Abstract
We define a nature-inspired model for entanglement optimization in the quantum Internet. The optimization model aims to maximize the entanglement fidelity and relative entropy of entanglement for the entangled connections of the entangled network structure of the quantum Internet. The cost functions are subject of a minimization defined to cover and integrate the physical attributes of entanglement transmission, purification, and storage of entanglement in quantum memories. The method can be implemented with low complexity that allows a straightforward application in the quantum Internet and quantum networking scenarios.
Similar content being viewed by others
1 Introduction
Quantum entanglement and the entangled network structure serve as fundamental concepts of the quantum Internet [1,2,3,4,5], long-distance quantum networks and future quantum communications [6,7,8,9,10,11,12,13,14,15,16,17,18,19,20,21,22]. Since the no-cloning theorem makes it impossible to use the “copy-and-resend” mechanisms of traditional repeaters [16, 23], in a quantum Internet scenario the quantum repeaters have to transmit correlations in a different way [1,2,3,4, 24]. In the entangled network structure of the quantum Internet, the main task of quantum repeaters is to distribute quantum entanglement between distant points that will then serve as a fundamental base resource for quantum teleportation and other quantum protocols [1]. Since in an experimental scenario [25,26,27,28,29,30,31] the quantum links between nodes are noisy and entanglement fidelity decreases as hop distance increases, entanglement purification is applied to improve the entanglement fidelity between nodes [1,2,3,4,5]. Quantum nodes also perform internal quantum error correction that is a requirement for reliability and storage in quantum memories [1, 4, 5, 29, 32,33,34,35,36,37,38,39,40,41,42]. Both entanglement purification and quantum error correction steps in local nodes are high-cost tasks that require significant minimization [1,2,3,4,5,6,7,8,9, 25, 26, 29,30,31, 43,44,76].
The shared entangled states between nodes form entangled connections. Significant attributes of these entangled connections are entanglement fidelity [1, 4, 5] and correlation in terms of relative entropy entanglement [68, 69]. Entanglement fidelity is a crucial parameter. It serves as the primary objective function in our model, which is a subject of maximization. Maximizing the relative entropy of entanglement is the secondary objective function. Minimizing the cost of classical communications, which is required by the entanglement optimization method as an auxiliary objective function, is also considered.
Besides these attributes, the entangled connections are characterized by the entanglement throughput that identifies the number of transmittable entangled systems per sec at a particular fidelity. In our model, the nodes are associated with an incoming entanglement throughput [1], that serves as a resource for the nodes to maximize the entanglement fidelity and the relative entropy of entanglement. The nodes receive and process the incoming entangled states. Each node performs purification and internal quantum error correction, and it stores the entangled systems in local quantum memories. The amount of input entangled systems in a node is therefore connected to the achievable maximal entanglement fidelity and correlation in the entangled states associated with that node. The objective of the proposed model is to reveal this connection and to define a framework for entanglement optimization in the quantum nodes of an arbitrary quantum network. The required input information for the optimization without loss of generality is the number of nodes, the number of fidelity types of the received entangled states, and the node characteristics. In a realistic setting, these cover the incoming entanglement throughput in a node and the costs of internal entanglement purification steps, internal quantum error corrections, and quantum memory usage.
In this work, an optimization framework for quantum networks is defined. The method aims to maximize the achievable entanglement fidelity and correlation of entangled systems, in parallel with the minimization of the cost of entanglement purification and quantum error correction steps in the quantum nodes of the network. The problem model is therefore defined as a multiobjective optimization. This paper aims to provide a model that utilizes the realistic parameters of the internal mechanisms of the nodes and the physical attributes of entanglement transmission. The proposed framework integrates the results of quantum Shannon theory, the theory of evolutionary multiobjective optimization algorithms [77, 78], and the mathematical modeling of seismic wave propagation [77,78,79,80,81,82].
Inspired by the statistical distribution of seismic events and the modeling of wave propagations in nature, the model utilizes a Poisson distribution framework to find optimal solutions in the objective space. In the theory of earthquake analysis and spatial connection theory [77,78,79,80,81,82], Poisson distributions are crucial in finding new epicenters. Motivated by these findings, a Poisson model is proposed to find new solutions in the objective space that is defined by the multiobjective optimization problem. The solutions in the objective space are represented by epicenters with several locations around them that also represent solutions in the feasible space [77, 78]. The epicenters have a magnitude and seismic power operators that determine the distributions of the locations and fitness [77, 78] of locations around the epicenters. Epicenters with low magnitude generate high seismic power in the locations, whereas epicenters with high magnitude generate low seismic power in the locations. Epicenters are generated randomly in the feasible space, and each epicenter is weighted from which the magnitude and power are derived. By a general assumption, epicenters with lower magnitude produce more locations because the locations are closer to the epicenter. The locations are placed within a certain magnitude around the epicenters in the feasible space. The optimization framework involves a set of solutions to the Pareto optimal front [77, 78] by combining the concept of Pareto dominance and seismic wave propagations. The new epicenters are determined by a Poisson distribution in analogue to prediction theory in earthquake models. The mathematical model of epicenters allows us to find new solutions iteratively and to find a global optimum. The framework has low complexity that allows an efficient practical implementation to solve the defined multiobjective optimization problem.
The multiobjective optimization problem model considers the fidelity and correlation of entanglement of entangled states available in the quantum nodes. The resources for the nodes are the incoming entangled states from the quantum links and the already stored entangled quantum systems in the local quantum memories. In the optimization procedure, both memory consumptions and environmental effects, such as entanglement purification and quantum error correction steps, are considered to develop the cost functions. In particular, the amount of resource, in terms of number of available entangled systems, is a coefficient that can be improved by increasing the incoming number of entangled systems, such as the incoming entanglement throughput in a node. In the proposed model, the incoming entanglement fidelity is further divided into some classes, which allows us to differentiate the resources in the nodes with respect to their fidelity types. Therefore, the fidelity type serves as a quality index for the optimization procedure. The optimization aims to find the optimal incoming entanglement throughput for all nodes that leads to a maximization of entanglement fidelity and correlation of entangled states with respect to the relative entropy of entanglement, for all entangled connections in the quantum network.
The novel contributions of our manuscript are as follows:
-
1.
A nature-inspired, multiobjective optimization framework is conceived for the quantum Internet.
-
2.
The model considers the physical attributes of entanglement transmission and quantum memories to provide a realistic setting (realistic objective functions and cost functions).
-
3.
The method fuses the results of quantum Shannon theory and theory of evolutionary multiobjective optimization algorithms.
-
4.
The model maximizes the entanglement fidelity and relative entropy of entanglement for all entangled connections of the network. It minimizes the cost functions to reduce the costs of entanglement purification, error correction, and quantum memory usage.
-
5.
The optimization framework allows a low-complexity implementation.
This paper is organized as follows. Section 2 presents the problem statement. Section 3 details the optimization method. Section 4 provides the problem resolution. Section 5 proposes numerical evidence. Finally, Sect. 6 concludes the paper. Supplemental material is included in the Appendix.
2 Problem statement
The problem to be solved is summarized in Problem 1.
Problem 1
For a given quantum network with N nodes, for all nodes \(x_{i} \), \(i=1,\ldots , N\), the entanglement fidelity and relative entropy of entanglement for all entangled connections are maximized, and the cost of optimal purification and quantum error correction and the cost of memory usage for all nodes are minimized.
The network model is as follows. Let \(B_{F} \left( x\right) \) be the incoming number of received entangled states (incoming entanglement throughput) in a given quantum node x, measured in the number of d-dimensional entangled states per sec at a particular entanglement fidelity F [1,2,3].
Let N be the number of nodes in the network, and let T be the number of fidelity types \(F_{j} \), \(j=1,\ldots , T\) of the entangled states in the quantum network.
Let \(B_{F}^{j} \left( x_{i} \right) \) be the number of incoming entangled states in an ith node \(x_{i} \), \(i=1,\ldots , N\), from fidelity type j. In our model, \(B_{F}^{j} \left( x_{i} \right) \) represents the utilizable resources in a particular node \(x_{i} \). Thus, the task is to determine this value for all nodes in the quantum network to maximize the fidelity and relative entropy of shared entanglement for all entangled connections.
Let \({\mathbf {X}}\) be an \(N\times T\) matrix
The matrix describes the number of entangled states of each fidelity type for all nodes in the network, \(B_{F}^{j} \left( x_{i} \right) \ge 0\) for all i and j.
2.1 Objective functions
For a given node \(x_{i} \), let \({{{\mathcal {F}}}}\left( x_{i} \right) \) be the primary objective function that identifies the cumulative entanglement fidelity (a sum of entanglement fidelities in \(x_{i} \)) after an entanglement purification \(\mathrm{P} \left( x_{i} \right) \) and an optimal quantum error correction \(\mathrm{C}\left( x_{i} \right) \) in \(x_{i} \). In our framework, \({{\mathcal {F}}_{i}}\left( {\mathbf {X}} \right) \) for a node \(x_{i} \) is defined as
where \(A_{ijk} \) is the quadratic regression coefficient, \(R_{ij} \) is the simple regression coefficient, \(c_{i} \) is a constant, and \({\tilde{B}}_{F}^{j} \left( x_{i} \right) \) is defined as
where \(\left\langle B \right\rangle _{F}^{j}\left( {{x}_{i}} \right) \) is an initialization value for \(B_{F}^{j} \left( x_{i} \right) \) in a particular node \(x_{i} \).
Then let \({\mathbb {E}}\left( {{D}_{i}}\left( {\mathbf {X}} \right) \right) \) be the secondary objective function that refers to the expected amount of cumulative relative entropy of entanglement (a sum of relative entropy of entanglement) in node \(x_{i} \), defined as
where \(A_{ijk}^{*} \), \(R_{ij}^{*} \), and \(c_{i}^{*} \) are some regression coefficients, by definition.
Therefore, the aim is to find the values of \(B_{F}^{j} \left( x_{i} \right) \) for all i and j in (1), such that \({{\mathcal {F}}_{i}}\left( {\mathbf {X}} \right) \) and \({\mathbb {E}}\left( {{D}_{i}}\left( {\mathbf {X}} \right) \right) \) are maximized for all i.
Assuming that the fidelity of entanglement is dynamically changing and evolves over time, the \(w_{j} \left( x_{i} \right) \) quantum memory coefficient is introduced for the storage of entangled states from the jth fidelity type in a node \(x_{i} \) as follows:
where \(\eta _{j} \) and \(\kappa _{j} \) are coefficients that describe the storage characteristic of entangled states with the jth fidelity type.
2.2 Cost functions
The cumulative entanglement fidelity (2) and cumulative relative entropy of entanglement (4) in a particular node \(x_{i} \) are associated with a \(f_{C} \left( \mathrm{P} \left( x_{i} \right) \right) \) cost entanglement purification \(\mathrm{P} \left( x_{i} \right) \) and a \(f_{C} \left( \mathrm{C}\left( x_{i} \right) \right) \) cost of optimal quantum error correction \(\mathrm{C}\left( x_{i} \right) \) in \(x_{i} \), where \(f_{C} \left( \cdot \right) \) is the cost function.
Then let \({\mathcal {C}}\left( {\mathbf {X}} \right) \) be the total cost function for all of the T fidelity types and for all of the N nodes, as follows:
where \(f_{j} \) is a total cost of purification and error correction associated with the jth fidelity type of entangled states.
Let \(F^{\mathrm{*}} \) be a critical fidelity on the received quantum states. The entangled states are then decomposable into two sets \({{{\mathcal {S}}}}_\mathrm{low} \) and \({{{\mathcal {S}}}}_{\mathrm{high}} \) with fidelity bounds \({{{\mathcal {S}}}}_\mathrm{low} \left( F\right) \) and \({{{\mathcal {S}}}}_{\mathrm{high}} \left( F\right) \) as
and
For the quantum systems of \({{{\mathcal {S}}}}_\mathrm{low} \), the highest fidelity is below the critical amount \(F^{\mathrm{*}} \), and for set \({{{\mathcal {S}}}}_{\mathrm{high}} \), the lowest fidelity is at least \(F^{\mathrm{*}} \). Then let \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \) and \(X_{{{{\mathcal {S}}}}_{\mathrm{high}} } \) identify the set of nodes for which condition (7) or (8) holds, respectively.
Let \({{{\mathcal {S}}}_{i}}\left( {\mathbf {X}} \right) \) be the cost of quantum memory usage in node \(x_{i} \), defined as
where \(\lambda \) is a constant, \(\alpha _{i} \) is a quality coefficient that identifies set (7) or (8) for a given node \(x_{i} \), and \(\Upsilon _{i} \) is the capacity coefficient of the quantum memory.
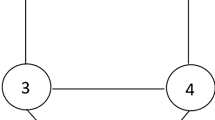
The main components of the network model are depicted in Fig. 1.
Illustration of the network model components. The quantum nodes \(x_{i} \) and \(x_{j} \) are associated with current input values \(B_{F}^{j} \left( x_{i} \right) \) and \(B_{F}^{l} \left( x_{j} \right) \) (blue and green arrows), where j and l identify the fidelity types of received entangled states. The nodes have several entangled connections (depicted by gray lines) in the network. The nodes are associated with subject functions \({{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \), \({\mathbb {E}}\left( {{D}_{i}}\left( {\mathbf {X}} \right) \right) \), and \({{{\mathcal {F}}}_{j}}\left( {\mathbf {X}} \right) \), \({\mathbb {E}}\left( {{D}_{j}}\left( {\mathbf {X}} \right) \right) \). The maximum of the received entanglement fidelity in the nodes allows the classification of the nodes to sets \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \) and \(X_{{{{\mathcal {S}}}}_{\mathrm{high}} } \): node \(x_{i} \) belongs to set \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \), whereas node \(x_{j} \) belongs to set \(X_{{{{\mathcal {S}}}}_{\mathrm{high}} } \) (depicted by dashed frames)
2.3 Multiobjective optimization
The optimization problem is as follows. The entanglement fidelity and the relative entropy of entanglement for all types of fidelity of stored entanglement for all nodes are maximized, while the cost of entanglement purification and quantum error correction is minimal, and the memory usage cost (required storage time) is also minimal. These requirements define a multiobjective optimization problem [77, 78].
Utilizing functions (2) and (4), the function subject of a maximization to yield maximal entanglement fidelity and maximal relative entropy of entanglement in all nodes of the network is defined via main objective function \({\mathcal {G}}\left( {\mathbf {X}} \right) \):
Function \({\mathcal {G}}\left( {\mathbf {X}} \right) \) should be maximized while cost functions (6) and (9) are minimized via functions \(F_{1} \left( N\right) \) and \(F_{2} \left( N\right) \):
and
with the problem constraints [77, 78] \(C_{1} \), \(C_{2} \), and \(C_{3} \) for all i and j. Constraint \(C_{1} \) is defined as
where \(\gamma \) is a cumulative lower bound on the required entanglement fidelity for all nodes, while \(\zeta \left( {\mathbf {X}} \right) \) is
and constraint \(C_{2} \) is
where \(\Lambda \) is an upper bound on the total cost function \({\mathcal {C}}\left( {\mathbf {X}} \right) \), while \(\mathrm{X}\) is
For constraint \(C_{3} \), let \(\tau _{j} \left( {\mathbf {X}} \right) \) be a differentiation of storage characteristic of entangled states from the jth fidelity type:
where
Then, \(C_{3} \) is defined as
where \(\Pi \) is an upper bound on the storage characteristic of entangled states from the jth fidelity type, while \(\nu \) is evaluated via (17) as
3 System model
This section defines the Poisson entanglement optimization method, and it is applied to the solution of the multiobjective optimization problem of Sect. 2.
3.1 Motivation and utility of the mathematical model in the quantum internet
The quantum Internet is defined as a complex network model with quantum and classical layers that involve several optimization criteria and objectives. An optimization problem model of the quantum Internet therefore induces a multiobjective optimization problem model that considers the special requirements of the environment of the quantum Internet. These requirements cover the entanglement transmission procedure, processing of quantum entanglement in the quantum nodes, and auxiliary communication through the classical links that support the entangled network structure. The quantum transmission procedure models the generation of the entangled quantum network with quantitative and qualitative measures. In this manner, a quantitative measure is the relative entropy of entanglement between the quantum nodes, while the entanglement fidelity is a qualitative measure. Classical communication could also cause an overhead in the entanglement distribution mechanism of the quantum Internet. Thus, a multiobjective optimization framework should consider the attributes of both quantum and classical layers.
To address the multiple criteria and several objectives of the quantum Internet, a multiobjective optimization framework is defined. The multiple criteria of the quantum Internet are defined as diverse objective functions that should be satisfied in parallel. The problem is therefore analogous to finding solutions in an objective space such that the objective space is defined and spanned by the input problems induced by the environment of the quantum Internet. The multiobjective optimization framework should evolve a set of solutions to the Pareto optimal front. In our model, these solutions are evolved via the mathematical model of epicenters that provide a naturally inspired answer to the multiobjective problem defined via the environment of the quantum Internet. The mathematical model of epicenters utilizes the theory of Pareto dominance in the problem resolution such that the selection and evaluation processes in the objective space that are required to identify a global optimal solution are controlled via our nature-inspired model. The proposed Poisson model ensures a robust randomization and efficient convergence in the objective space such that the solutions determined by utilizing the epicenters in the objective space will converge to a global optimal solution. The global optimal solution in the objective space represents the parallel satisfaction of the multiple criteria and objective functions defined by the quantum Internet. The randomness injected by the Poisson distribution not just avoids early convergence to a local optimal solution but also induces a fast convergence for the global optimal solution in the objective space.
Since the multiple objectives and optimization criteria of the mathematical framework are motivated by practical assumptions and considerations of the quantum Internet, the proposed mathematical model of epicenters is strongly connected with a quantum Internet scenario. As follows, the utility of the proposed multiobjective optimization framework represents an effective solution for the practical optimization problems induced by the quantum Internet.
3.2 Poisson operators
The attributes of the Poisson operator are as follows.
3.2.1 Dispersion
The \(D\left( {{{\mathcal {E}}}}\right) \) dispersion coefficient of an epicenter \({{{\mathcal {E}}}}\) (solution in the feasible space \({{{\mathcal {S}}}}_{F} \)) determines the number of affected \(L_{j} \), \(j=1,\ldots ,D\left( {{{\mathcal {E}}}}\right) \), locations around an epicenter \({{{\mathcal {E}}}}\). The random locations around an epicenter also represent solutions in \({{{\mathcal {S}}}}_{F} \) that help in increasing the diversity of population \({{{\mathcal {P}}}}\) (a set of possible solutions) to find a global optimum. The diversity increment is therefore a tool to avoid an early convergence to a local optimum [77, 78].
The dispersion \(D\left( {{{\mathcal {E}}}}_{i} \right) \) operator for an ith epicenter \({{{\mathcal {E}}}}_{i} \) is defined as
where m is a control parameter, \({{{\mathcal {E}}}}_{i} \) is an ith individual (epicenter) from the \(\left| {{\mathcal P}}\right| \) individuals (epicenters) in population \({{\mathcal P}}\), \(\left| {{{\mathcal {P}}}}\right| \) is the size of population \({{{\mathcal {P}}}}\), function \({\tilde{f}}\left( \cdot \right) \) is the fitness value (see Sect. A.2.1), \({\tilde{f}}\left( \langle {\mathcal {E}} \rangle \right) \) is a maximum objective value among the \(\left| {{{\mathcal {P}}}}\right| \) individuals, and \(\vartheta \) is a residual quantity.
Without loss of generality, assuming \(\left| {{\mathcal P}}\right| \) epicenters, the q total number of locations is as
3.2.2 Seismic power and magnitude
Assume that \(L_{j} \) is a random location around \({{\mathcal E}}_{i} \). For \(L_{j} \), the Euclidean distance \(d\left( {{{\mathcal {E}}}}_{i},l_{j} \right) \) between an ith epicenter \({{{\mathcal {E}}}}_{i} \) and the projection point \(l_{j} \) of a jth location point \(L_{j} \),\(j=1,\ldots ,D\left( {{\mathcal E}}\right) \) on the ellipsoid around \({{{\mathcal {E}}}}_{i} \) is as follows:
where \(\dim _{i} \left( \cdot \right) \) is the ith dimension of \(l_{j} \), and
where coefficients a and b define the shape of the ellipse around epicenter \({{{\mathcal {E}}}}_{i} \) (see Fig. 2), while \(\alpha _{{{{\mathcal {E}}}}_{i} } \left( l_{j} \right) \) is an angle:
The seismic power \(P\left( {{{\mathcal {E}}}}_{i},L_{j} \right) \) operator for an ith epicenter \({{{\mathcal {E}}}}_{i} \) in a jth location point \(L_{j} \),\(j=1,\ldots ,D\left( {{\mathcal E}}_{i} \right) \) is defined as
where \(b_{0} \) and \(b_{1} \) are regression coefficients, \(\sigma _{\ln P\left( {{{\mathcal {E}}}}_{j} \right) } \) is the standard deviation [82], \(M\left( {{{\mathcal {E}}}}_{i},L_{j} \right) \) is the seismic magnitude in a location \(L_{j} \), and \(l_{j} \) is the projection of \(L_{j} \) onto the ellipsoid around \({{{\mathcal {E}}}}_{i} \) [82].
Thus, at a given \(L_{j} \) with \(d\left( {{{\mathcal {E}}}}_{i},l_{j} \right) \) ((23)), from \(P\left( {{\mathcal E}}_{i},L_{j} \right) \) (see (26)), the magnitude \(M\left( {{{\mathcal {E}}}}_{i},L_{j} \right) \) between epicenter \({{{\mathcal {E}}}}_{i} \) and location \(L_{j} \) is evaluated as
3.2.3 Cumulative magnitude
Let \(L_{j}^{{{{\mathcal {E}}}}_{i} } \) be the location point where the seismic power \(P\left( {{{\mathcal {E}}}}_{i},L_{j}^{{{{\mathcal {E}}}}_{i} } \right) \) is maximal for a given epicenter \({{{\mathcal {E}}}}_{i} \). Let \(P^{\mathrm{*}} \left( {{{\mathcal {E}}}}_{i} \right) \) be the maximal seismic power,
Assuming that \(\left| {{{\mathcal {P}}}}\right| \) epicenters, \({{{\mathcal {E}}}}_{1,\ldots ,\left| {{{\mathcal {P}}}}\right| } \) exist in the system, let identify by \(P_{\max } \left( {{\mathcal E}}'\right) \) the epicenter \({{{\mathcal {E}}}}'\) with a maximal seismic power among as
with magnitude \(M\left( {{{\mathcal {E}}}}',L_{j}^{{{\mathcal E}}'} \right) \), where \(L_{j}^{{{{\mathcal {E}}}}'} \) is the location point where the seismic power \(P_{\max } \left( {{\mathcal E}}'\right) \) is maximal yielded for \({{{\mathcal {E}}}}'\).
Then the \(C\left( {{{\mathcal {E}}}}_{i} \right) \) cumulative magnitude for an epicenter \({{{\mathcal {E}}}}_{i} \) is defined as
where \({{{\mathcal {E}}}}'\) is the highest seismic power epicenter with magnitude \(M\left( {{{\mathcal {E}}}}',L_{j}^{{{\mathcal E}}'} \right) \), \({\tilde{f}}\left( {{{\mathcal {E}}}}'\right) \) is the minimum objective value among the \(\left| {{{\mathcal {P}}}}\right| \) epicenters, and \({{{\mathcal {M}}}}\) is a control parameter defined as
where \(L_{j}^{{{{\mathcal {E}}}}_{i} } \) provides the maximal seismic power for an ith epicenter \({{{\mathcal {E}}}}_{i} \), functions \({\tilde{f}}\left( {{{\mathcal {E}}}}_{i} \right) \) and \({\tilde{f}}\left( {{{\mathcal {E}}}}'\right) \) are the fitness values (see Sect. A.2.1) for the current epicenter \({{\mathcal E}}_{i} \) and for the highest seismic power epicenter \({{{\mathcal {E}}}}'\), and \(\vartheta \) is a residual quantity.
3.3 Distribution of epicenters
Assume that \({{{\mathcal {E}}}}_{i} \) is a current epicenter (solution) and \({{{\mathcal {R}}}}_{k} \) and \({{{\mathcal {R}}}}_{l} \) are two random reference points around \({{{\mathcal {E}}}}_{i} \). Using the \(C\left( {{{\mathcal {E}}}}_{i} \right) \) cumulative seismic magnitude (see (30)) of an epicenter \({{{\mathcal {E}}}}_{i} \), the generation of a new epicenter \({{{\mathcal {E}}}}_{p} \) is as follows:
Let \(\Phi \left( {{{\mathcal {E}}}}_{i},{{{\mathcal {R}}}}_{k},{{{\mathcal {R}}}}_{l} \right) \) be a Poisson range identifier function [80, 81] for \({{{\mathcal {E}}}}_{i} \) using \({{{\mathcal {R}}}}_{k} \) and \({{{\mathcal {R}}}}_{l} \) as random reference points:
where \({{{\mathcal {E}}}}_{i} \) is a current epicenter, \({{{\mathcal {R}}}}_{k} \) and \({{{\mathcal {R}}}}_{l} \) are random reference points, \(d\left( \cdot \right) \) is the Euclidean distance function, \(c_{w} \left( {{{\mathcal {E}}}}_{i},{{\mathcal R}}_{k} \right) \) and \(c_{w} \left( {{{\mathcal {R}}}}_{k},{{{\mathcal {R}}}}_{l} \right) \) are weighting coefficients between epicenters \({{{\mathcal {E}}}}_{i} \) and \({{{\mathcal {R}}}}_{k} \) and between \({{{\mathcal {R}}}}_{k} \) and \({{{\mathcal {R}}}}_{l} \), and \(\theta \left( \ell _{{{{\mathcal {E}}}}_{i},{{\mathcal R}}_{k} },\ell _{{{{\mathcal {R}}}}_{k},{{{\mathcal {R}}}}_{l} } \right) \) is the angle between lines \(\ell _{{{{\mathcal {E}}}}_{i} ,{{{\mathcal {R}}}}_{k} } \) and \(\ell _{{{{\mathcal {R}}}}_{k},{{{\mathcal {R}}}}_{l} } \):
Without loss of generality, using (32), a Poissonian distance function \({\mathfrak {D}}\left( {{{\mathcal {E}}}_{p}} \right) \) for the finding of new epicenter \({{{\mathcal {E}}}}_{p} \) is defined via a P Poisson distribution [80, 81] as follows:
where
with mean
Therefore, the resulting new epicenter \({{{\mathcal {E}}}}_{p} \) is a Poisson random epicenter \({{{\mathcal {E}}}}_{p} \) with a Poisson range identifier \({\mathfrak {D}}\left( {{{\mathcal {E}}}_{p}} \right) \).
For a large set of reference points, only those reference points that are within the \(r\left( {{{\mathcal {E}}}}_{i} \right) \) radius around the current solution \({{{\mathcal {E}}}}_{i} \) are selected for the determination of the new solution \({{{\mathcal {E}}}}_{p} \). This radius is defined as
where \(\tilde{{M}}\) is the average magnitude,
\(Q_{1} \) and \(Q_{2} \) are constants, and \(\chi \) is a normalization term. Motivated by the corresponding seismologic relations of the Dobrovolsky–Megathrust radius formula [81], the constants in (37) are selected as \(Q_{1} =0.414\) and \(Q_{2} =1.696\).
In the relevance range \(r\left( {{{\mathcal {E}}}}_{i} \right) \) of (37), the weights of reference points are determined by the seismic power function (26).
3.4 Population diversity
3.4.1 Hypocentral
The hypocentral of an epicenter is aimed to increase the diversity of population by a randomization.
Let \(\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) \) be an actual randomly selected kth dimension and \(k=1,\ldots ,\dim \left( {{{\mathcal {E}}}}_{i} \right) \) be a current epicenter \({{{\mathcal {E}}}}_{i} \), \(i=1,\ldots ,\left| {{{\mathcal {P}}}}\right| \). The \({{{\mathcal {H}}}}\left( \dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) \right) \) hypocentral provides a random displacement [80, 81] of \(\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) \) using \(C\left( {{{\mathcal {E}}}}_{i} \right) \) (see (30)):
where \({{{\mathcal {U}}}}\left( -C\left( {{{\mathcal {E}}}}_{i} \right) ,C\left( {{{\mathcal {E}}}}_{i} \right) \right) \) is a uniform random number from the range of \(\left[ -C\left( {{\mathcal E}}_{i} \right) , C\left( {{{\mathcal {E}}}}_{i} \right) \right] \) to yield the displacement \(\dim _{k} \left( {{{\mathcal {E}}}}_{i'} \right) \), \(M\left( \dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) ,L_{j}^{\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) } \right) \) is the magnitude, and \(L_{j}^{\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) } \) is a location point where \(P\left( \dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) ,L_{j}^{\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) } \right) \) is maximal for \(\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) \).
The \(D\left( {{{\mathcal {E}}}}_{i} \right) \) locations around the cumulative magnitude \(C\left( {{{\mathcal {E}}}}_{i} \right) \) of \({{{\mathcal {E}}}}_{i} \) are generated by (39) through all the randomly selected Y dimensions, where Y is as follows [77, 78]:
The process is repeated for all \({{{\mathcal {E}}}}_{i} \).
3.4.2 Poisson randomization
To generate random locations around \(\dim _{k} \left( {{\mathcal E}}_{i} \right) \), a Poisson distribution is also used to increase the diversity of the population. A random location in the kth dimension \(L_{r}^{\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) } \) around \(\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) \) is generated as follows:
where
is a Poisson random number with distribution coefficients k and \(\lambda \). Given that it is possible that using (41) some randomly generated locations will be out of the feasible space \({{{\mathcal {S}}}}_{F} \), a normalization operator \(\mathrm{N} \left( \cdot \right) \) of \(L_{r}^{\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) } \) is defined to keep the new locations around \(\dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) \) in \({{{\mathcal {S}}}}_{F} \), as follows [77, 78]:
where \(B_\mathrm{low}^{k} \) and \(B_{up}^{k} \) are lower and upper bounds on the boundaries of locations in a kth dimension, and \(\bmod (\cdot )\) is to a modular arithmetic function. The procedure is repeated for the randomly selected \(t={{{\mathcal {U}}}}\left( 1,\dim \left( {{{\mathcal {E}}}}_{i} \right) \right) \) dimensions of \({{{\mathcal {E}}}}_{i} \), for \(\forall i\).
3.5 Iterative convergence
The method of convergence of solutions in the Poisson optimization is summarized in Method 1.

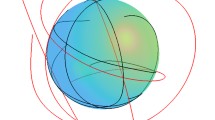
An epicenter \({{{\mathcal {E}}}}_{i} \) and the generation of a new solution \({{{\mathcal {E}}}}_{p} \) in the objective space \(\mathrm{S}_{O} \) are depicted in Fig. 2. The ellipsoid around \({{{\mathcal {E}}}}_{i} \) and the projection point \(l_{k} \) of the reference location \({{{\mathcal {R}}}}_{k} \) are serving the determination of power function \(P\left( {{{\mathcal {E}}}}_{i},{{{\mathcal {R}}}}_{k} \right) \) in the reference location \({{\mathcal R}}_{k} \).
A new epicenter \({{{\mathcal {E}}}}_{p} \) is determined via the Poisson function \({\mathfrak {D}}\left( {{{\mathcal {E}}}_{p}} \right) \). Locations with low power function (26) values have high magnitudes (27) from the epicenter, whereas locations with high power function values have low magnitudes from the epicenter.
Iteration step of the Poisson optimization model in the objective space \(\mathrm{S}_{O} \). An ith epicenter, \({{{\mathcal {E}}}}_{i} \) (depicted by the red dot), with a projected point \(l_{k} \) of random reference location \({{{\mathcal {R}}}}_{k} \). Reference locations \({{{\mathcal {R}}}}_{k} \) and \({{\mathcal R}}_{l} \) (blue dots) identify locations \(L_{k} \) and \(L_{l} \), respectively. The power in \({{{\mathcal {R}}}}_{k} \) is \(P\left( {{{\mathcal {E}}}}_{i},{{{\mathcal {R}}}}_{k} \right) \) (see (26)), while the magnitude is \(M\left( {{{\mathcal {E}}}}_{i},{{{\mathcal {R}}}}_{k} \right) \) (see (27)). Notation \(\dim _{i} \left( \cdot \right) \) refers to the ith dimension of \(l_{k} \), and coefficients a and b define the shape of the ellipse (yellow) around epicenter \({{{\mathcal {E}}}}_{i} \). The \({{{\mathcal {H}}}}\left( \dim _{k} \left( {{{\mathcal {E}}}}_{i} \right) \right) \) hypocentral of \({{{\mathcal {E}}}}_{i} \) is determined via the range of the \(C\left( {{{\mathcal {E}}}}_{i} \right) \) cumulative magnitude (depicted by the green circle). The new epicenter \({{{\mathcal {E}}}}_{p} \) (depicted by the green dot) is determined by the \({\mathfrak {D}}\left( {{{\mathcal {E}}}_{p}} \right) \) Poisson distance function using \({{{\mathcal {R}}}}_{k} \) and \({{{\mathcal {R}}}}_{l} \), with angle \(\theta \left( \ell _{{{{\mathcal {E}}}}_{i},{{{\mathcal {R}}}}_{k} },\ell _{{{{\mathcal {R}}}}_{k},{{{\mathcal {R}}}}_{l} } \right) \) between lines \(\ell _{{{{\mathcal {E}}}}_{i},{{{\mathcal {R}}}}_{k} } \) and \(\ell _{{{{\mathcal {R}}}}_{k},{{{\mathcal {R}}}}_{l} } \) (Color figure online)
3.6 Framework
The algorithmical framework that utilizes the Poisson entanglement optimization method for the problem statement presented in Sect. 2 is defined in Algorithm 1.

Sub-procedure 1 of step 5 is discussed in the Appendix.
3.6.1 Optimization of classical communications
To achieve the minimization of classical communications required by the entanglement optimization, the S-metric (or hypervolume indicator) is integrated, which is a quality measure for the solutions or a contribution of a single solution in a solution set [77, 78]. By definition, this metric identifies the size of dominated space (size of space covered).
By theory, the \(S\left( {{{\mathcal {R}}}}\right) \) S-metric for a solution set \({{{\mathcal {R}}}}=\left\{ r_{1},\ldots ,r_{n} \right\} \) is as follows:
where \({{{\mathcal {L}}}}\) is a Lebesgue measure, notation \(b\angle a\) means a dominates b (or b is dominated by a), and \(x_{ref} \) is a reference point dominated by all valid solutions in the solution set [77, 78].
For a given solution \(r_{i} \), the S-metric identifies the size of space dominated by \(r_{i} \) but not dominated by any other solution, without loss of generality as:
In the optimization of classical communications, the existence of two objective functions is assumed. The first objective function, \(f_{1} \), is associated with the minimization of the cost of the first type of classical communications related to the reception and storage of entangled systems in the quantum nodes. (It covers the classical communications related to the required entanglement throughput by the nodes, fidelity of received entanglement, number of stored entangled states, and fidelity parameters.) Thus,
where \({{{\mathcal {C}}}}_{1} \left( x_{i} \right) \) is the cost associated with the first type of classical communications related to a \(x_{i} \).
The second objective function, \(f_{2} \), is associated with the cost of the second type of classical communications that is related to entanglement purification:
where \({{{\mathcal {C}}}}_{2} \left( x_{i} \right) \) is the cost associated with the second type of classical communications with respect to \(x_{i} \).
Assuming objective functions \(f_{1} \) and \(f_{2} \), the \(S\left( r_{i} \right) \) of a particular solution \(r_{i} \) is as follows:
Given that the S-metric is calculated for the solutions, a set of nearest neighbors that restrict the space can be determined. Since the volume of this space can be quantified by the hypervolume, the solutions that satisfy objectives \(f_{1} \) and \(f_{2} \) can be found by utilizing (48).
3.7 Computational complexity
The computational complexity of the Poissonian optimization method is derived as follows. Given that \(\left| {{{\mathcal {P}}}}\right| \) epicenters are generated in the search space and that the number of locations for an ith epicenter \({{{\mathcal {E}}}}_{i} \) is determined by the dispersion operator \(D\left( {{{\mathcal {E}}}}_{i} \right) \), the resulting computational complexity at a total number of locations \(q=\sum _{i=1}^{\left| {{\mathcal P}}\right| }D\left( {{{\mathcal {E}}}}_{i} \right) \) (see (22)) is
since after a sorting process the locations for a given epicenter \({{{\mathcal {E}}}}_{i} \) can be calculated with complexity \({{{\mathcal {O}}}}\left( D\left( {{{\mathcal {E}}}}_{i} \right) \right) \), where d is the number of objectives.
Considering that in our setting \(d=2\), the total complexity is
4 Problem resolution
The resolution of the problem shown in Sect. 2 using the Poissonian entanglement optimization framework of Sect. 3 is as follows.
Let \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \) be a set of nodes for which condition (7) holds for the fidelity of the received entangled states in the nodes, and let \(X_{{{\mathcal S}}_{\mathrm{high}} } \) be a set of nodes for which condition (8) holds for the received fidelity entanglement.
Then let \(\left| X_{{{{\mathcal {S}}}}_\mathrm{low} } \right| \) and \(\left| X_{{{{\mathcal {S}}}}_{\mathrm{high}} } \right| \) be the cardinality of \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \) and \(X_{{{{\mathcal {S}}}}_{\mathrm{high}} } \), respectively.
Specifically, function (10) for the \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \)-type nodes is rewritten as
where \({{{\mathcal {F}}}}_{i}^{X_{{{{\mathcal {S}}}}_\mathrm{low} } } \left( X\right) \) is the entanglement fidelity function for an ith \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \)-type node \(x_{i} \), \(x_{i} \in X_{{{{\mathcal {S}}}}_\mathrm{low} } \), and \({\mathbb {E}}\left( D_{i}^{{{X}_{{{{\mathcal {S}}}_\mathrm{low}}}}}\left( {\mathbf {X}} \right) \right) \) is the expected relative entropy of entanglement in an ith \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \)-type \(x_{i} \).
Similarly, for the \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \)-type nodes, function (10) is as follows:
From (51) and (52), a cumulative \({{{\mathcal {G}}}^{{{X}_{{{{\mathcal {S}}}_{\mathrm{high}}}}}\otimes {{X}_{{{{\mathcal {S}}}_{\mathrm{high}}}}}}}\left( {\mathbf {X}} \right) \) is defined as
where \(A_{i} \) refers to the number of received entangled systems in an ith node, while
The fidelity types of the available resource states in the nodes should be further divided into T classes. The final function is then evaluated as
where
Thus,
where \({{\nu }_{{\mathbf {X}}}}\left( {{\varphi }_{i}} \right) =\sum \limits _{j=1}^{Z}{{{\tau }_{j}}\left( {{\varphi }_{i}} \right) } \), \(\gamma \) is given by the constraint of (13), while \(\Pi \) is given by the constraint of (19).
4.1 Convergence of solutions
Let \({{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \in \left[ 0,1\right] \) be the objective function that refers to the resulting entanglement fidelity in a particular node \(x_{i} \), after purification and quantum error correction with per-node cost functions \(F_{1}^{i} \left( {\mathbf {X}} \right) \), and \(F_{2}^{i} \left( {\mathbf {X}} \right) \), respectively.
Precisely, a current ith epicenter \({{{\mathcal {E}}}}_{i} \) identifies a solution in the objective space \(\mathrm{S}_{O}\),
The random locations around \({{{\mathcal {E}}}}_{i} \) also represent possible solutions. Let \({{{\mathcal {E}}}}^{\mathrm{*}} \) be an optimal solution in the \(\mathrm{S}_{O} \) subject space, which maximizes \({{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \) and minimizes \(F_{1}^{i} \left( {\mathbf {X}} \right) \) and \(F_{2}^{i} \left( {\mathbf {X}} \right) \). From \({{{\mathcal {E}}}}_{i} \), the algorithm determines a new solution (epicenter) \({{\mathcal E}}_{p} \) via the \({\mathfrak {D}}\left( {{{\mathcal {E}}}_{p}} \right) \) Poisson distance function, using the connection model between the locations around \({{{\mathcal {E}}}}_{i} \). To improve the diversity, locations around \({{{\mathcal {E}}}}_{p} \) are generated. The new epicenter \({{{\mathcal {E}}}}_{p} \) converges to an optimal solution \({{{\mathcal {E}}}}^{\mathrm{*}} \). The iterations are repeated until \({{{\mathcal {E}}}}^{\mathrm{*}} \) is not found or until a stopping criterion is met.
The iteration from a current solution \({{{\mathcal {E}}}}_{i} \) to a new solution \({{{\mathcal {E}}}}_{p} \) toward a global optimal \({{{\mathcal {E}}}}^{\mathrm{*}} \) in \(\mathrm{S}_{O} \) is illustrated in Fig. 3.
Distribution of solutions for entanglement fidelity maximization in the objective space \(\mathrm{S}_{O} :\left\{ F_{1}^{i} \left( N\right) ,F_{2}^{i} \left( N\right) ,{{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \right\} \) of the entanglement optimization problem (cost functions \(F_{1} \left( N\right) \) and \(F_{2} \left( N\right) \) and the objective function \({{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \) are normalized onto the range of \(\left[ 0,1\right] \)). a A random epicenter \({{{\mathcal {E}}}}_{i} \) refers to a current solution (depicted by the red dot) with the Poisson distributed reference locations (the reference points are not real solutions). The random reference locations are clustered into two classes: (1) reference locations within radius \(r\left( {{{\mathcal {E}}}}_{i} \right) \) around \({{{\mathcal {E}}}}_{i} \) and (2) reference locations outside the radius (depicted by the gray dots). Reference locations outside the range are neglected in the iteration. b A new epicenter \({{{\mathcal {E}}}}_{p} \) (depicted by the green dot) is determined via the connection model of relevant reference points (e.g., lie inside the range of \(r\left( {{{\mathcal {E}}}}_{i} \right) \)), which yields the \({\mathfrak {D}}\left( {{{\mathcal {E}}}_{p}} \right) \) Poisson distance function. The new solution, \({{{\mathcal {E}}}}_{p} \), converges toward an optimal solution \({{{\mathcal {E}}}}^{\mathrm{*}} \) (depicted by the purple dot). The reference locations inside the relevance region are weighted by the seismic power function (Color figure online)
5 Numerical evidence
In this section, a numerical evidence is proposed to demonstrate the Poisson entanglement optimization method.
5.1 Decision making
To demonstrate the results of Sect. 4, let \({{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \) be the object function subject to maximize. The problem is to determine a matrix \({\mathbf {X}}\) that maximizes \({{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \), and also \({\mathbb {E}}\left( D_{i}^{{{N}_{{{{\mathcal {S}}}_\mathrm{low}}}}}\left( {\mathbf {X}} \right) \right) \), and minimizes the cost functions \(F_{1}^{i} \left( N\right) \) and \(F_{1}^{i} \left( N\right) \). Thus, for each node N, the optimal number of received and stored entangled systems should be determined, with high and low fidelity classes.
Particularly, finding an optimal solution \({{{\mathcal {E}}}}^{\mathrm{*}} \) in \(\mathrm{S}_{O} \) with the assumptions given in Sect. 4 therefore means the selection of the optimal objective function (e.g., maximizing the entanglement fidelity \({{{\mathcal {F}}}_{i}}\left( {\mathbf {X}} \right) \) or maximizing the relative entropy of entanglement \({\mathbb {E}}\left( D_{i}^{{{N}_{{{{\mathcal {S}}}_\mathrm{low}}}}}\left( {\mathbf {X}} \right) \right) \)), in particular node types \(X_{{{{\mathcal {S}}}}_\mathrm{low} } \) and \(X_{{{{\mathcal {S}}}}_{\mathrm{high}} } \), while all cost functions are minimized in the quantum network.
A solution set in \(\mathrm{S}_{O} \) is depicted in Fig. 4.
An optimal solution \({{{\mathcal {E}}}}^{\mathrm{*}} \) in \(\mathrm{S}_{O} \) therefore yields the maximization of entanglement fidelity \({{{\mathcal {F}}}}_{N} \left( X\right) \) if a particular node N belongs to the class \(N_{{{{\mathcal {S}}}}_{\mathrm{high}} } \), whereas it maximizes the relative entropy of entanglement \({\mathbb {E}}\left( D_{i}^{{{N}_{{{{\mathcal {S}}}_\mathrm{low}}}}}\left( {\mathbf {X}} \right) \right) \) if N belongs to the class \(N_{{{{\mathcal {S}}}}_\mathrm{low} } \). Increasing \(B_{F}^{j} \left( x_{i} \right) \) for a \(N_{{{{\mathcal {S}}}}_{\mathrm{high}} } \)-class node and then performing an optimal purification and quantum error correction could significantly improve the fidelity of entanglement. On the other hand, for a \(N_{{{{\mathcal {S}}}}_\mathrm{low} } \)-class node, the fidelity improvement at an optimal purification and quantum error correction is insignificant. Thus, incrementing \(B_{F}^{j} \left( x_{i} \right) \) does not lead to a significant improvement in the fidelity. The optimal solution for these nodes is to focus on improving the relative entropy of entanglement, which requires lower cost function values.
This decision strategy provides a global optimal with respect to all quantum nodes of the quantum network.
The decision making is illustrated in Fig. 5. In Fig. 5a, the F entanglement fidelity is depicted in function of \(F_{1}^{i} \left( N\right) \) for \(N_{{{\mathcal S}}_\mathrm{low} } \) and \(N_{{{{\mathcal {S}}}}_{\mathrm{high}} } \) nodes. In Fig. 5b, the D relative entropy of entanglement is depicted in function of \(F_{1}^{i} \left( N\right) \) for \(N_{{{{\mathcal {S}}}}_\mathrm{low} } \) and \(N_{{{{\mathcal {S}}}}_{\mathrm{high}} } \) nodes. The initial values of F and D are assumed to be equal for a given class, while the value of \(F_{2}^{i} \left( N\right) \) is set to constant for illustration purposes.
For an \(N_{{{{\mathcal {S}}}}_{\mathrm{high}} } \) node, the increment of \(F_{1}^{i} \left( N\right) \) leads to significant improvement in F, while the increment in D is moderate. For an \(N_{{{\mathcal S}}_\mathrm{low} } \) node, the increment of \(F_{1}^{i} \left( N\right) \) leads to moderate improvement in F, while the improvement in D is significant. As a corollary, the increment of the entanglement throughput is a useful approach to increase the entanglement fidelity for the \(X_{{{{\mathcal {S}}}}_{\mathrm{high}} } \) set, and to boost the relative entropy of entanglement in the \(X_{{{\mathcal S}}_\mathrm{low} } \) set.
Illustration of the decision making. a The F entanglement fidelity values in function of \(F_{1}^{i} \left( N\right) \) for \(N_{{{{\mathcal {S}}}}_\mathrm{low} } \) (red line) and \(N_{{{{\mathcal {S}}}}_{\mathrm{high}} } \) (blue line) nodes. The value of \(F_{2}^{i} \left( N\right) \) is set to constant. b The D relative entropy of entanglement values in function of \(F_{1}^{i} \left( N\right) \) for \(N_{{{{\mathcal {S}}}}_\mathrm{low} } \) (red line) and \(N_{{{{\mathcal {S}}}}_{\mathrm{high}} } \)(blue line) nodes. The value of \(F_{2}^{i} \left( N\right) \) is set to constant (Color figure online)
5.2 Distribution of solutions
First, we analyze the distribution of solutions in the feasible space \({{{\mathcal {S}}}}_{F} \) focusing on the magnitudes associated to the locations around epicenters.
Let us assume that the total number of q locations (see (22)) can be divided into m magnitude ranges [79], such that
where \(n_{i} \) is the number of locations belonging to an ith magnitude range, \(\left| {{{\mathcal {P}}}}\right| \) is the population size. Then let \(M_{i} \) be the magnitude associated to the ith magnitude range. Then a \({\tilde{n}}_{i} \) approximation of \(n_{i} \) is evaluated as
where \(f\left( \cdot \right) \) is a fitting function. To give an estimate on \(n_{i} \) at a particular magnitude \(M_{i} \), we utilize a power law distribution [79] function \({{\mathcal B}}\left( n_{i} \right) \) for a log-scaled \(n_{i} \), as
where \({\tilde{M}}_{i} \) is a log-scaled \(M_{i} \), while a and b are constants [79].
Then, the \({\tilde{n}}_{i} \) Poisson estimate is yielded as
where \(\sigma _{i}^{2} \) is the observational variance, while \(\lambda _{i} \) is the mean of a Poisson distribution. Since the sum of independent Poisson variables is also a Poisson variable with mean equals to the sum of the components means,
where \(\lambda \left( q\right) \) is the mean total number, while \(\lambda _{i} \) is an ith component mean. Using the Poisson property \(\sigma ^{2} =\lambda \), the \(\sigma _{q}^{2} \) estimated uncertainty is yielded as [79] \(\sigma _{q}^{2} =\lambda \left( q\right) =\sum _{i=1}^{m}f\left( {\tilde{M}}_{i} \right) \). Thus using a corresponding fitting function \(f\left( \cdot \right) \), the mean and the variance of the total number of events are equal to the sum of the fitted values.
In our model the distribution of the log-scaled \({\tilde{n}}_{i} =\lambda _{i} \) values in function of \(M_{i} \) is well approachable by the power law distribution \({{{\mathcal {B}}}}\left( \lambda _{i} \right) :\log _{10} \left( \lambda _{i} \right) =a-b{\tilde{M}}_{i} \), while the distribution of the \(\lambda \left( q\right) \) total number (64) of locations is approachable by a \({{{\mathcal {N}}}}\left( \lambda \left( q\right) ,\sigma _{{{\mathcal N}}}^{2} \right) \), Gaussian distribution with variance \(\sigma _{{{{\mathcal {N}}}}}^{2} =\lambda \left( q\right) \) as \(\lambda \left( q\right) \rightarrow \infty \), by theory.
The distributions of \({{{\mathcal {B}}}}\left( \lambda _{i} \right) \) in function of the magnitude \(M_{i} \) and coefficient b are illustrated in Fig. 6.
The distributions of \(\lambda \left( q\right) \) (see (64)) for \(k_{it} \) iterations are depicted in Fig. 7. In Fig. 7a, \(\lambda \left( q\right) =10^{2} \), while Fig. 7b illustrated the distribution at \(\lambda \left( q\right) =10^{6} \). As \(\lambda \left( q\right) \rightarrow \infty \), the distributions of \(\lambda \left( q\right) \) can be approximated by a \({{{\mathcal {N}}}}\left( \lambda \left( q\right) ,\sigma _{{{{\mathcal {N}}}}}^{2} \right) \), \(\sigma _{{{{\mathcal {N}}}}}^{2} =\lambda \left( q\right) \) Gaussian distribution.
The associated distributions of \({{{\mathcal {B}}}}\left( \lambda _{i} \right) \) for the values of \(\lambda \left( q\right) \) are depicted in Fig. 8. The maximum value of \({{\mathcal B}}\left( \lambda _{i} \right) \) is selected to \({{\mathcal B}}\left( \lambda _{i} \right) \approx 10\) in each cases which values are picked up at \(\lambda \left( q\right) \), where \(\lambda \left( q\right) =10^{2} \) in Fig. 8a, and \(\lambda \left( q\right) =10^{6} \) in Fig. 8b. The \({{\mathcal B}}\left( \lambda _{i} \right) \) values approximates to a Gaussian distribution. The statistical distribution of \({{\mathcal B}}\left( \lambda _{i} \right) \) is therefore constitutes a similar pattern for arbitrary \(\lambda \left( q\right) \).
6 Conclusions
We defined an optimization framework for the transmission and processing of quantum entanglement in the entangled network structure of the quantum Internet. The proposed Poissonian entanglement optimization framework fuses the fundamental concepts of quantum Shannon theory with the theory of evolutionary algorithms and seismic wave propagations. Two objective functions are defined, with primary focus on the entanglement fidelity and secondary focus on the relative entropy of entanglement. As an additional objective function, the minimization of classical communications required by the entanglement optimization procedure is considered. The cost functions are defined to cover the physical attributes of entanglement transmission, purification, and storage in quantum memories. This method can be implemented with low complexity that allows a straightforward application in future quantum Internet and quantum networking scenarios.
References
Van Meter, R.: Quantum Networking. Wiley, ISBN:1118648927, 9781118648926 (2014)
Lloyd, S., Shapiro, J.H., Wong, F.N.C., Kumar, P., Shahriar, S.M., Yuen, H.P.: Infrastructure for the quantum internet. ACM SIGCOMM Comput. Commun. Rev. 34(5), 9–20 (2004)
Kimble, H.J.: The quantum internet. Nature 453, 1023–1030 (2008)
Van Meter, R., Ladd, T.D., Munro, W.J., Nemoto, K.: System design for a long-line quantum repeater. IEEE/ACM Trans. Netw. 17(3), 1002–1013 (2009)
Van Meter, R., Satoh, T., Ladd, T.D., Munro, W.J., Nemoto, K.: Path selection for quantum repeater networks. Netw. Sci. 3(1–4), 82–95 (2013)
Gyongyosi, L., Imre, S.: Decentralized base-graph routing for the quantum internet. Phys. Rev. A Am. Phys. Soc. (2018). https://doi.org/10.1103/PhysRevA.98.022310
Gyongyosi, L., Imre, S.: Dynamic topology resilience for quantum networks. In: Proceedings SPIE 10547, Advances in Photonics of Quantum Computing, Memory, and Communication XI, 105470Z (22 February 2018) (2018). https://doi.org/10.1117/12.2288707
Gyongyosi, L., Imre, S.: Topology Adaption for the Quantum Internet, Quantum Information Processing. Springer, Berlin (2018). https://doi.org/10.1007/s11128-018-2064-x
Pirandola, S., Laurenza, R., Ottaviani, C., Banchi, L.: Fundamental limits of repeaterless quantum communications. Nat. Commun. (2017). https://doi.org/10.1038/ncomms15043
Pirandola, S., Braunstein, S.L., Laurenza, R., Ottaviani, C., Cope, T.P.W., Spedalieri, G., Banchi, L.: Theory of channel simulation and bounds for private communication. Quantum Sci. Technol. 3, 035009 (2018)
Laurenza, R., Pirandola, S.: General bounds for sender-receiver capacities in multipoint quantum communications. Phys. Rev. A 96, 032318 (2017)
Pirandola, S.: Capacities of repeater-assisted quantum communications (2016). arXiv:1601.00966
Gyongyosi, L., Imre, S.: Multilayer optimization for the quantum internet. Sci. Rep. (2018). https://doi.org/10.1038/s41598-018-30957-x
Gyongyosi, L., Imre, S.: Entanglement availability differentiation service for the quantum internet. Sci. Rep. (2018). https://doi.org/10.1038/s41598-018-28801-3
Gyongyosi, L., Imre, S.: Entanglement-gradient routing for quantum networks. Sci. Rep. (2017). https://doi.org/10.1038/s41598-017-14394-w
Imre, S., Gyongyosi, L.: Advanced Quantum Communications—An Engineering Approach. Wiley-IEEE Press, Hoboken, NJ (2013)
Caleffi, M.: End-to-end entanglement rate: toward a quantum route metric. In: 2017 IEEE Globecom (2018). https://doi.org/10.1109/GLOCOMW.2017.8269080
Caleffi, M.: Optimal routing for quantum networks. IEEE Access (2017). https://doi.org/10.1109/ACCESS.2017.2763325
Caleffi, M., Cacciapuoti, A.S., Bianchi, G.: Quantum internet: from communication to distributed computing (2018). arXiv:1805.04360
Castelvecchi, D.: The quantum internet has arrived. Nature, News and Comment (2018). https://www.nature.com/articles/d41586-018-01835-3
Cacciapuoti, A.S., Caleffi, M., Tafuri, F., Cataliotti, F.S., Gherardini, S., Bianchi, G.: Quantum internet: networking challenges in distributed quantum computing (2018). arXiv:1810.08421
Bacsardi, L.: On the way to quantum-based satellite communication. IEEE Commun. Mag. 51(08), 50–55 (2013)
Petz, D.: Quantum Information Theory and Quantum Statistics. Springer, Heidelberg (2008)
Gyongyosi, L., Imre, S., Nguyen, H.V.: A survey on quantum channel capacities. IEEE Commun. Surv. Tutor. 99, 1 (2018). https://doi.org/10.1109/COMST.2017.2786748
Xiao, Y.F., Gong, Q.: Optical microcavity: from fundamental physics to functional photonics devices. Sci. Bull. 61(3), 185–186 (2016)
Zhang, W., et al.: Quantum secure direct communication with quantum memory. Phys. Rev. Lett. 118, 220501 (2017)
Biamonte, J., et al.: Quantum machine learning. Nature 549, 195–202 (2017)
Lloyd, S., Mohseni, M., Rebentrost, P.: Quantum algorithms for supervised and unsupervised machine learning (2013). arXiv:1307.0411
Chou, C., Laurat, J., Deng, H., Choi, K.S., de Riedmatten, H., Felinto, D., Kimble, H.J.: Functional quantum nodes for entanglement distribution over scalable quantum networks. Science 316(5829), 1316–1320 (2007)
Sheng, Y.B., Zhou, L.: Distributed secure quantum machine learning. Sci. Bull. 62, 1025–1029 (2017)
Kok, P., Munro, W.J., Nemoto, K., Ralph, T.C., Dowling, J.P., Milburn, G.J.: Linear optical quantum computing with photonic qubits. Rev. Mod. Phys. 79, 135–174 (2007)
Gyongyosi, L., Imre, S.: A Poisson model for entanglement optimization in the quantum Internet. In: Proceedings of Quantum Information Science, Sensing, and Computation X; vol. 10660, 106600C (2018). https://doi.org/10.1117/12.2309416 (2018)
Shor, P.W.: Scheme for reducing decoherence in quantum computer memory. Phys. Rev. A 52, R2493–R2496 (1995)
Muralidharan, S., Kim, J., Lutkenhaus, N., Lukin, M.D., Jiang, L.: Ultrafast and fault-tolerant quantum communication across long distances. Phys. Rev. Lett. 112, 250501 (2014)
Yuan, Z., Chen, Y., Zhao, B., Chen, S., Schmiedmayer, J., Pan, J.W.: Experimental demonstration of a BDCZ quantum repeater node. Nature 454, 1098–1101 (2008)
Kobayashi, H., Le Gall, F., Nishimura, H., Rotteler, M.: General Scheme for Perfect Quantum Network Coding with Free Classical Communication. Lecture Notes in Computer Science (Automata, Languages and Programming SE-52, vol. 5555, pp. 622–633. Springer, Berlin (2009)
Hayashi, M.: Prior entanglement between senders enables perfect quantum network coding with modification. Phys. Rev. A 76, 040301(R) (2007)
Hayashi, M., Iwama, K., Nishimura, H., Raymond, R., Yamashita, S.: Quantum Network Coding. In: Thomas, W., Weil, P. (eds.) Lecture Notes in Computer Science (STACS 2007 SE52 vol. 4393). Springer, Berlin (2007)
Chen, L., Hayashi, M.: Multicopy and stochastic transformation of multipartite pure states. Phys. Rev. A 83(2), 022331 (2011)
Schoute, E., Mancinska, L., Islam, T., Kerenidis, I., Wehner, S.: Shortcuts to quantum network routing (2016). arXiv:1610.05238
Lloyd, S., Weedbrook, C.: Quantum generative adversarial learning. Phys. Rev. Lett. 121 (2018) arXiv:1804.09139
Gisin, N., Thew, R.: Quantum communication. Nat. Photon. 1, 165–171 (2007)
Zou, Z.Z., Yu, X.T., Zhang, Z.C.: Quantum connectivity optimization algorithms for entanglement source deployment in a quantum multi-hop network. Front. Phys. 13(2), 130202 (2018)
Xiong, P.Y., Yu, X.T., Zhang, Z.C., et al.: Routing protocol for wireless quantum multi-hop mesh backbone network based on partially entangled GHZ state. Front. Phys. 12(4), 120302 (2017)
Farouk, A., Batle, J., Elhoseny, M., et al.: Robust general N user authentication scheme in a centralized quantum communication network via generalized GHZ states. Front. Phys. 13(2), 130306 (2018)
Wang, Z., Zhang, C., Huang, Y.F., et al.: Experimental verification of genuine multipartite entanglement without shared reference frames. Sci. Bull. 61(9), 714–719 (2016)
Deng, F.G., Ren, B.C., Li, X.H.: Quantum hyperentanglement and its applications in quantum information processing. Sci. Bull. 62(1), 46–68 (2017)
Zhu, F., Zhang, W., Sheng, Y., et al.: Experimental long-distance quantum secure direct communication. Sci. Bull. 62(22), 1519–1524 (2017)
Van Meter, R., Devitt, S.J.: Local and distributed quantum computation. IEEE Comput. 49(9), 31–42 (2016)
Lloyd, S., Mohseni, M., Rebentrost, P.: Quantum principal component analysis. Nat. Phys. 10, 631 (2014)
Lloyd, S.: Capacity of the noisy quantum channel. Phys. Rev. A 55, 1613–1622 (1997)
Lloyd, S.: The universe as quantum computer. In: Zenil, H. (ed.) A Computable Universe: Understanding and Exploring Nature as Computation. World Scientific, Singapore (2013). arXiv:1312.4455v1
Zhang, W., et al.: Quantum secure direct communication with quantum memory. Phys. Rev. Lett. 118, 220501 (2017)
Enk, S.J., Cirac, J.I., Zoller, P.: Photonic channels for quantum communication. Science 279, 205–208 (1998)
Briegel, H.J., Dur, W., Cirac, J.I., Zoller, P.: Quantum repeaters: the role of imperfect local operations in quantum communication. Phys. Rev. Lett. 81, 5932–5935 (1998)
Dur, W., Briegel, H.J., Cirac, J.I., Zoller, P.: Quantum repeaters based on entanglement purification. Phys. Rev. A 59, 169–181 (1999)
Duan, L.M., Lukin, M.D., Cirac, J.I., Zoller, P.: Long-distance quantum communication with atomic ensembles and linear optics. Nature 414, 413–418 (2001)
Van Loock, P., Ladd, T.D., Sanaka, K., Yamaguchi, F., Nemoto, K., Munro, W.J., Yamamoto, Y.: Hybrid quantum repeater using bright coherent light. Phys. Rev. Lett. 96, 240501 (2006)
Zhao, B., Chen, Z.B., Chen, Y.A., Schmiedmayer, J., Pan, J.W.: Robust creation of entanglement between remote memory qubits. Phys. Rev. Lett. 98, 240502 (2007)
Goebel, A.M., Wagenknecht, G., Zhang, Q., Chen, Y., Chen, K., Schmiedmayer, J., Pan, J.W.: Multistage entanglement swapping. Phys. Rev. Lett. 101, 080403 (2008)
Simon, C., de Riedmatten, H., Afzelius, M., Sangouard, N., Zbinden, H., Gisin, N.: Quantum repeaters with photon pair sources and multimode memories. Phys. Rev. Lett. 98, 190503 (2007)
Tittel, W., Afzelius, M., Chaneliere, T., Cone, R.L., Kroll, S., Moiseev, S.A., Sellars, M.: Photon-echo quantum memory in solid state systems. Laser Photon. Rev. 4, 244–267 (2009)
Sangouard, N., Dubessy, R., Simon, C.: Quantum repeaters based on single trapped ions. Phys. Rev. A 79, 042340 (2009)
Dur, W., Briegel, H.J.: Entanglement purification and quantum error correction. Rep. Prog. Phys 70, 1381–1424 (2007)
Sheng, Y.B., Zhou, L.: Distributed secure quantum machine learning. Sci. Bull. 62, 1025–1029 (2017)
Leung, D., Oppenheim, J., Winter, A.: Quantum network communication-the butterfly and beyond. IEEE Trans. Inf. Theory 56, 3478–90 (2010)
Kobayashi, H., Le Gall, F., Nishimura, H., Rotteler, M.: Perfect quantum network communication protocol based on classical network coding. In: Proceedings of 2010 IEEE International Symposium on Information Theory (ISIT), pp. 2686–2290 (2010)
Vedral, V., Plenio, M.B., Rippin, M.A., Knight, P.L.: Quantifying entanglement. Phys. Rev. Lett. 78, 2275–2279 (1997)
Vedral, V.: The role of relative entropy in quantum information theory. Rev. Mod. Phys. 74, 197–234 (2002)
Long, G.-L., Liu, X.-S.: Theoretically efficient high-capacity quantum-key-distribution scheme. Phys. Rev. A 65(3), 032302 (2002)
Zhao, L.J., Guo, Y.M., Li-Jost, X., et al.: Quantum nonlocality can be distributed via separable states. Sci. China Phys. Mech. Astron. 61(7), 070321 (2018)
Zhang, K.J., Zhang, L., Song, T.T., et al.: A potential application in quantum networks-deterministic quantum operation sharing schemes with Bell states. Sci. China Phys. Mech. Astron. 59(6), 660302 (2018)
Ye, T.Y., Ji, Z.X.: Multi-user quantum private comparison with scattered preparation and one-way convergent transmission of quantum states. Sci. China Phys. Mech. Astron. 60(9), 090312 (2017)
Hu, J.Y., Yu, B., Jing, M.Y., et al.: Experimental quantum secure direct communication with single photons. Light: Sci. Appl. 5(9), e16144 (2016)
Wang, K., Yu, X.T., Lu, S.L., et al.: Quantum wireless multihop communication based on arbitrary Bell pairs and teleportation. Phys. Rev. A 89(2), 022329 (2014)
Yu, X.T., Xu, J., Zhang, Z.C.: Distributed wireless quantum communication networks. Chin. Phys. B 22(9), 090311 (2013)
Tan, Y.: Fireworks Algorithm. A Novel Swarm Intelligence Optimization Method. Springer, Berlin (2015)
Zheng, Y.J., Song, Q., Chen, S.Y.: Multiobjective fireworks optimization for variable-rate fertilization in oil crop production. Appl. Soft Comput. 13(11), 4253–4263 (2013)
Greenhough, J., Main, I.G.: A Poisson model for earthquake frequency uncertainties in seismic hazard analysis (2008). https://doi.org/10.1029/2008GL035353. arXiv:0807.2396v2
Kannan, S.: Improving innovative mathematical model for earthquake prediction. J. Geol. Geosci. (2014). https://doi.org/10.4172/2329-6755.1000168
Mejia, J., Rojas, K., Aleza, N., Villagracia, A.R.: Earthquake prediction through Kannan-mathematical-model analysis and Dobrovolsky-based clustering Technique. In: DLSU Research Congress 2015 (2015)
Stamatovska, S.G.: The latest mathematical models of earthquake ground motion. In: Kanao, M. (ed.) Seismic Waves—Research and Analysis. InTech (2012)
Acknowledgements
Open access funding provided by Budapest University of Technology and Economics (BME). This work was partially supported by the European Research Council through the Advanced Fellow Grant, in part by the Royal Society’s Wolfson Research Merit Award, in part by the Engineering and Physical Sciences Research Council under Grant EP/L018659/1, by the Hungarian Scientific Research Fund—OTKA K-112125, and by the National Research Development and Innovation Office of Hungary (Project No. 2017-1.2.1-NKP-2017-00001), and in part by the BME Artificial Intelligence FIKP grant of EMMI (BME FIKP-MI/SC).
Author information
Authors and Affiliations
Contributions
LGY designed the protocol and wrote the manuscript. LGY and SI analyzed the results. All authors reviewed the manuscript.
Ethics declarations
Ethics statement
This work did not involve any active collection of human data.
Data accessibility statement
This work does not have any experimental data.
Conflict of interest
We have no competing interests.
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
L. Gyongyosi: Parts of this work were presented in conference proceedings [8].
Appendix
Appendix
1.1 Definitions
1.1.1 Entanglement Fidelity
Let
be the target Bell state subject to be created at the end of the entanglement distribution procedure. The entanglement fidelity F at an actually created noisy quantum system \(\sigma \) is
where F is a value between 0 and 1, \(F=1\) for a perfect Bell state and \(F<1\) for an imperfect state. The fidelity for two pure quantum states is defined as
The fidelity of quantum states can describe the relation of a pure channel input state \(|\psi \rangle \) and the received mixed quantum system \(\sigma =\sum _{i=0}^{n-1} p_{i} \rho _{i} =\sum _{i=0}^{n-1} p_{i} | \psi _{i} \rangle \langle \psi _{i} | \) at the channel output as
Fidelity can also be defined for mixed states \(\sigma \) and \(\rho \)
1.1.2 Relative Entropy of Entanglement
By definition, the \(E(\rho )\) relative entropy of entanglement function of a joint state \(\rho \) of subsystems A and B is defined by the \(D( \cdot \Vert \cdot )\) quantum relative entropy function, without loss of generality as
where \(\rho _{AB} \) is the set of separable states \(\rho _{AB}=\sum _{i=1}^{n} p_{i} \rho _{A,i} \otimes \rho _{B,i} \).
1.2 Evaluation of Solutions
1.2.1 Fitness Function
To evaluate the performance of the epicenters we utilize a mathematical apparatus based on the Pareto strength and fitness assignment [77, 78]. Let \(\Pr \left( {{\mathcal E}}_{i} \right) \) be the probability of selection of an epicenter \({{\mathcal E}}_{i} \), defined as
where \(\kappa \left( {{\mathcal E}}_{i} \right) \) is the sum of \(d\left( \cdot \right) \) Euclidean distances between \({{\mathcal E}}_{i} \) and the other epicenters, as
where K is a set with cardinality
where \(D\left( {{\mathcal E}}_{i} \right) \) is given in (21), and \(l\in K\) refers to that the position of \({{\mathcal E}}_{j} \) belongs to set K, and \(\left| {{\mathcal P}}\right| \) is the population size. Let \({{\mathcal N}{\mathcal P}}\) refer to the non-dominated solution archive, and let
refer to the selected epicenter, i.e, to an individual solution in \({{\mathcal P}}\) or in \({{\mathcal N}{\mathcal P}}\).
Let \(\Phi \left( \varphi _{i} \right) \) be a strength coefficient for solution \(\varphi _{i} \), defined as
where \(\angle \) refers to the Pareto dominance relation between \(\varphi _{i} \) and \(\varphi _{k} ={{\mathcal E}}_{k} \). As follows, (A.11) depends on the number of individuals it dominates, by theory [77, 78].
By definition, a decision vector \(\mathbf {A}\) dominates a vector \(\mathbf {B}\), i.e., \(\mathbf {B}\angle \mathbf {A}\), if
for \(\forall i\), \(i=1,\ldots ,m\) and for at least one j with i, \(j=1,\ldots ,n\),
where \(f:{{\mathbb {R}}^{m}}\rightarrow {{\mathbb {R}}^{n}}\). The set of non-dominated decision vectors in \({{\mathbb {R}}}^{n} \) is called a Pareto optimal set, while the image under f in the solution space is called the Pareto front [77, 78]. In a multiobjective optimization the aim is to achieve the best Pareto front, by theory.
Using (A.11), let \(\alpha \left( \varphi _{i} \right) \) be the raw fitness value of \(\varphi _{i} \) evaluated by the \(\Phi \left( \cdot \right) \) strength function (see (A.11)) of its dominators as
with an inverse distance function (referred to as the density value of \(\varphi _{i} \)), \(\rho \left( \varphi _{i} \right) \) as
where \(d_{g} \left( \varphi _{i} \right) \) is the distance from solution \(\varphi _{i} \) to its \(g^{th} \) nearest individual, where g is initialized as the square root of the sample size \(\left| {{\mathcal P}}\bigcup {{\mathcal N}{\mathcal P}}\right| \), by theory [77, 78].
Using (A.15), a for a random solution \(r\left( \varphi _{i} \right) \) the \(\tilde{f}\left( \cdot \right) \) fitness function of \(\varphi _{i} \) is as
Then let p refer to the number of selected \(\varphi _{i} \) solutions in \({{\mathcal P}}\). Using (A.16), the selection probability of each solution is yielded as
1.2.2 Constraints
As a solution \(\varphi _{i} \) does not satisfy the problem constraints \(C_{1} \), \(C_{2} \), \(C_{3} \), a \(\mathrm{H} ^{C_{z} } \left( \varphi _{i} \right) \), \(z=1,2,3\) degrees of violation are defined for the constraints.
For constraint \(C_{1} \) (see (13)), the \(\mathrm{H} ^{C_{1} } \left( \varphi _{i} \right) \) violation function [77, 78] is as
where
For constraint \(C_{2} \) (see (15)), the \(\mathrm{H} ^{C_{2} } \left( \varphi _{i} \right) \) violation function is as follows
where
For constraint \(C_{3} \) (see (19)), the \(\mathrm{H} ^{C_{3} } \left( \varphi _{i} \right) \) violation function is as
where
From (A.18), (A.20) and (A.22) a penalty coefficient \(\partial \left( \varphi _{i} \right) \) is defined as
where \(w_{i} \)-s are weighting coefficients [77, 78].
1.2.3 Selection Condition
Assuming that there are \(\chi \) number of selected random solutions such that the selection probabilities are proportional to their fitness values. The selection of a solution \(\varphi _{i} \) is as follows.
First from the selected random solutions a mutant solution \(\hbar _{i} \) is generated as
where \(r_{i} \in \left\{ a,\ldots p\right\} \) are the random indexes, while \(\vartheta >0\) is a coefficient.
From the components of \(\hbar _{i} \) a trial solution \(\mathrm{T} _{i} \) is defined with a \(j^{th} \) component \(\mathrm{T} _{i}^{\left( j\right) } \) as
where \(r\left( 0,1\right) \) is a random number from the range \(\left[ 0,1\right] \), \(r\left( i\right) \) is a random integer within \(\left( 0,X\right] \) for each i, while \(P_{cross} \) is the crossover probability ranged in \(\left( 0,1\right) \).
Then the selection of the solution \(\varphi _{i} \) using the trial solution \(\mathrm{T} _{i} \) is as
where function \(\tilde{f}\left( \cdot \right) \) is given in (A.16).
1.3 Sub-Procedure 1
The Sub-procedure 1 of Algorithm 1 is as follows [77, 78].

1.4 Notations
The notations of the manuscript are summarized in Table 1.
Rights and permissions
Open Access This article is distributed under the terms of the Creative Commons Attribution 4.0 International License (http://creativecommons.org/licenses/by/4.0/), which permits unrestricted use, distribution, and reproduction in any medium, provided you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons license, and indicate if changes were made.
About this article
Cite this article
Gyongyosi, L., Imre, S. A Poisson Model for Entanglement Optimization in the Quantum Internet. Quantum Inf Process 18, 233 (2019). https://doi.org/10.1007/s11128-019-2335-1
Received:
Accepted:
Published:
DOI: https://doi.org/10.1007/s11128-019-2335-1