffield N, Spatscheck O (2006) Lads: large-scale automated ddos detection system. In: Proceedings of the USENIX technical conference, Jun 2006
Spring N, Mahajan R, Wetherall D (2004) Measuring ISP topologies with rocketfuel. IEEE/ACM Trans Netw (TON) 12(1):2–16
The CCN project team, Named Data Networking (CCN) Project (2010) PARC Technical, Report CCN-0001, Oct 2010
Visala K, Lagutin D, Tarkoma S (2009) LANES: An inter-domain data-oriented routing architecture. In: Proceedings of the 2009 workshop on re-architecting the internet, Italy, Rome, Dec 2009
Wahlisch M, Schmidt TC, Vahlenkamp M (2013) Lessons from the past why data-driven states harm future information-centric networking. In: Proceedings of IFIP networking
Widjaja I (2012) Towards a flexible resource management system for content centric networking. In: Proceedings of the IEEE ICC
Yi C, Afanasyev A, Moiseenko I, Wang L, Zhang B, Zhang L (2013) A case for stateful forwarding plane. Comput Commun 36:779–791
Zadeh L (1965) Fuzzy sets. Inform Control 8(3):338–353
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by A. Castiglione.
This research is supported by the National Basic Research Program of China (“973 program”) (2013CB329101), the National High-Tech Research and Development Program of China (863) (2011AA010701), the National Natural Science Foundation of China (NSFC) (61232017, 61271202, 61271201, 61003283, 61102049), Beijing Natural Science Foundation (4122060, 4132053) and SRF for ROCS, SEM (W13C300010).
Rights and permissions
About this article
Cite this article
Wang, K., Zhou, H., Qin, Y. et al. Cooperative-Filter: countering Interest flooding attacks in named data networking. Soft Comput 18, 1803–1813 (2014). https://doi.org/10.1007/s00500-014-1275-z
Published:
Issue Date:
DOI: https://doi.org/10.1007/s00500-014-1275-z